Right now, the LockBit ransomware is the most energetic and profitable cybercrime organization in the earth. Attributed to a Russian Threat Actor, LockBit has stepped out from the shadows of the Conti ransomware group, who had been disbanded in early 2022.
LockBit ransomware was initial discovered in September 2019 and was formerly identified as ABCD ransomware mainly because of the “.abcd virus” extension initial observed. LockBit operates as a Ransomware-as-a-service (RaaS) design. In quick, this indicates that affiliates make a deposit to use the software, then split the ransom payment with the LockBit group. It has been reported that some affiliate marketers are receiving a share as significant of 75%. LockBit’s operators have posted advertisements for their affiliate software on Russian-language legal boards stating they will not function in Russia or any CIS international locations, nor will they function with English-talking builders except if a Russian-talking “guarantor” vouches for them.
Preliminary attack vectors of LockBit include social engineering, this kind of as phishing, spear phishing, and organization email compromise (BEC), exploiting community-facing apps, selecting preliminary accessibility brokers” (IABs), and making use of stolen credentials to obtain valid accounts, this kind of as distant desktop protocol (RDP), as effectively as brute-drive cracking attacks.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
All through past year’s Worldwide Danger Forecast webinar, hosted by SecurityHQ, we discovered LockBit as a important menace and highlighted them as a Menace Actor to pay out near interest to throughout 2022.
LockBit Targets
LockBit has generally targeted attacks on government entities and enterprises in a wide variety of sectors, these as healthcare, economic products and services, and industrial items and services. The ransomware has been noticed focusing on nations around the world globally, like the US, China, India, Indonesia, Ukraine, France, the UK, and Germany.
Yet another interesting feature of LockBit is that it is programmed in a way that it can’t be utilized in attacks from Russia or CIS nations around the world (Commonwealth of Independent States). This is likely a precautionary measure taken by the group to keep away from any opportunity backlash from the Russian governing administration.
The map under exhibits the areas focused by LockBit.
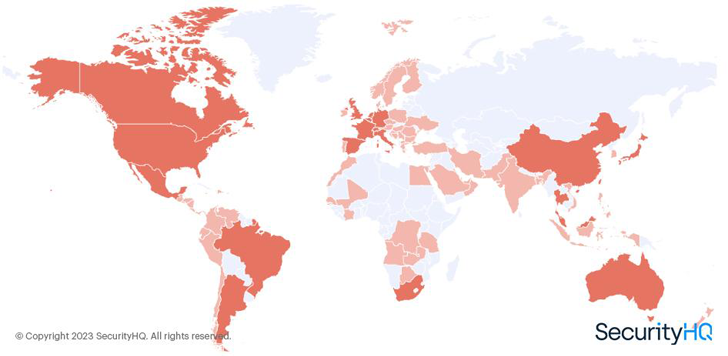 Determine 1 – SecurityHQ Evaluation of LockBit Victims Per Geography
Determine 1 – SecurityHQ Evaluation of LockBit Victims Per Geography
A Chaotic Year for LockBit
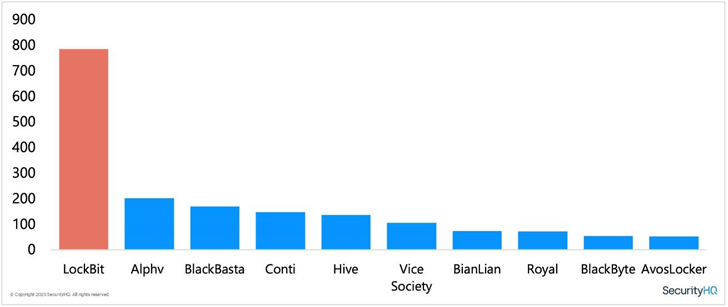
Via analysis of leak web site details, we have been able to get a genuine image of how lots of prosperous attacks LockBit experienced built. In 2022, the group posted much more profitable attacks than any other ransomware team. We have mapped the exercise of LockBit during the calendar year against other effectively-recognised ransomware teams. You can see the decline of Conti as the group started out to shut down functions. It is now described however, that users of the at the time prolific Conti ransomware team are now functioning within just the BlackBasta, BlackByte and Karakurt ransomware groups.
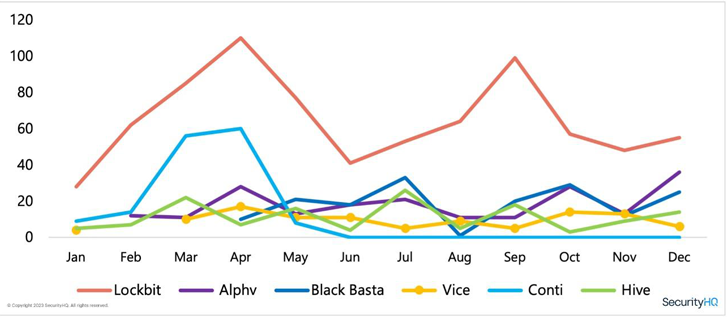
The graph below demonstrates how lively LockBit were being all through 2022, as opposed to other ransomware teams.
A person of the unique features of LockBit is their bug bounty system for their ransomware builders and compilers. The team delivers a $1 million reward for anyone who can dox (publicly reveal the identities of) their house owners. This is a sizeable sum, and it demonstrates how really serious LockBit is about protecting their anonymity.
Just lately, the group has been connected to an attack on Royal Mail in the UK. However, LockBit has denied any involvement in the attack, stating that it was carried out by an affiliate. This is not uncommon for ransomware groups, as they typically use affiliates to have out attacks in order to distance them selves from the outcomes.
Overall, the LockBit ransomware group is a formidable and sophisticated cybercrime firm that poses a considerable menace to businesses and corporations all-around the environment. With a properly-founded ransomware-as-a-provider design, a bug bounty method, and a willingness to reward individuals who reveal their identities, LockBit is a power to be reckoned with in the danger landscape.
What is RaaS?
Ransomware-as-a-assistance (RaaS) has obtained acceptance in new years. RaaS refers to a sort of business design exactly where ransomware operators provide the malware and instruments to other persons or organised crime teams to have out ransomware attacks, in trade for a share of the ransom payment. This enables even fewer technically experienced individuals to take part in ransomware attacks, expanding the variety of attacks and producing it much more tough to keep track of and apprehend the attackers.
What to Do Following
To greatly enhance your security posture, it is recommended that companies do the subsequent ways:
To listen to SecurityHQ specialists go over some of the finest threats observed in the course of 2022, explore the outcomes of a breach, with predictions for 2023, and how to mitigate against approaching cyber security threats, obtain this webinar recording’ Worldwide Risk Landscape 2023 Forecast’, to know much more.
Note: This post is by Aaron Hambleton, Director for Center East & Africa at SecurityHQ. With over 11 several years of experience across several sectors like Monetary Expert services, Retail, Insurance policy, Government, and Telecommunications, Aaron is a accredited GCDA and has know-how in incident response, risk searching, vulnerability administration, cyber security functions, threat intelligence, and consultancy.
Found this post attention-grabbing? Adhere to us on Twitter and LinkedIn to examine additional distinctive written content we write-up.
Some pieces of this write-up are sourced from:
thehackernews.com


 Brand-new Emotet campaign socially engineers its way from detection
Brand-new Emotet campaign socially engineers its way from detection