Ransomware has emerged as the only cryptocurrency-dependent crime to develop in 2023, with cybercriminals extorting just about $175.8 million extra than they did a year in the past, according to results from Chainalysis.
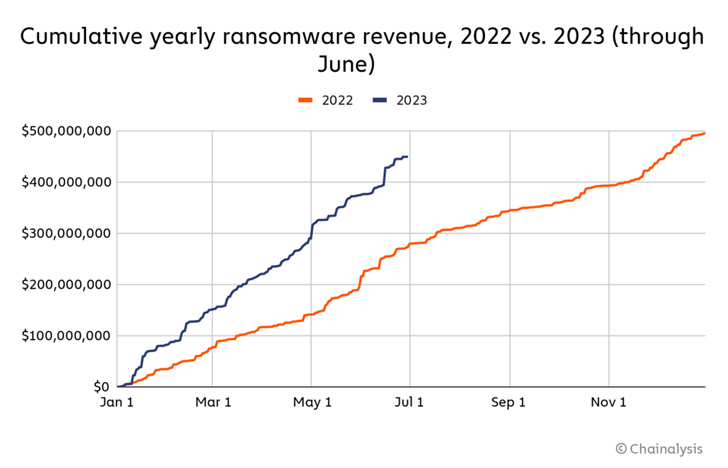
“Ransomware attackers are on speed for their 2nd-most important 12 months ever, owning extorted at the very least $449.1 million by means of June,” the blockchain analytics agency explained in a midyear crypto crime report shared with The Hacker News. “If this rate carries on, ransomware attackers will extort $898.6 million from victims in 2023, trailing only 2021’s $939.9 million.”
In contrast, crypto ripoffs have pulled in 77% much less income than they did through June of 2022, mostly driven by the abrupt exit of VidiLook, which pays users VDL tokens in return for viewing digital ads that then can be exchanged for huge benefits. So have the inflows to illicit addresses linked with malware, darknet markets, little one abuse product, and fraud outlets.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
The advancement, subsequent a drop in ransomware revenues in 2022, marks a reversal of sorts, with Chainalysis attributing it to the return of big recreation looking just after a downturn previous yr and the increasing number of successful compact attacks carried by groups like Dharma and Phobos.
On the other conclusion of the spectrum lie highly developed groups like Cl0p (or Clop), BlackCat, and Black Basta, which tend to be additional selective in their focusing on, whilst also putting greater companies to need higher ransoms. Cl0p’s typical payment measurement for the very first 50 percent of 2023 stands at $1,730,486, in contrast to Dharma’s $275.
Cl0p, in particular, has been on a rampage in latest months, exploiting security flaws in MOVEit Transfer application to breach 257 companies across the world to day, for each Emsisoft researcher Brett Callow. Additional than 17.7 million men and women are claimed to be impacted as a consequence of the ransomware attacks.
“Clop’s preference for focusing on more substantial providers (>$5 million/yr revenue) and capitalizing on more recent-but-disclosed vulnerabilities has been the principal driver of its achievement in the to start with 50 percent of 2023,” Sophos researcher David Wallace reported in a report previously this 7 days, contacting the group a “loud, adaptable, persistent participant.”
Impending WEBINARShield In opposition to Insider Threats: Master SaaS Security Posture Administration
Nervous about insider threats? We’ve bought you included! Be part of this webinar to explore useful tactics and the techniques of proactive security with SaaS Security Posture Management.
Join Now
Whilst regulation enforcement initiatives to actively go after ransomware groups and sanction products and services featuring cashout providers, coupled with the availability of decryptors, have emboldened victims to not fork out up, it’s suspected that the craze “may be prompting ransomware attackers to raise the dimensions of their ransom calls for” to extract funds from firms who are still ready to settle.
Past but not minimum, the Russia-Ukraine War is also reported to have been a contributing factor to the decrease in ransomware attacks in 2022, producing the Conti procedure to shut store right after declaring assistance for Russia.
“The conflict possible displaced ransomware operators and diverted them absent from monetarily impressed cyber intrusions,” Chainalysis mentioned. “It stands to purpose that the conflict disrupted ransomware operators’ potential to conduct attacks or maybe even their mandate for this kind of attacks,” specifically considering that a bulk of ransomware actors are tied to Russia.
Identified this post intriguing? Comply with us on Twitter and LinkedIn to examine extra exceptional information we article.
Some sections of this article are sourced from:
thehackernews.com


 The Risks and Preventions of AI in Business: Safeguarding Against Potential Pitfalls
The Risks and Preventions of AI in Business: Safeguarding Against Potential Pitfalls