Cybersecurity researchers have uncovered a new Windows malware with worm-like capabilities and is propagated by means of detachable USB equipment.
Attributing the malware to a cluster named “Raspberry Robin,” Red Canary scientists mentioned that the worm “leverages Windows Installer to achieve out to QNAP-affiliated domains and download a destructive DLL.”
The earliest signals of the action are reported to day back to September 2021, with bacterial infections observed in companies with ties to technology and producing sectors.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
Attack chains pertaining to Raspberry Robin get started with connecting an infected USB travel to a Windows device. Current inside the gadget is the worm payload, which seems as a .LNK shortcut file to a legitimate folder.
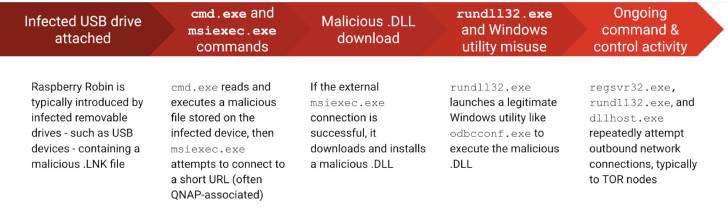
The worm then requires care of spawning a new system using cmd.exe to study and execute a destructive file saved on the external travel.
This is followed by launching explorer.exe and msiexec.exe, the latter of which is employed for exterior network conversation to a rogue area for command-and-command (C2) needs and to download and put in a DLL library file.
The destructive DLL is subsequently loaded and executed working with a chain of legitimate Windows utilities this sort of as fodhelper.exe, rundll32.exe to rundll32.exe, and odbcconf.exe, successfully bypassing User Account Handle (UAC).
Also typical across Raspberry Robin detections is the presence of outbound C2 get hold of involving the processes regsvr32.exe, rundll32.exe, and dllhost.exe to IP addresses related with Tor nodes.
That reported, the operators’ targets stay unanswered at this phase. It really is also unclear how and where by the external drives are infected, despite the fact that it can be suspected that it can be carried out offline.
“We also you should not know why Raspberry Robin installs a destructive DLL,” the scientists explained. “One speculation is that it may possibly be an endeavor to create persistence on an contaminated technique.”
Identified this short article fascinating? Comply with THN on Fb, Twitter and LinkedIn to read a lot more unique content material we post.
Some areas of this short article are sourced from:
thehackernews.com


 Ukrainians DDoS Russian Vodka Supply Chains
Ukrainians DDoS Russian Vodka Supply Chains