The U.S. Justice Section (DoJ) on Friday introduced the seizure of on line infrastructure that was employed to offer a distant accessibility trojan (RAT) named Warzone RAT.
The domains – www.warzone[.]ws and three other folks – ended up “utilised to offer laptop malware used by cybercriminals to secretly obtain and steal facts from victims’ computers,” the DoJ reported.
Along with the takedown, the worldwide legislation enforcement exertion has arrested and indicted two men and women in Malta and Nigeria for their involvement in promoting and supporting the malware and helping other cybercriminals use the RAT for malicious needs.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
The defendants, Daniel Meli (27) and Prince Onyeoziri Odinakachi (31) have been billed with unauthorized harm to secured desktops, with the previous also accused of “illegally providing and advertising an digital interception device and participating in a conspiracy to commit quite a few laptop or computer intrusion offenses.”

Meli is alleged to have made available malware solutions at the very least since 2012 by means of on-line hacking message boards, sharing e-books, and aiding other criminals use RATs to carry out cyber attacks. Prior to Warzone RAT, he experienced marketed one more RAT identified as Pegasus RAT.
Like Meli, Odinakachi also furnished on the net client guidance to purchasers of Warzone RAT malware involving June 2019 and no previously than March 2023. The two people had been arrested on February 7, 2024.
Warzone RAT, also regarded as Ave Maria, was first documented by Yoroi in January 2019 as section of a cyber attack concentrating on an Italian firm in the oil and gasoline sector in the direction of the stop of 2018 utilizing phishing e-mails bearing bogus Microsoft Excel files exploiting a acknowledged security flaw in the Equation Editor (CVE-2017-11882).
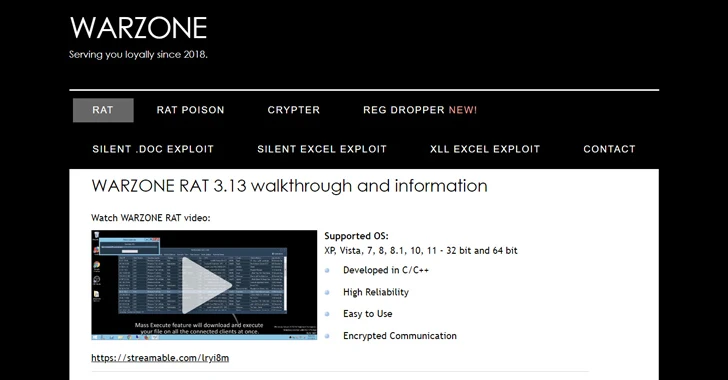
Sold underneath the malware-as-a-provider (Maas) product for $38 a thirty day period (or $196 for a year), it features as an information and facts stealer and facilitates distant control, therefore making it possible for risk actors to commandeer the contaminated hosts for follow-on exploitation.
Some of the notable characteristics of the malware include things like the skill to browse victim file programs, acquire screenshots, file keystrokes, steal target usernames and passwords, and activate the computer’s webcams with no the victim’s expertise or consent.
“Ave Maria attacks are initiated via phishing email messages, as soon as the dropped payload infects the victim’s device with the malware, it establishes interaction with the attacker’s command-and-manage (C2) server on non-HTTP protocol, following decrypting its C2 connection employing RC4 algorithm,” Zscaler ThreatLabz stated in early 2023.

On a single of the now-dismantled internet sites, which had the tagline “Serving you loyally considering that 2018,” the developers of the C/C++ malware described it as responsible and simple to use. They also delivered the skill for buyers to speak to them by using email (solmyr@warzone[.]ws), Telegram (@solwz and @sammysamwarzone), Skype (vuln.hf), as very well as via a committed “customer region.”
An further make contact with avenue was Discord, wherever the end users had been asked to get in contact with an account with the ID Meli#4472. An additional Telegram account linked to Meli was @daniel96420.
Exterior of cybercrime groups, the malware has also been put to use by many state-of-the-art danger actors like YoroTrooper as perfectly as those people involved with Russia in excess of the earlier yr.
The DoJ claimed the U.S. Federal Bureau of Investigation (FBI) covertly bought copies of Warzone RAT and verified its nefarious features. The coordinated work out included aid from authorities in Australia, Canada, Croatia, Finland, Germany, Japan, Malta, the Netherlands, Nigeria, Romania, and Europol.
Uncovered this report intriguing? Adhere to us on Twitter and LinkedIn to study a lot more exclusive content material we publish.
Some areas of this article are sourced from:
thehackernews.com

 Alert: New Stealthy “RustDoor” Backdoor Targeting Apple macOS Devices
Alert: New Stealthy “RustDoor” Backdoor Targeting Apple macOS Devices