Cybersecurity scientists have found that it is really possible for threat actors to exploit a very well-recognized utility termed command-not-discovered to recommend their very own rogue packages and compromise methods managing Ubuntu running technique.
“Even though ‘command-not-found’ serves as a practical instrument for suggesting installations for uninstalled instructions, it can be inadvertently manipulated by attackers through the snap repository, leading to deceptive recommendations of malicious offers,” cloud security organization Aqua mentioned in a report shared with The Hacker News.
Put in by default on Ubuntu programs, command-not-found implies offers to install in interactive bash periods when trying to operate instructions that are not obtainable. The solutions include things like equally the Highly developed Packaging Instrument (APT) and snap offers.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
When the tool works by using an inside database (“/var/lib/command-not-discovered/commands.db”) to propose APT packages, it depends on the “recommend-snap” command to counsel snaps that offer the supplied command.

Therefore, ought to an attacker be equipped to activity this system and have their malicious package recommended by the ‘command-not-found’ package, it could pave the way for application source chain attacks.
Aqua said it located a likely loophole whereby the alias mechanism can be exploited by the risk actor to possibly register the corresponding snap name connected with an alias and trick users into setting up the destructive bundle.
What is more, an attacker could assert the snap identify associated to an APT bundle and upload a destructive snap, which then ends up getting instructed when a consumer varieties in the command on their terminal.

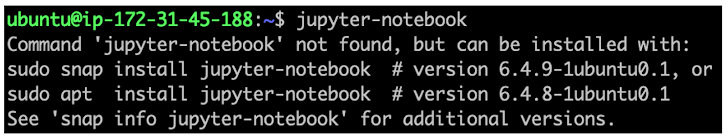
“The maintainers of the ‘jupyter-notebook’ APT bundle had not claimed the corresponding snap name,” Aqua stated. “This oversight left a window of chance for an attacker to claim it and add a destructive snap named ‘jupyter-notebook.'”
To make matters worse, command-not-identified utility implies the snap package higher than the respectable APT package deal for jupyter-notebook, deceptive end users into putting in the phony snap package.
As many as 26% of the APT package commands are susceptible to impersonation by destructive actors, Aqua pointed out, presenting a sizeable security risk, as they could be registered below an attacker’s account.
A 3rd class entails typosquatting attacks in which typographical faults manufactured by end users (e.g., ifconfigg rather of ifconfig) are leveraged to propose bogus snap packages by registering a fraudulent bundle with the identify “ifconfigg.”

In these types of a scenario, command-not-identified “would mistakenly match it to this incorrect command and suggest the malicious snap, bypassing the suggestion for ‘net-tools’ entirely,” Aqua researchers spelled out.
Describing the abuse of the command-not-observed utility to endorse counterfeit deals as a urgent concern, the firm is urging end users to validate the supply of a bundle just before set up and look at the maintainers’ trustworthiness.
Developers of APT and snap offers have also been recommended to register the associated snap name for their commands to prevent them from currently being misused.
“It remains uncertain how extensively these capabilities have been exploited, underscoring the urgency for heightened vigilance and proactive defense strategies,” Aqua reported.
Identified this post interesting? Abide by us on Twitter and LinkedIn to go through more exclusive articles we post.
Some elements of this article are sourced from:
thehackernews.com

 Cybersecurity Tactics FinServ Institutions Can Bank On in 2024
Cybersecurity Tactics FinServ Institutions Can Bank On in 2024