The Android banking trojan known as SpyNote has been dissected to expose its numerous data-gathering options.
Ordinarily spread via SMS phishing strategies, attack chains involving the spy ware trick possible victims into installing the app by clicking on the embedded url, according to F-Safe.
Other than requesting invasive permissions to access contact logs, camera, SMS messages, and exterior storage, SpyNote is recognized for hiding its presence from the Android household screen and the Recents display in a bid to make it challenging to stay away from detection.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

“The SpyNote malware application can be introduced through an exterior result in,” F-Secure researcher Amit Tambe mentioned in an assessment printed past 7 days. “On obtaining the intent, the malware application launches the major exercise.”
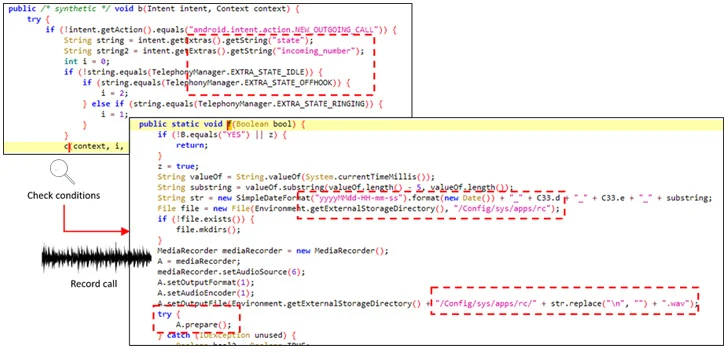
But most importantly, it seeks accessibility permissions, subsequently leveraging it to grant alone extra permissions to history audio and phone phone calls, log keystrokes, as perfectly as seize screenshots of the phone by using the MediaProjection API.
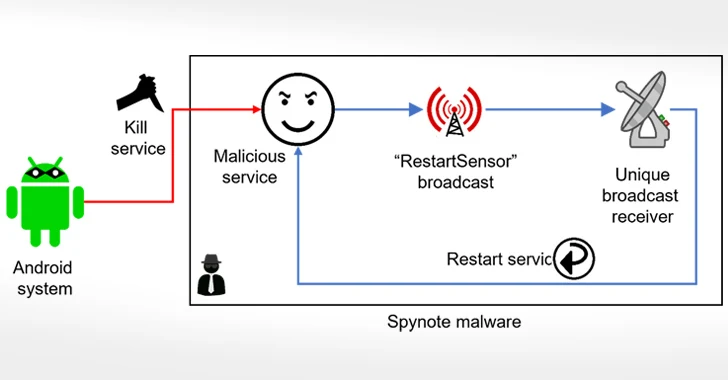
A nearer evaluation of the malware has exposed the presence of what are identified as diehard services that goal to resist attempts, both produced by the victims or by the operating process, at terminating it.
This is achieved by registering a broadcast receiver that’s made to restart it automatically each time it is about to be shut down. What is more, consumers who endeavor to uninstall the destructive application by navigating to Configurations are prevented from accomplishing so by closing the menu display screen by means of its abuse of the accessibility APIs.
“The SpyNote sample is spyware that logs and steals a variety of info, such as essential strokes, phone logs, data on put in purposes, and so on,” Tambe mentioned. “It stays concealed on the victim’s unit generating it complicated to detect. It also would make uninstallation particularly challenging.”

“The target is sooner or later remaining only with the choice of executing a manufacturing unit reset, losing all details, therefore, in the approach.”
The disclosure comes as the Finnish cybersecurity organization thorough a bogus Android app that masquerades as an running process update to entice targets into granting it accessibility providers permissions and exfiltrate SMS and lender information.
Found this report appealing? Comply with us on Twitter and LinkedIn to read through extra unique content material we article.
Some pieces of this short article are sourced from:
thehackernews.com

 The Fast Evolution of SaaS Security from 2020 to 2024 (Told Through Video)
The Fast Evolution of SaaS Security from 2020 to 2024 (Told Through Video)