South Korean education and learning, development, diplomatic, and political establishments are at the obtaining close of new attacks perpetrated by a China-aligned risk actor regarded as the Tonto Team.
“New conditions have exposed that the team is employing a file similar to anti-malware goods to ultimately execute their malicious attacks,” the AhnLab Security Unexpected emergency Reaction Heart (ASEC) reported in a report posted this 7 days.
Tonto Staff, active since at the very least 2009, has a keep track of record of targeting numerous sectors across Asia and Eastern Europe. Previously this calendar year, the team was attributed to an unsuccessful phishing attack on cybersecurity company Team-IB.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
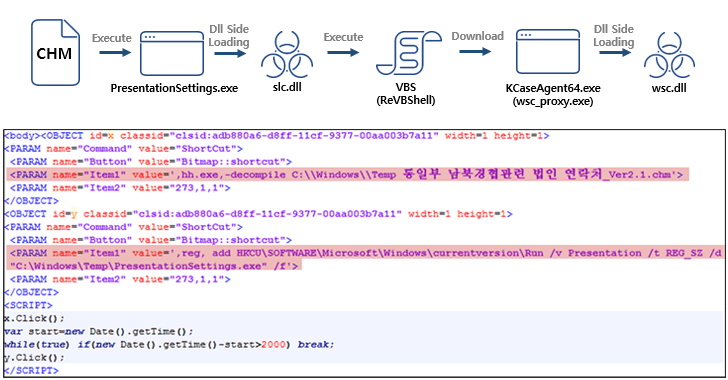
The attack sequence found by ASEC starts off with a Microsoft Compiled HTML Enable (.CHM) file that executes a binary file to facet-load a destructive DLL file (slc.dll) and start ReVBShell, an open up resource VBScript backdoor also set to use by another Chinese danger actor termed Tick.
ReVBShell is subsequently leveraged to obtain a second executable, a legitimate Avast program configuration file (wsc_proxy.exe), to facet-load a 2nd rogue DLL (wsc.dll), in the end primary to the deployment of the Bisonal distant access trojan.
“The Tonto Staff is continuously evolving via several implies these kinds of as applying ordinary program for much more elaborate attacks,” ASEC mentioned.
Approaching WEBINARLearn to End Ransomware with Authentic-Time Protection
Sign up for our webinar and study how to stop ransomware attacks in their tracks with authentic-time MFA and provider account defense.
Save My Seat!
The use of CHM files as a distribution vector for malware is not confined to Chinese danger actors alone. Identical attack chains have been adopted by a North Korean nation-point out team identified as ScarCruft in attacks aimed at its southern counterpart to backdoor qualified hosts.
The adversary, also known as APT37, Reaper, and Ricochet Chollima, has given that also utilized LNK data files to distribute the RokRAT malware, which is capable of collecting consumer qualifications and downloading more payloads.
Discovered this post intriguing? Adhere to us on Twitter and LinkedIn to read a lot more exclusive content we article.
Some parts of this posting are sourced from:
thehackernews.com

 #RSAC: AI Dominates RSA as Excitement and Questions Surround its Potential in Cybersecurity
#RSAC: AI Dominates RSA as Excitement and Questions Surround its Potential in Cybersecurity