
As several as 85 command-and-regulate (C2) servers have been found out supported by the ShadowPad malware given that September 2021, with infrastructure detected as recently as Oct 16, 2022.
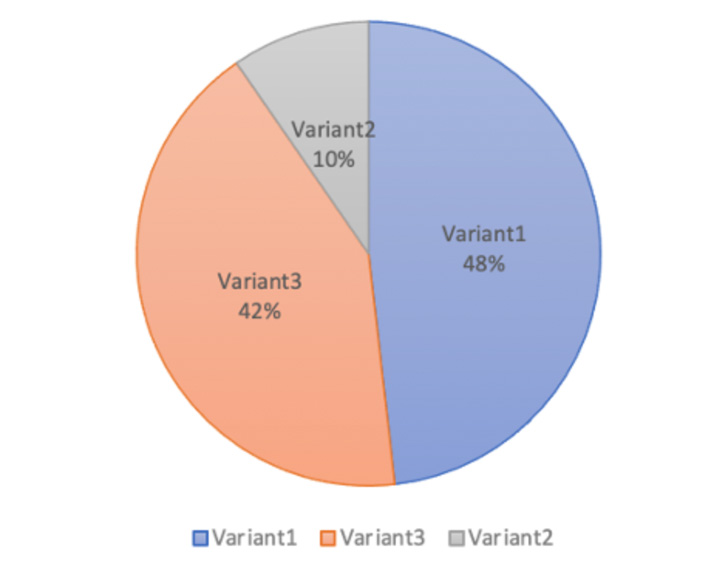
That’s according to VMware’s Threat Examination Device (TAU), which analyzed 3 ShadowPad variants using TCP, UDP, and HTTP(S) protocols for C2 communications.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
ShadowPad, witnessed as a successor to PlugX, is a modular malware system privately shared among a number of Chinese state-sponsored actors considering that 2015.
Taiwanese cybersecurity company TeamT5, earlier this Might, disclosed details of yet another China-nexus modular implant named Pangolin8RAT, which is considered to be the successor of the PlugX and ShadowPad malware households, linking it to a risk group dubbed Tianwu.
An examination of the 3 ShadowPad artifacts, which have been previously set to use by Winnti, Tonto Team, and an rising menace cluster codenamed Room Pirates, produced it possible to find the C2 servers by scanning the record of open hosts created by a resource named ZMap, VMware reported.

The enterprise more disclosed it determined Spyder and ReverseWindow malware samples communicating with ShadowPad C2 IP addresses, both of which are malicious applications set to use by APT41 (aka Winnti) and LuoYu.
On top of that, overlaps have been observed concerning the aforementioned Spyder sample and a Worker element of the threat actor’s Winnti 4. trojan.
“Scanning APT malware C2s on the Internet is from time to time like acquiring a needle in a haystack,” Takahiro Haruyama, senior risk researcher at VMware TAU, mentioned. “Nevertheless, at the time the C2 scanning works, it can turn out to be a video game changer as one particular of the most proactive threat detection approaches.”
Uncovered this report appealing? Stick to THN on Facebook, Twitter and LinkedIn to study much more exceptional content material we post.
Some parts of this post are sourced from:
thehackernews.com


 Ransomware: Open Source to the Rescue
Ransomware: Open Source to the Rescue