The operators powering the Rig Exploit Package have swapped the Raccoon Stealer malware for the Dridex economical trojan as portion of an ongoing campaign that commenced in January 2022.
The swap in modus operandi, noticed by Romanian firm Bitdefender, arrives in the wake of Raccoon Stealer quickly closing the job following one particular of its staff customers responsible for critical functions passed absent in the Russo-Ukrainian war in March 2022.
The Rig Exploit Package is notable for its abuse of browser exploits to distribute an array of malware. Initially spotted in 2019, Raccoon Stealer is a credential-stealing trojan that’s marketed and offered on underground boards as a malware-as-a-services (MaaS) for $200 a thirty day period.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
That explained, the Raccoon Stealer actors are previously functioning on a 2nd edition which is anticipated to be “rewritten from scratch and optimized.” But the void left by the malware’s exit is remaining crammed by other information stealers such as RedLine Stealer and Vidar.
Dridex (aka Bugat and Cridex), for its component, has the capability to download additional payloads, infiltrate browsers to steal client login information and facts entered on banking internet websites, capture screenshots, and log keystrokes, amid many others, by means of various modules that enable its functionality to be prolonged at will.
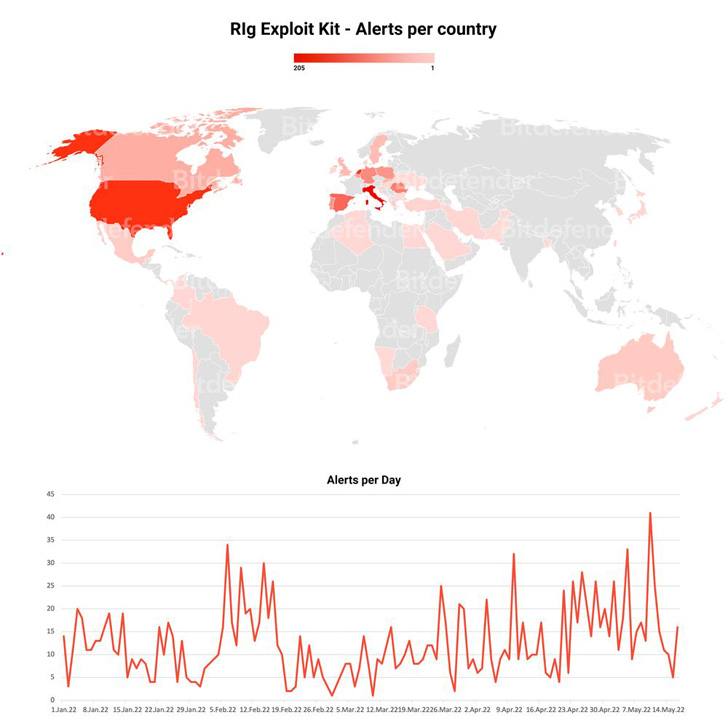
In April 2022, Bitdefender found out one more Rig Exploit Package marketing campaign distributing the RedLine Stealer trojan by exploiting an Internet Explorer flaw patched by Microsoft previous calendar year (CVE-2021-26411).

That’s not all. Final May possibly, a independent marketing campaign exploited two scripting motor vulnerabilities in unpatched Internet Explorer browsers (CVE-2019-0752 and CVE-2018-8174) to supply a malware called WastedLoader, so named for its similarities to WasterLocker but lacking the ransomware part.
“This the moment all over again demonstrates that threat actors are agile and brief to adapt to modify,” the cybersecurity agency stated. “By design, Rig Exploit Kit enables for rapid substitution of payloads in case of detection or compromise, which aids cyber felony teams recover from disruption or environmental variations.”
Located this report attention-grabbing? Observe THN on Fb, Twitter and LinkedIn to read through a lot more exceptional content material we submit.
Some areas of this article are sourced from:
thehackernews.com

 #InfosecurityEurope2022 Firms Face Emerging Threats as Bad Actors Evade Defenses
#InfosecurityEurope2022 Firms Face Emerging Threats as Bad Actors Evade Defenses