Federal government entities in Ukraine have been breached as part of a new campaign that leveraged trojanized variations of Windows 10 installer documents to perform publish-exploitation actions.
Mandiant, which discovered the supply chain attack all around mid-July 2022, said the malicious ISO files have been distributed by using Ukrainian- and Russian-language Torrent websites. It’s monitoring the danger cluster as UNC4166.
“On installation of the compromised program, the malware gathers facts on the compromised program and exfiltrates it,” the cybersecurity organization said in a complex deep dive published Thursday.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
Although the adversarial collective’s provenance is unknown, the intrusions are explained to have qualified companies that were beforehand victims of disruptive wiper attacks attributed to APT28, a Russian state-sponsored actor.
The ISO file, for every the Google-owned threat intelligence firm, was made to disable the transmission of telemetry details from the contaminated computer to Microsoft, install PowerShell backdoors, as perfectly as block automated updates and license verification.

The key aim of the procedure seems to have been information and facts accumulating, with added implants deployed to the devices, but only after conducting an preliminary reconnaissance of the compromised ecosystem to determine if it consists of the intelligence of worth.
These integrated Stowaway, an open up source proxy resource, Cobalt Strike Beacon, and SPAREPART, a light-weight backdoor programmed in C, enabling the danger actor to execute commands, harvest info, capture keystrokes and screenshots, and export the info to a remote server.
In some circumstances, the adversary attempted to down load the TOR anonymity browser on to the victim’s product. Although the correct cause for this action is not apparent, it’s suspected that it could have served as an different exfiltration route.

SPAREPART, as the title implies, is assessed to be a redundant malware deployed to sustain remote obtain to the procedure ought to the other approaches are unsuccessful. It can be also functionally equivalent to the PowerShell backdoors dropped early on in the attack chain.
“The use of trojanized ISOs is novel in espionage functions and involved anti-detection abilities implies that the actors behind this activity are security conscious and affected person, as the operation would have essential a major time and means to acquire and hold out for the ISO to be put in on a network of fascination,” Mandiant explained.
Cloud Atlas Strikes Russia and Belarus
The conclusions occur as Examine Position and Positive Technologies disclosed attacks staged by an espionage team dubbed Cloud Atlas from the government sector in Russia, Belarus, Azerbaijan, Turkey, and Slovenia as part of a persistent campaign.
The hacking crew, lively due to the fact 2014, has a monitor history of attacking entities in Jap Europe and Central Asia. But since the outbreak of the Russo-Ukrainian war, it has been noticed mostly focusing on entities in Russia, Belarus, and Transnistria.
“The actors are also protecting their concentration on the Russian-annexed Crimean Peninsula, Lugansk, and Donetsk regions,” Examine Stage explained in an evaluation previous week.
Cloud Atlas, also referred to as Clear Ursa, Inception, and Oxygen, remains unattributed to date, becoming a member of the likes of other APTs like TajMahal, DarkUniverse, and Metador. The team gets its identify for its reliance on cloud companies like OpenDrive to host malware and for command-and-regulate (C2).
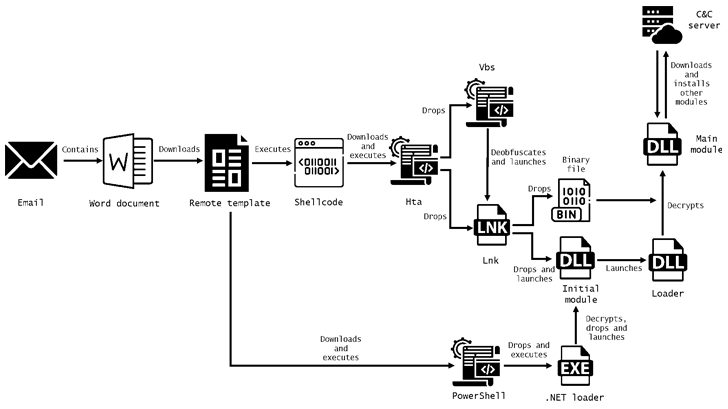
Attack chains orchestrated by the adversary usually make use of phishing e-mails containing entice attachments as the original intrusion vector, which eventually lead to the shipping of a malicious payload by way of an intricate multi-stage sequence.
The malware then proceeds to initiate contact with an actor-controlled C2 server to retrieve added backdoors capable of stealing data files with unique extensions from the breached endpoints.
Attacks observed by Check out Place, on the other hand, culminate in a PowerShell-primarily based backdoor called PowerShower, which was 1st documented by Palo Alto Networks Unit 42 in November 2018.
Some of these intrusions in June 2022 also turned out to be effective, allowing the risk actor to get whole access to the network and use equipment like Chocolatey, AnyDesk, and PuTTY to deepen their foothold.
“With the escalation of the conflict in between Russia and Ukraine, their concentration for the earlier year has been on Russia and Belarus and their diplomatic, federal government, energy and technology sectors, and on the annexed areas of Ukraine,” Check Place additional.
Discovered this short article interesting? Adhere to us on Twitter and LinkedIn to read more distinctive written content we put up.
Some sections of this posting are sourced from:
thehackernews.com


 Ex-Twitter employee Gets 3.5 Years Jail for Spying on Behalf of Saudi Arabia
Ex-Twitter employee Gets 3.5 Years Jail for Spying on Behalf of Saudi Arabia