The latest wave of cyber attacks focusing on Albanian companies involved the use of a wiper referred to as No-Justice.
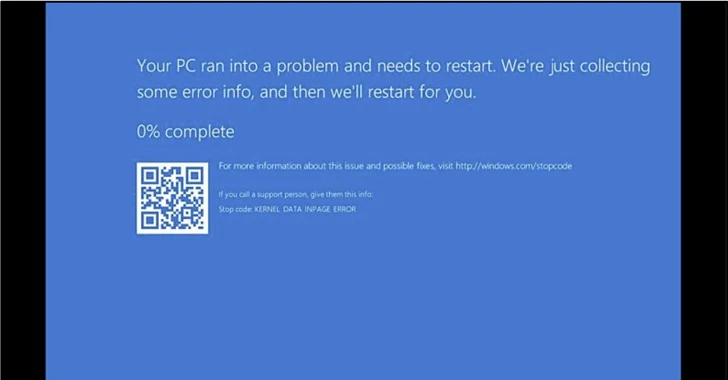
The findings occur from cybersecurity firm ClearSky, which explained the Windows-primarily based malware “crashes the operating process in a way that it are not able to be rebooted.”
The intrusions have been attributed to an Iranian “psychological operation team” named Homeland Justice, which has been operating considering the fact that July 2022, specially orchestrating damaging attacks against Albania.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
On December 24, 2023, the adversary resurfaced right after a hiatus, stating it is “again to ruin supporters of terrorists,” describing its hottest campaign as #DestroyDurresMilitaryCamp. The Albanian town of Durrës at this time hosts the dissident team People’s Mojahedin Business of Iran (MEK).
Targets of the attack incorporated Just one Albania, Eagle Mobile Albania, Air Albania, and the Albanian parliament.
Two of the principal equipment deployed during the marketing campaign incorporate an executable wiper and a PowerShell script that’s built to propagate the former to other equipment in the target network following enabling Windows Remote Administration (WinRM).

The No-Justice wiper (NACL.exe) is a 220.34 KB binary that needs administrator privileges to erase the details on the computer.
This is accomplished by taking away the boot signature from the Master Boot Document (MBR), which refers to the initial sector of any tricky disk that identifies in which the functioning method is located in the disk so that it can be loaded into a computer’s RAM.
Also shipped around the study course of the attack are legitimate applications like Plink (aka PuTTY Backlink), RevSocks, and the Windows 2000 useful resource package to aid reconnaissance, lateral movement, and persistent remote accessibility.
The enhancement comes as pro-Iranian danger actors this kind of as Cyber Av3ngers, Cyber Toufan, Haghjoyan, and YareGomnam Team have more and more established their sights on Israel and the U.S. amid continuing geopolitical tensions in the Center East.
“Groups such as Cyber Av3ngers and Cyber Toufan appear to be adopting a narrative of retaliation in their cyber attacks,” Verify Position disclosed final month.
“By opportunistically concentrating on U.S. entities applying Israeli technology, these hacktivist proxies check out to attain a twin retaliation strategy – saying to target the two Israel and the U.S. in a solitary, orchestrated cyber assault.”

Cyber Toufan, in specific, has been linked to a deluge of hack-and-leak operations concentrating on in excess of 100 organizations, wiping infected hosts and releasing stolen details on their Telegram channel.
“They have brought about so much problems that lots of of the orgs – almost a third, in point, haven’t been capable to recuperate,” security researcher Kevin Beaumont explained. “Some of these are even now fully offline more than a month later on, and the wiped victims are a combine of private businesses and Israeli condition governing administration entities.”
Past month, the Israel Nationwide Cyber Directorate (INCD) stated it really is at this time tracking approximately 15 hacker teams linked with Iran, Hamas, and Hezbollah that are maliciously working in Israeli cyberspace due to the fact the onset of the Israel-Hamas war in Oct 2023.
The agency further more observed that the strategies and techniques utilized share similarities with people applied in the Ukraine-Russia war, leveraging psychological warfare and wiper malware to damage details.
Uncovered this write-up appealing? Comply with us on Twitter and LinkedIn to browse more unique articles we publish.
Some elements of this article are sourced from:
thehackernews.com


 SpectralBlur: New macOS Backdoor Threat from North Korean Hackers
SpectralBlur: New macOS Backdoor Threat from North Korean Hackers