Ukraine’s technological security and intelligence support is warning of a new wave of cyber attacks that are aimed at gaining entry to users’ Telegram accounts.
“The criminals despatched messages with malicious hyperlinks to the Telegram web site in order to get unauthorized accessibility to the documents, which includes the possibility to transfer a one particular-time code from SMS,” the State Service of Unique Interaction and Facts Protection (SSSCIP) of Ukraine explained in an inform.
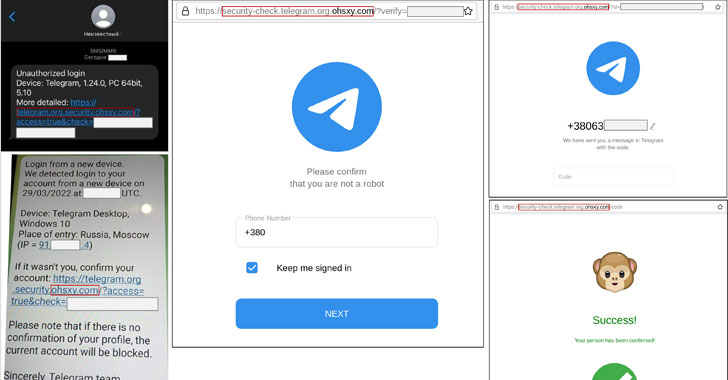
The attacks originate with Telegram messages alerting recipients that a login had been detected from a new gadget found in Russia, urging the people to verify their accounts by clicking on a hyperlink.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
The URL, in fact a phishing domain, prompts the victims to enter their phone figures as effectively as the a single-time passwords sent by using SMS that are then used by the danger actors to consider over the accounts.
The modus operandi mirrors that of an previously phishing attack that was disclosed in early March that leveraged compromised inboxes belonging to distinct Indian entities to send phishing e-mails to consumers of Ukr.net to hijack the accounts.
In one more social engineering marketing campaign observed by Ukraine’s Computer Crisis Response Crew (CERT-UA), war-associated email lures had been sent to Ukrainian governing administration companies to deploy a piece of espionage malware.
The e-mails come with an HTML file attachment (“War Criminals of the Russian Federation.htm”), opening which culminates in the down load and execution of a PowerShell-primarily based implant on the infected host.
CERT-UA attributed the attack to Armageddon, a Russia-based menace actor with ties to the Federal Security Assistance (FSB) that has a record of placing Ukrainian entities due to the fact at least 2013.
In February 2022, the hacking group was related to espionage attacks targeting governing administration, navy, non-authorities companies (NGO), judiciary, regulation enforcement, and non-revenue organizations with the most important objective of exfiltrating delicate information.
Armageddon, also acknowledged by the moniker Gamaredon, is also considered to have singled out Latvian govt officers as element of a relevant phishing attack to the conclude of March 2022, employing war-themed RAR archives to supply malware.
Other phishing campaigns documented by CERT-UA in current weeks have deployed a variety of malware, which include GraphSteel, GrimPlant, HeaderTip, LoadEdge, and SPECTR, not to mention a Ghostwriter-spearheaded operation to install the Cobalt Strike article-exploitation framework.
The disclosure will come as many sophisticated persistent risk (APT) groups from Iran, China, North Korea, and Russia have capitalized on the ongoing Russo-Ukrainian war as a pretext to backdoor target networks and phase other destructive pursuits.
Identified this post attention-grabbing? Adhere to THN on Fb, Twitter and LinkedIn to read through a lot more distinctive content material we put up.
Some sections of this report are sourced from:
thehackernews.com



 Report: Apple “neglects” to patch zero-days for older macOS versions
Report: Apple “neglects” to patch zero-days for older macOS versions