The open-resource distant obtain trojan recognised as Quasar RAT has been observed leveraging DLL facet-loading to fly below the radar and stealthily siphon information from compromised Windows hosts.
“This method capitalizes on the inherent have faith in these files command inside of the Windows natural environment,” Uptycs scientists Tejaswini Sandapolla and Karthickkumar Kathiresan mentioned in a report released final 7 days, detailing the malware’s reliance on ctfmon.exe and calc.exe as element of the attack chain.
Also recognized by the names CinaRAT or Yggdrasil, Quasar RAT is a C#-based remote administration tool able of accumulating process information, a listing of managing programs, data files, keystrokes, screenshots, and executing arbitrary shell instructions.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

DLL facet-loading is a popular procedure adopted by many threat actors to execute their possess payloads by planting a spoofed DLL file with a title that a benign executable is recognized to be seeking for.
“Adversaries likely use facet-loading as a usually means of masking steps they perform less than a genuine, trustworthy, and potentially elevated program or software program method,” MITRE notes in its explanation of the attack strategy.
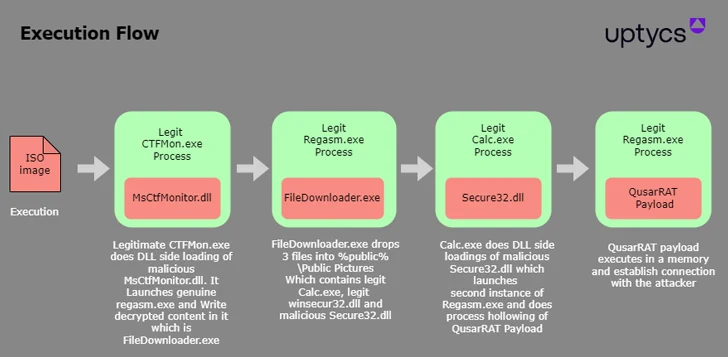
The commencing issue of the attack documented by Uptycs is an ISO graphic file that includes 3 data files: A genuine binary named ctfmon.exe that’s renamed as eBill-997358806.exe, a MsCtfMonitor.dll file that is renamed as observe.ini, and a malicious MsCtfMonitor.dll.
“When the binary file ‘eBill-997358806.exe’ is run, it initiates the loading of a file titled ‘MsCtfMonitor.dll’ (name masqueraded) by way of DLL side-loading strategy, within just which malicious code is hid,” the researchers stated.

The hidden code is an additional executable “FileDownloader.exe” that is injected into Regasm.exe, the Windows Assembly Registration Device, in order to launch the future stage, an reliable calc.exe file that loads the rogue Secure32.dll yet again through DLL side-loading and start the final Quasar RAT payload.
The trojan, for its part, establishes connections with a remote server to send method data and even sets up a reverse proxy for distant obtain to the endpoint.
The identification of the danger actor and the precise initial accessibility vector employed to pull off the attack is unclear, but it really is probably to be disseminated by suggests of phishing email messages, creating it essential that buyers be on the guard for doubtful e-mail, inbound links, or attachments.
Observed this short article intriguing? Follow us on Twitter and LinkedIn to go through extra distinctive written content we write-up.
Some sections of this short article are sourced from:
thehackernews.com


 Europol Dismantles Ragnar Locker Ransomware Infrastructure, Nabs Key Developer
Europol Dismantles Ragnar Locker Ransomware Infrastructure, Nabs Key Developer