In the very last decade, there has been a rising disconnect in between front-line analysts and senior administration in IT and Cybersecurity. Nicely-documented problems experiencing present day analysts revolve about a substantial quantity of alerts, false positives, lousy visibility of specialized environments, and analysts paying out also considerably time on handbook responsibilities.
The Effect of Alert Exhaustion and Fake Positives
Analysts are overcome with alerts. The knock-on influence of this is that fatigued analysts are at risk of lacking key particulars in incidents, and generally conduct time-consuming triaging tasks manually only to finish up copying and pasting a generic closing comment into a false beneficial notify.
It is probably that there will usually be phony positives. And lots of would argue that a fake positive is greater than a wrong negative. But for proactive actions to be built, we have to transfer closer to the heart of an incident. That necessitates diving into how analysts carry out the triage and investigation course of action.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
SHQ Response System for Triage and Investigation
A standard triage method is typically manual, and leverages analysts to perform individual log lookups for contextual details. From this details, they get started to piece together a tale of what has happened and deliver an notion of the general risk scale.
The SHQ Reaction System utilizes Synthetic Intelligence (AI) for log correlation, pulling facts from various resources and visualizing it in a single incident webpage. From this, critical knowledge is presented throughout a obvious timeline, and artifacts are updated on the portal routinely.
By obtaining the most significant details presented in just one place, an investigating analyst can cut by the sound and stay in one particular interface. They no extended need to have to pivot throughout a number of log resources or conduct guide SIEM lookups to assemble the pertinent logs to then realize the story of a security incident.
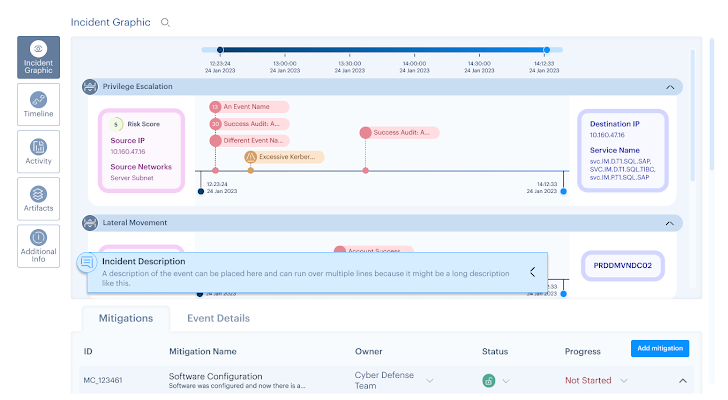 Figure 1: Incident Graphic, SHQ Response Platform ©2024 SecurityHQ
Figure 1: Incident Graphic, SHQ Response Platform ©2024 SecurityHQ
The timeline functionality also lets an analyst to investigate the logic at the rear of an inform or use scenario bring about. This is proven with the appropriate Indicators of Compromise (IoCs), which can be automatically blocked applying again-finish built-in equipment.
Incident Response Platform for Senior Stakeholders
Confused analysts swamped by fake positives is endemic. Head of World SOC operations at SecurityHQ, Deodatta Wandhekar, put it most effective by explaining that:
‘Sixty per cent of SOC Incidents are repeat conclusions that keep re-surfacing thanks to underlying unmitigated dangers. The actors could be different however, the risk is mainly the exact. This is triggering sizeable alert fatigue.’
One particular need to take into consideration how to bridge this hole, with the two a distinct concentration on small business goals and risk appetite, when retaining a level of technical element.
Risk Sign up for Collaboration & System
SecurityHQ’s crafted-in Risk Register allows analysts and business enterprise leaders to do the job together to travel mitigation routines, utilizing the technological acumen of operational team to notify strategic organization conclusions.
This permits analysts to play a job in steering a cybersecurity method. By possessing a level of technical possession, a additional collaborative solution is fostered between operational analysts and administration team. It also makes it possible for when-overworked analysts to plainly see the fruits of their labor mirrored in broader business tactics.
Following Ways
SecurityHQ as both equally a consultative husband or wife, and as the operator of these a platform, contributes to acquiring a better romantic relationship concerning administration and analysts by providing an intuitive, and government-welcoming, risk sign up.
From in this article, the concentrate on proactive methods and roadmaps more than just ‘firefighting’ and closing incidents within just a Service Degree Settlement (SLA) results in the opportunity for meaningful improve in a corporation.
For far more information, discuss to an skilled right here. If you suspect a security incident, report an incident in this article.
Be aware: This posting was expertly published by Tim Chambers, Senior Cyber Security Supervisor at SecurityHQ
Identified this report exciting? This write-up is a contributed piece from a person of our valued associates. Observe us on Twitter and LinkedIn to read more special material we write-up.
Some areas of this short article are sourced from:
thehackernews.com


 Severe Vulnerabilities in Cinterion Cellular Modems Pose Risks to Various Industries
Severe Vulnerabilities in Cinterion Cellular Modems Pose Risks to Various Industries