Quite a few well-liked Android apps available in Google Perform Keep are vulnerable to a path traversal-affiliated vulnerability that could be exploited by a destructive application to overwrite arbitrary files in the vulnerable app’s residence listing.
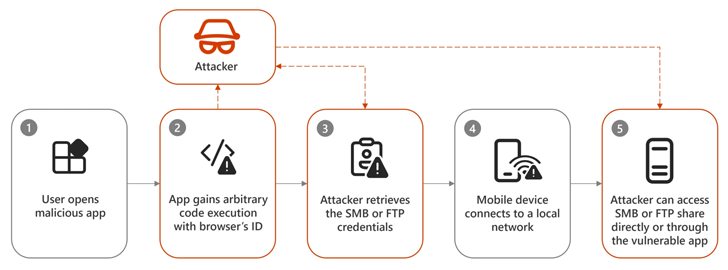
“The implications of this vulnerability pattern contain arbitrary code execution and token theft, based on an application’s implementation,” Dimitrios Valsamaras of the Microsoft Menace Intelligence workforce stated in a report published Wednesday.
Profitable exploitation could allow for an attacker to take full control of the application’s conduct and leverage the stolen tokens to achieve unauthorized entry to the victim’s on-line accounts and other info.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

Two of the applications that had been located vulnerable to the dilemma are as follows –
- Xiaomi File Supervisor (com.mi. Android.globalFileexplorer) – Over 1 billion installs
- WPS Business (cn.wps.moffice_eng) – More than 500 million installs
Even though Android implements isolation by assigning every single software its own dedicated information and memory space, it gives what is actually termed a material company to facilitate knowledge and file sharing concerning apps in a protected method. But implementation oversights could allow bypassing of examine/publish constraints within just an application’s household directory.
“This information company-based design presents a properly-outlined file-sharing system, enabling a serving application to share its files with other programs in a protected way with fine-grained regulate,” Valsamaras explained.
“Even so, we have usually encountered conditions the place the consuming application isn’t going to validate the material of the file that it receives and, most regarding, it utilizes the filename offered by the serving application to cache the been given file within the consuming application’s inner data directory.”
This pitfall can have major repercussions when a serving app declares a malicious variation of the FileProvider course in purchase to help file sharing between applications, and finally cause the consuming application to overwrite critical data files in its personal knowledge area.
Put in a different way, the mechanism normally takes benefit of the simple fact that the consuming application blindly trusts the input to send arbitrary payloads with a specific filename by suggests of a tailor made, express intent and without the need of the user’s knowledge or consent, foremost to code execution.
As a consequence, this could allow an attacker to overwrite the concentrate on app’s shared preferences file and make it connect with a server under their command to exfiltrate sensitive details.

A further situation consists of apps that load indigenous libraries from its individual facts directory (as a substitute of “/details/application-lib”), in which circumstance a rogue app could exploit the aforementioned weakness to overwrite a native library with destructive code that will get executed when the library is loaded.
Pursuing accountable disclosure, equally Xiaomi and WPS Workplace have rectified the issue as of February 2024. Microsoft, on the other hand, explained the issue could be more commonplace, requiring that builders consider measures to test their apps for identical issues.
Google has also posted its own advice on the issue, urging developers to thoroughly take care of the filename delivered by the server application.
“When the customer software writes the gained file to storage, it should disregard the filename offered by the server software and alternatively use its individual internally created exclusive identifier as the filename,” Google said. “If making a distinctive filename is not practical, the customer application ought to sanitize the supplied filename.”
Discovered this write-up exciting? Abide by us on Twitter and LinkedIn to browse much more exclusive articles we post.
Some areas of this write-up are sourced from:
thehackernews.com


 Ukrainian REvil Hacker Sentenced to 13 Years and Ordered to Pay $16 Million
Ukrainian REvil Hacker Sentenced to 13 Years and Ordered to Pay $16 Million