Researchers have lose light-weight on a new hybrid malware marketing campaign focusing on both Android and Windows operating techniques in a bid to extend its pool of victims.
The attacks entail the use of unique malware this sort of as ERMAC, Erbium, Aurora, and Laplas, according to a ThreatFabric report shared with The Hacker News.
“This marketing campaign resulted in thousands of victims,” the Dutch cybersecurity business said, adding, “Erbium stealer correctly exfiltrated facts from additional then 1,300 victims.”

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

The ERMAC bacterial infections start with a fraudulent website that promises to offer you Wi-Fi authorization application for Android and Windows that, when set up, comes with features to steal seed phrases from crypto wallets and other sensitive information.
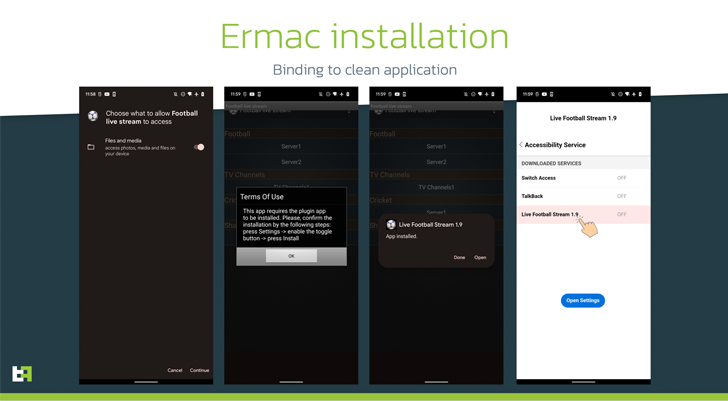
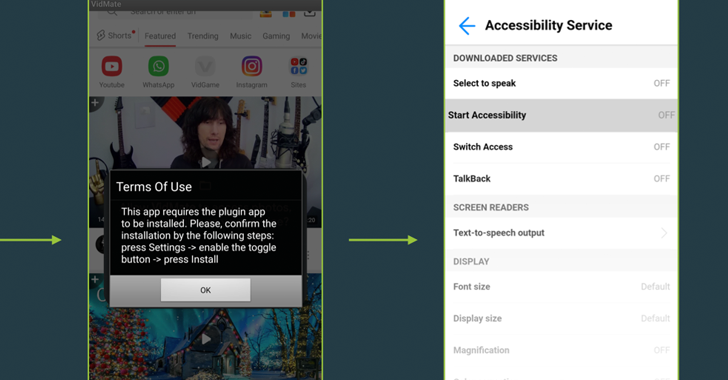
ThreatFabric said it also identified a number of destructive applications that had been trojanized versions of reputable apps like Instagram, with the operators making use of them as droppers to produce the obfuscated malicious payload.
The rogue applications, dubbed Zombinder, are claimed to have been made applying an APK binding support advertised on the dark web by a nicely-recognized danger actor considering the fact that March 2022.
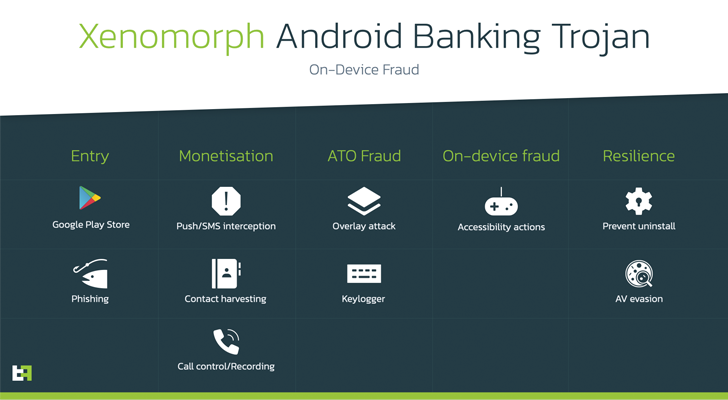
This sort of zombie applications have been utilized to distribute Android banking trojans like SOVA and Xenomorph targeting customers in Spain, Portugal, and Canada, among many others.
Interestingly, the obtain selection for Windows on the booby-trapped web site distributing ERMAC is designed to deploy the Erbium and Aurora data stealers on the compromised method.
Erbium, which is a malware-as-a-service (MaaS) licensed for $1,000 for every 12 months, not only steals passwords and credit rating card info, but has also been noticed acting as a conduit to fall the Laplas clipper that is employed to hijack crypto transactions.
“The existence of this kind of a vast variety of trojans may also suggest that the malicious landing webpage is applied by various actors and supplied to them as a part of a third-party distribution company,” the researchers theorized.
Identified this posting attention-grabbing? Abide by us on Twitter and LinkedIn to go through a lot more exclusive information we put up.
Some areas of this posting are sourced from:
thehackernews.com

 Australia to hunt down hackers, sets ‘most cyber-secure country by 2030’ target
Australia to hunt down hackers, sets ‘most cyber-secure country by 2030’ target