Security Configuration Assessment (SCA) is critical to an organization’s cybersecurity technique. SCA aims to discover vulnerabilities and misconfigurations that destructive actors exploit to achieve unauthorized access to methods and knowledge. Regular security configuration assessments are essential in preserving a secure and compliant environment, as this minimizes the risk of cyber attacks. The assessment supplies insight into your current security posture by executing configuration baseline checks on providers and apps operating on critical techniques.
How SCA functions
SCA is executed by checking the configurations of your IT assets versus recognized benchmarks this sort of as the Heart for Internet Security (CIS) benchmark and compliance criteria this kind of as NIST, GDPR, and HIPPA. Regulatory benchmarks supply a international benchmark for greatest tactics to assist businesses greatly enhance their IT cleanliness and increase consumer rely on. The CIS benchmark supplies a guideline for most effective practices for security configuration and has recommendations for numerous seller merchandise.
The configuration details from the focus on endpoints are gathered and as opposed from the established baseline making use of regarded benchmarks this kind of as CIS and NIST to determine misconfigurations. The recognized exceptions might lead to exploitable vulnerabilities or weaken the endpoint’s all round security posture.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
The report created by the evaluation identifies configuration issues and supplies descriptions and rationale for the recognized issues with mitigation actions. This report aids security analysts in implementing the important variations and updates to deliver methods and configurations in line with the safe baseline. This may possibly contain altering options, patching vulnerabilities, or disabling pointless companies.
Why SCA is vital
Security Configuration Evaluation (SCA) is a critical follow in cybersecurity that aims to boost the security posture of IT property. Listed here are some key advantages of conducting security configuration assessments:
- Identifying vulnerabilities – Determining vulnerabilities in procedure configurations permits companies to just take proactive methods to stop cyber attacks.
- Lowering attack surface area area – SCA aids to lower the attack area place of an corporation by identifying attack vectors such as unneeded services, open ports, or extremely permissive settings. With the assistance of SCA, businesses can discover and limit their attack vectors.
- Complying with regulatory requirements lets companies to evaluate and carry out compliance with regulatory benchmarks, ideal practices, and inside security guidelines. SCA can help guarantee that units are configured according to these criteria (PCI-DSS, HIPAA, NIST, TSC, CIS), lowering the risk of non-compliance.
- Enhancing IT hygiene – By frequently examining and addressing configuration gaps, corporations can improve their IT hygiene and minimize the likelihood of cyber attacks. SCA identifies configuration gaps and delivers security analyst insights on how to reinforce technique defenses and increase the total security posture of the firm.
- Reducing human mistake – SCA allows detect and rectify configuration problems created by administrators, lowering the risk of accidental security breaches. Misconfiguration is one of the typical brings about of security incidents, SCA enables early detection of configuration issues.

Security Configuration Evaluation with Wazuh
Wazuh is a absolutely free, open supply security platform that presents unified XDR and SIEM abilities across workloads on cloud and on-premises environments. It gives a centralized perspective for monitoring, detecting, and alerting security functions occurring on monitored endpoints and cloud workloads.
The Wazuh SCA module performs scans to detect misconfigurations on monitored endpoints and advise remediation actions. All those scans evaluate the configuration of the endpoints working with policy data files that include checks to be analyzed in opposition to the true configuration of the endpoint. This capability can help you deal with your attack surface area efficiently to make improvements to your security posture.
Rewards of working with Wazuh SCA module
Wazuh SCA module provides the adhering to added benefits:
- Ongoing checking – With a complete and ongoing SCA scan, misconfigurations and process weaknesses are simply determined in functioning techniques and programs mounted on your endpoints. Wazuh lets you to develop tailor made procedures that scan endpoints and verify if they conform to your organization’s guidelines.
- Overall flexibility – Organizations can conveniently perform SCA scans on a lot of equipment with various working units and purposes. Wazuh SCA capability is enabled by default on monitored endpoints. This permits security analysts to know the existing degree of security hardening on just about every endpoint monitored by Wazuh. Security teams can use the Wazuh SCA capability to make sure coverage and protected configurations for your remote endpoints in a rapidly-increasing setting.
- Compliance monitoring – The Wazuh SCA module performs frequent checks on monitored endpoints, making certain compliance with PCI DSS, HIPAA, NIST, TSC, CIS, and other pertinent specifications. It allows corporations to assess and implement compliance with regulatory standards, most effective practices, and inner security policies. It also assures compliance with your company’s inside policies/baselines.
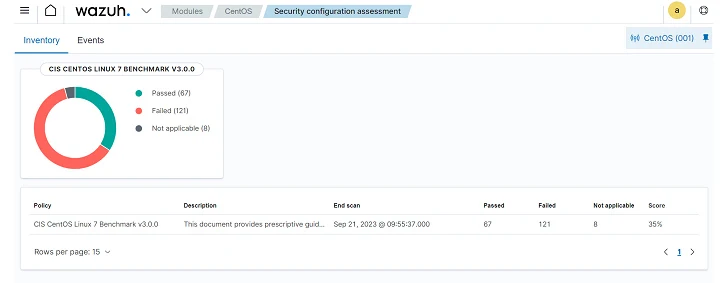
- Reporting – Wazuh generates comprehensive experiences of checks carried out on your endpoint. Wazuh SCA studies incorporate discovered vulnerabilities, compliance gaps, and remediation actions to protected your endpoints. Also, the Wazuh dashboard has a Security configuration assessment module that permits you to see SCA scan outcomes for every agent. You can choose clear, actionable measures to guarantee compliance, safe process configurations, and strengthen IT hygiene.
- Multi-system assistance – The Wazuh SCA module supports and has SCA policies for numerous working systems and services these types of as Linux, Windows, macOS, Solaris, AIX, HP-UX, Microsoft SQL, PostgreSQL, Oracle database, NGINX, Apache, and far more.
Summary
Security configuration evaluation is a essential ingredient of a detailed cybersecurity system and risk administration. Standard SCA scans can assistance an firm to proactively recognize misconfigurations and system flaws, mitigate configuration-linked pitfalls, and cut down their attack surface. Having a effectively-documented and secure configuration baseline permits corporations to understand the affect of an incident better and recuperate more quickly. As a result of frequent SCA scans, corporations can adhere to regulatory necessities by identifying and repairing exceptions. This boosts an organization’s popularity with consumers, associates, and stakeholders, instilling have confidence in in the security of its methods.
The Wazuh SCA module allows people conduct security checks in opposition to monitored endpoints to strengthen their total security posture in a regularly switching danger landscape. Choose the to start with step in procedure hardening by working with the Wazuh SCA module to look at for exposures and misconfigurations in your endpoints.
Be part of the Wazuh neighborhood to get started out.
Observed this report exciting? Observe us on Twitter and LinkedIn to go through additional exceptional written content we publish.
Some components of this write-up are sourced from:
thehackernews.com


 Researcher Reveal New Technique to Bypass Cloudflare’s Firewall and DDoS Protection
Researcher Reveal New Technique to Bypass Cloudflare’s Firewall and DDoS Protection