A security researcher was awarded a bug bounty of $107,500 for identifying security issues in Google Dwelling good speakers that could be exploited to set up backdoors and convert them into wiretapping products.
The flaws “allowed an attacker within just wi-fi proximity to install a ‘backdoor’ account on the machine, enabling them to send out instructions to it remotely over the internet, obtain its microphone feed, and make arbitrary HTTP requests inside the victim’s LAN,” the researcher, who goes by the title Matt, disclosed in a specialized compose-up published this 7 days.
In earning these kinds of malicious requests, not only could the Wi-Fi password get uncovered, but also give the adversary immediate accessibility to other products related to the very same network. Adhering to accountable disclosure on January 8, 2021, the issues have been remediated by Google in April 2021.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
The issue, in a nutshell, has to do with how the Google Property computer software architecture can be leveraged to increase a rogue Google person account to a target’s home automation system.

In an attack chain detailed by the researcher, a risk actor looking to eavesdrop on a victim can trick the unique into setting up a malicious Android app, which, upon detecting a Google Home system on the network, issues stealthy HTTP requests to hyperlink an attacker’s account to the victim’s machine.
Taking factors a notch larger, it also emerged that, by staging a Wi-Fi deauthentication attack to power a Google Home gadget to disconnect from the network, the appliance can be made to enter a “setup method” and create its own open Wi-Fi network.
The danger actor can subsequently hook up to the device’s setup network and ask for information like machine name, cloud_system_id, and certification, and use them to link their account to the gadget.
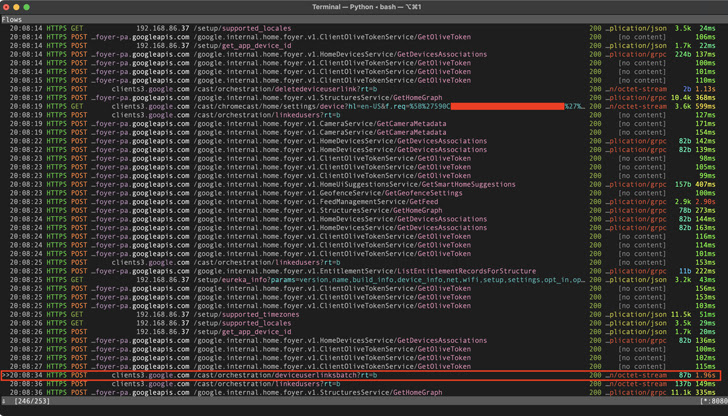
No matter of the attack sequence used, a productive link procedure permits the adversary to take gain of Google House routines to change down the volume to zero and connect with a particular phone quantity at any offered level in time to spy on the target by the device’s microphone.
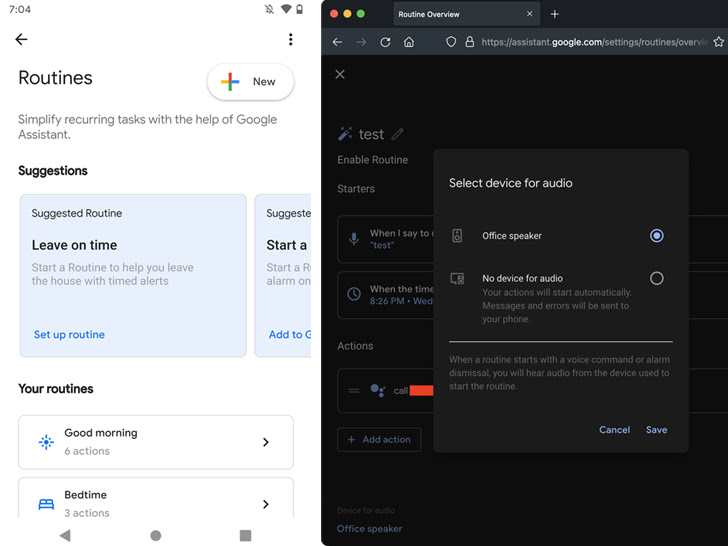
“The only issue the victim might observe is that the device’s LEDs convert sound blue, but they’d most likely just suppose it truly is updating the firmware or a little something,” Matt reported. “Throughout a call, the LEDs do not pulse like they normally do when the device is listening, so there is no indication that the microphone is open up.”
Moreover, the attack can be extended to make arbitrary HTTP requests within the victim’s network and even browse data files or introduce destructive modifications on the connected product that would get utilized following a reboot.
This is not the first time these kinds of attack solutions have been devised to covertly snoop on prospective targets by way of voice-activated units.
In November 2019, a team of academics disclosed a approach known as Gentle Instructions, which refers to a vulnerability of MEMS microphones that permits attackers to remotely inject inaudible and invisible instructions into popular voice assistants like Google Assistant, Amazon Alexa, Fb Portal, and Apple Siri making use of light.
Discovered this report attention-grabbing? Stick to us on Twitter and LinkedIn to go through extra distinctive written content we article.
Some sections of this write-up are sourced from:
thehackernews.com


 What is multi-factor authentication (MFA) fatigue and how do you defend against attacks?
What is multi-factor authentication (MFA) fatigue and how do you defend against attacks?