The infamous TrickBot malware is focusing on shoppers of 60 monetary and technology organizations, such as cryptocurrency firms, principally located in the U.S., even as its operators have updated the botnet with new anti-evaluation attributes.
“TrickBot is a innovative and multipurpose malware with far more than 20 modules that can be downloaded and executed on need,” Check out Point scientists Aliaksandr Trafimchuk and Raman Ladutska explained in a report printed now.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
In addition to currently being both common and persistent, TrickBot has regularly evolved its methods to go previous security and detection levels. To that conclude, the malware’s “injectDll” web-injects module, which is dependable for thieving banking and credential facts, leverages anti-deobfuscation strategies to crash the web web page and thwart makes an attempt to scrutinize the resource code.
Also place in area are anti-assessment guardrails to avoid security researchers from sending automated requests to command-and-management (C2) servers to retrieve new web injects.
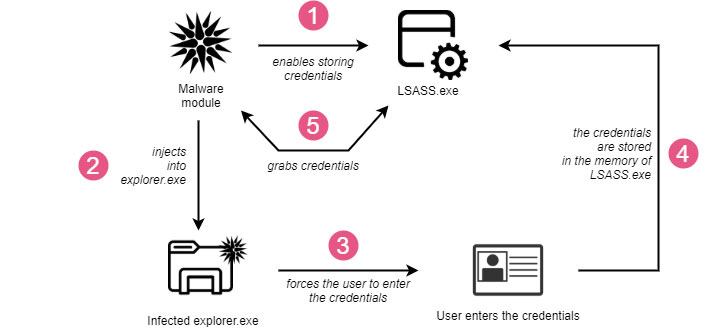
Yet another of TrickBot’s essential strengths is its potential to propagate alone, which it achieves by making use of the “tabDLL” module to steal the users’ credentials and distribute the malware by means of SMBv1 network share utilizing the EternalRomance exploit.
A 3rd crucial module deployed as element of TrickBot bacterial infections is “pwgrabc,” a credential stealer created to siphon passwords from web browsers and a number of other purposes such as Outlook, Filezilla, WinSCP, RDP, Putty, OpenSSH, OpenVPN, and TeamViewer.
“TrickBot attacks high-profile victims to steal the qualifications and present its operators accessibility to the portals with delicate knowledge exactly where they can cause increased injury,” the scientists reported, adding “the operators powering the infrastructure are really experienced with malware improvement on a high degree as well.”
The conclusions also arrive as the TrickBot gang was disclosed as employing metaprogramming strategies for its Bazar family members of malware to conceal their code and defend towards reverse engineering with the supreme objective of evading signature-based detection.
Uncovered this report intriguing? Adhere to THN on Facebook, Twitter and LinkedIn to browse additional exceptional content material we article.
Some parts of this article are sourced from:
thehackernews.com




 Emotet Now Spreading Through Malicious Excel Files
Emotet Now Spreading Through Malicious Excel Files