An unknown risk actor has been linked to a new Android malware strain that functions the capacity to root smartphones and consider finish manage in excess of infected smartphones while concurrently using steps to evade detection.
The malware has been named “AbstractEmu” owing to its use of code abstraction and anti-emulation checks to stay clear of functioning while beneath investigation. Notably, the worldwide cell campaign is engineered to concentrate on people and infect as several equipment as attainable indiscriminately.


Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
Lookout Risk Labs explained it found a complete of 19 Android programs that posed as utility applications and process resources like password supervisors, money supervisors, application launchers, and information preserving apps, seven of which contained the rooting operation. Only a single of the rogue applications, identified as Lite Launcher, designed its way to the formal Google Enjoy Retail store, attracting a overall of 10,000 downloads prior to it was purged.
The applications are stated to have been prominently distributed by means of 3rd-party merchants this kind of as the Amazon Appstore and the Samsung Galaxy Retail store, as well as other lesser-acknowledged marketplaces like Aptoide and APKPure.
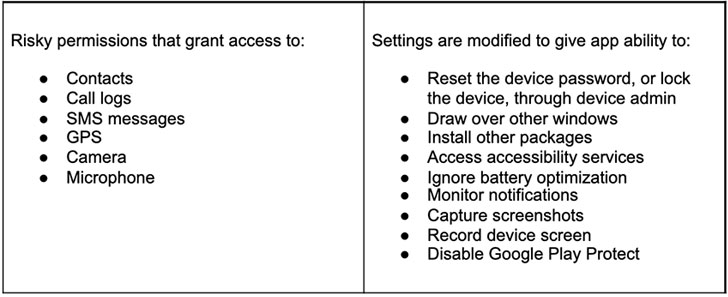
“While scarce, rooting malware is incredibly risky. By working with the rooting procedure to gain privileged obtain to the Android working technique, the danger actor can silently grant themselves hazardous permissions or install additional malware — measures that would usually call for consumer conversation,” Lookout researchers reported. “Elevated privileges also give the malware obtain to other apps’ sensitive details, some thing not doable beneath standard situation.”
The moment set up, the attack chain is made to 1 of five exploits for more mature Android security flaws that would let it to acquire root permissions and just take in excess of the device, extract delicate information, and transmit to a distant attack-controlled server —
- CVE-2015-3636 (PongPongRoot)
- CVE-2015-1805 (iovyroot)
- CVE-2019-2215 (Qu1ckr00t)
- CVE-2020-0041, and
- CVE-2020-0069
Lookout attributed the mass distributed rooting malware campaign to a “effectively-resourced group with fiscal inspiration,” with telemetry information revealing that Android gadget people in the U.S. had been the most impacted. The ultimate objective of the infiltrations stays unclear as yet.
“Rooting Android or jailbreaking iOS equipment are nonetheless the most invasive techniques to fully compromise a cell unit,” the scientists reported, including “cell products are ideal applications for cyber criminals to exploit, as they have many functionalities and maintain an huge total of sensitive facts.”
Found this post intriguing? Stick to THN on Fb, Twitter and LinkedIn to browse much more exclusive content material we submit.
Some components of this article are sourced from:
thehackernews.com

 Luxury hotel chain hit twice by hackers after reneging on ransomware payment
Luxury hotel chain hit twice by hackers after reneging on ransomware payment