Russian menace actors have been probably linked to what is been described as the “major cyber attack versus Danish critical infrastructure,” in which 22 providers affiliated with the procedure of the country’s electricity sector ended up specific in Could 2023.
“22 simultaneous, successful cyberattacks towards Danish critical infrastructure are not commonplace,” Denmark’s SektorCERT said [PDF]. “The attackers knew in progress who they were being going to goal and bought it correct every time. Not when did a shot overlook the focus on.”
The company stated it identified evidence connecting just one or additional attacks to Russia’s GRU armed service intelligence agency, which is also tracked under the title Sandworm and has a keep track of document of orchestrating disruptive cyber assaults on industrial regulate devices. This evaluation is based mostly on artifacts speaking with IP addresses that have been traced to the hacking crew.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
The unparalleled and coordinated cyber attacks took put on Might 11 by exploiting CVE-2023-28771 (CVSS rating: 9.8), a critical command injection flaw impacting Zyxel firewalls that was disclosed in late April 2023.

On the 11 firms that were being efficiently infiltrated, the danger actors executed destructive code to conduct reconnaissance of the firewall configurations and decide the future system of motion.
“This form of coordination calls for scheduling and means,” SektorCERT explained in a detailed timeline of gatherings. “The advantage of attacking simultaneously is that the info about a single attack can not spread to the other targets right before it is also late.”
“This places the energy of details sharing out of engage in since no one can be warned in progress about the ongoing attack considering that everyone is attacked at the exact same time. It is strange – and very effective.”
A second wave of attacks focusing on far more companies was subsequently recorded from Could 22 to 25 by an attack team with previously unseen cyber weapons, boosting the probability that two distinct risk actors have been involved in the marketing campaign.
That said, it’s at the moment unclear if the groups collaborated with every other, labored for the identical employer, or ended up acting independently.
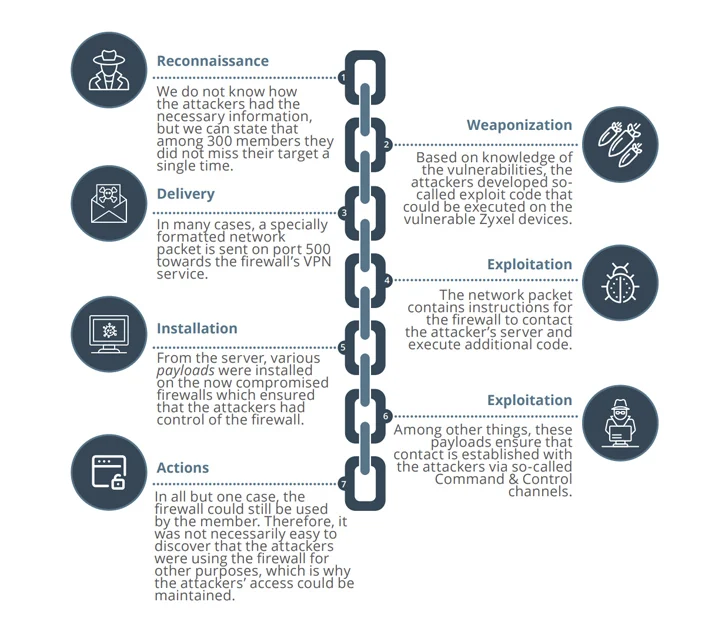
These attacks are suspected to have weaponized two more critical bugs in Zyxel gear (CVE-2023-33009 and CVE-2023-33010, CVSS scores: 9.8) as zero-days to co-decide the firewalls into Mirai and MooBot botnets, supplied that patches for them were being produced by the enterprise on Could 24, 2023.
The compromised equipment, in some conditions, were employed to carry out distributed denial-of-support (DDoS) attacks against unnamed organizations in the U.S. and Hong Kong.
“After the exploit code for some of the vulnerabilities grew to become publicly recognized about 30/5, attack attempts in opposition to the Danish critical infrastructure exploded – specially from IP addresses in Poland and Ukraine,” SektorCERT stated.
The onslaught of attacks prompted the affected entities to disconnect from the internet and go into island manner, the company more added.

But it really is not only country-state actors. The energy sector is also significantly getting a target for ransomware groups, with initial obtain brokers (IABs) actively promoting unauthorized obtain to nuclear electrical power firms, according to a report from Resecurity before this 7 days.
The enhancement comes as Censys found out six hosts belonging to NTC Vulkan, a Moscow-based mostly IT contractor that is alleged to have equipped offensive cyber applications to Russian intelligence organizations, such as Sandworm.
Furthermore, the investigation uncovered a relationship to a team called Raccoon Security by way of an NTC Vulkan certificate.
“Racoon Security is a manufacturer of NTC Vulkan and that it is probable that Raccoon Security’s routines contain either previous or current participation in the formerly-mentioned leaked initiatives contracted by the GRU,” Matt Lembright, director of Federal Apps at Censys, mentioned.
Uncovered this post attention-grabbing? Abide by us on Twitter and LinkedIn to read extra special articles we publish.
Some components of this write-up are sourced from:
thehackernews.com


 U.S. Takes Down IPStorm Botnet, Russian-Moldovan Mastermind Pleads Guilty
U.S. Takes Down IPStorm Botnet, Russian-Moldovan Mastermind Pleads Guilty