Well-liked video clip conferencing application Zoom has tackled quite a few security vulnerabilities, two of which impact its Linux client that could have authorized an attacker with entry to a compromised process to go through and exfiltrate Zoom consumer data—and even run stealthy malware as a sub-method of a trustworthy application.
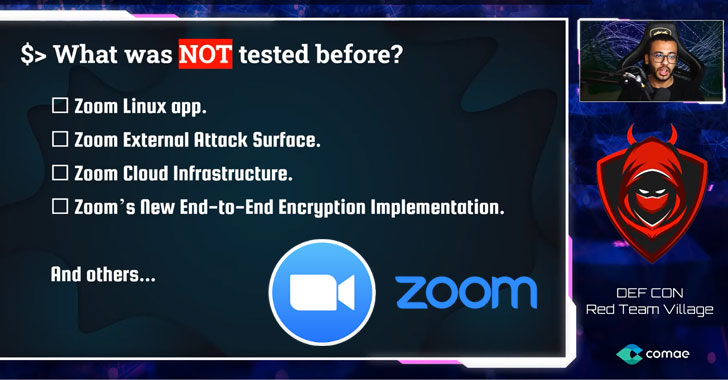
According to cybersecurity researcher Mazin Ahmed, who introduced his findings at DEF CON 2020 yesterday, the corporation also still left a misconfigured progress occasion exposed that wasn’t updated due to the fact September 2019, indicating the server could be inclined to flaws that have been remaining unpatched.
After Ahmed privately documented the issues to Zoom in April and subsequently in July, the organization issued a resolve on August 3 (model 5.2.4).
It really is worthy of noting that for some of these assaults to transpire, an attacker would need to have to have previously compromised the victim’s product by other suggests. But that will not get absent the significance of the flaws.
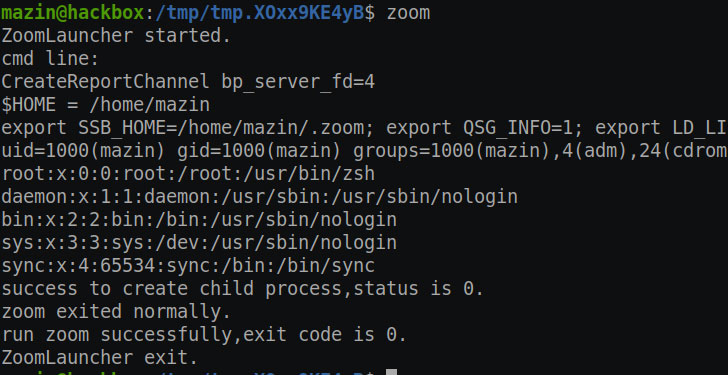
In one scenario, Ahmed uncovered an issue with the Zoom Launcher for Linux that could enable an adversary to run unauthorized software owing to the method it launches the “zoom” executable.
“This breaks all of the protection of application whitelisting, will allow malware to run as a subprocess of a trusted vendor (Zoom), and is a lousy style and design/security apply by all signifies,” Ahmed claimed in an examination.
That is not all. In a very similar vein, an attacker with obtain to the victim’s machine can read through and exfiltrate Zoom person information and configuration by navigating to the community database and even accessing chat messages saved on the technique in plaintext structure.
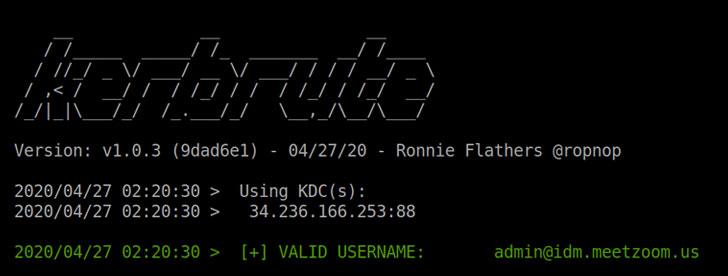
Two other flaws involved an externally available Kerberos authentication provider (“ca01.idm.meetzoom.us”) and a TLS/SSL issue that allows malware inject personalized certification fingerprints into the local Zoom database.
“This is per user certification pinning and intentionally makes it possible for for the person to allow for tailor made certificates,” Zoom stated of the certification injection flaw. “The person can create to their own databases, but no other non-root end users can. It’s widespread best follow to have user apps run at their privilege stage, as demanding Zoom to run as root would introduce unnecessary security hazards to Zoom and our clients.”
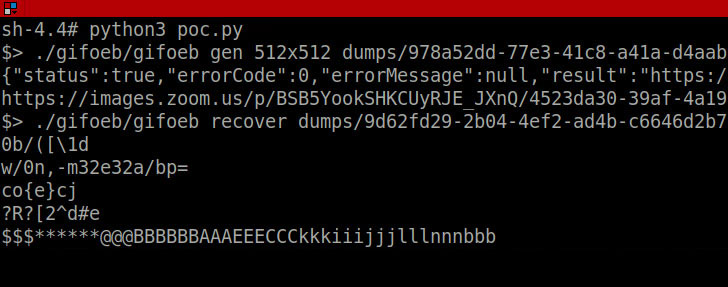
But it will get much more fascinating. Ahmed went on to emphasize a memory leak vulnerability by exploiting the profile photograph aspect on Zoom to upload a malicious GIF image, down load the rendered file, and extract information from it to leak parts of procedure memory.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
“Soon after an internal investigation, we have concluded that the conduct was not a memory leak but just our image utility’s very best energy at converting a malformed gif into a jpeg,” the enterprise mentioned.
While Ahmed thinks this to be a consequence of a identified flaw in ImageMagick image conversion application (CVE-2017-15277), Zoom has said it isn’t going to use the utility to transform GIFs uploaded as profile pics into JPEG structure.
In reaction to the disclosures, Zoom has taken down the exposed Kerberos authentication server to avert brute-pressure attacks, though also acknowledging that it really is performing on addressing the deficiency of encryption even though storing the chat logs.
It really is encouraged that end users update Zoom to the most current edition to mitigate any risk arising out of these issues.
The growth came as the organization resolved a security flaw previous thirty day period. It permitted attackers to crack the numeric passcode made use of to secure personal meetings on the platform and eavesdrop on members.
Found this posting exciting? Stick to THN on Facebook, Twitter and LinkedIn to read more distinctive articles we write-up.

 #DEFCON: Bypassing Biometric Scanners with 3D Printed Fingerprints
#DEFCON: Bypassing Biometric Scanners with 3D Printed Fingerprints