A new malvertising campaign has been noticed capitalizing on a compromised web site to encourage spurious versions of PyCharm on Google research final results by leveraging Dynamic Look for Advertisements.
“Unbeknownst to the internet site owner, one of their adverts was mechanically produced to market a preferred method for Python builders, and obvious to folks executing a Google research for it,” Jérôme Segura, director of menace intelligence at Malwarebytes, stated in a report.
“Victims who clicked on the ad were taken to a hacked web web page with a hyperlink to obtain the software, which turned out to set up more than a dozen diverse parts of malware rather.”

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

The infected website in question is an unnamed on-line portal that specializes in marriage arranging, which experienced been injected with malware to provide bogus inbound links to the PyCharm computer software.
For each Malwarebytes, targets are directed to the web site making use of Dynamic Lookup Ads, an advertisement offering from Google that programmatically takes advantage of the site’s information to tailor focused advertisements based on the lookup terms.
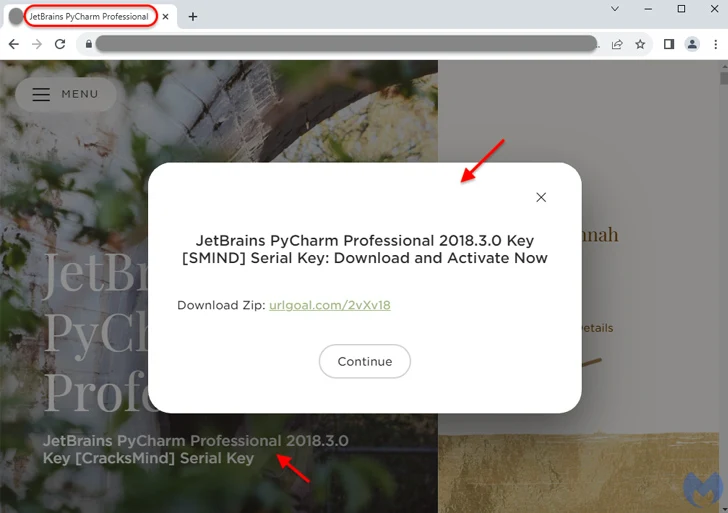
“When a person searches on Google with phrases intently related to the titles and usually made use of phrases on your internet site, Google Ads will use these titles and phrases to select a landing web site from your web page and produce a crystal clear, appropriate headline for your advert,” Google describes in its assist documentation.
As a outcome, a risk actor with capabilities to alter the website’s content could also make the advert campaigns a valuable instrument for abuse, properly serving Google Look for end users advertisements that can end result in unintended behavior.

“What transpired in this article is Google Advertisements dynamically produced this advert from the hacked page, which tends to make the web page owner an accidental intermediary and victim spending for their possess destructive ad,” Segura described.
The advancement arrives as Akamai in depth the infrastructure guiding a subtle phishing marketing campaign concentrating on hospitality web-sites and their shoppers.
“The marketing campaign is a world-wide danger, with a notable total of DNS website traffic found in Switzerland, Hong Kong, and Canada,” the enterprise reported.
“Though the campaign was to begin with thought to have been active only since September 2023, the area registration reveals area names remaining registered and queried as early as June 2023.”
Located this post exciting? Stick to us on Twitter and LinkedIn to examine far more exceptional content material we article.
Some components of this posting are sourced from:
thehackernews.com

 Canada Bans WeChat and Kaspersky Apps On Government Devices
Canada Bans WeChat and Kaspersky Apps On Government Devices