Ukrainian military entities are the focus on of a phishing marketing campaign that leverages drone manuals as lures to provide a Go-based open-resource submit-exploitation toolkit referred to as Merlin.
“Given that drones or Unmanned Aerial Automobiles (UAVs) have been an integral tool applied by the Ukrainian navy, malware-laced lure files themed as UAVs assistance manuals have begun to surface area,” Securonix scientists Den Iuzvyk, Tim Peck, and Oleg Kolesnikov explained in a report shared with The Hacker News.
The cybersecurity company is tracking the marketing campaign below the name STARK#VORTEX.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
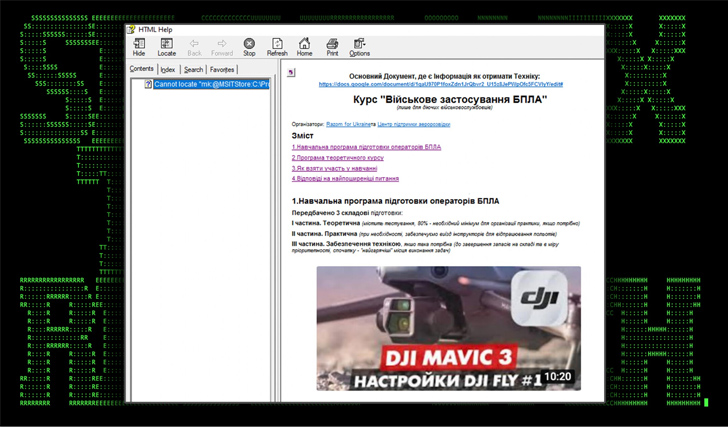
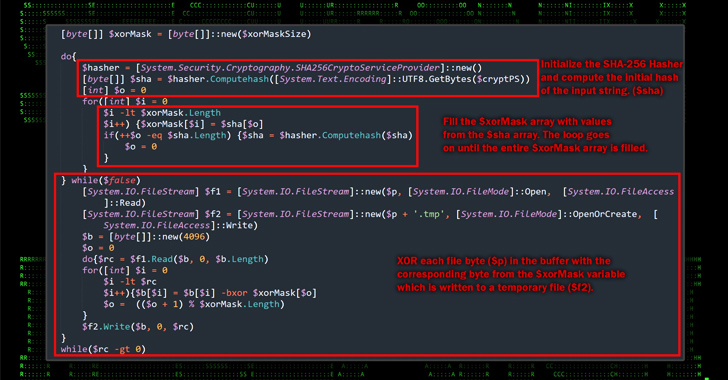
The commencing stage of the attack is a Microsoft Compiled HTML Assistance (CHM) file that, when opened, operates malicious JavaScript embedded inside 1 of the HTML internet pages to execute PowerShell code built to get hold of a distant server to fetch an obfuscated binary.

The Windows-based mostly payload is decoded to extract the Merlin Agent, which, in switch, is configured to communicate with a command-and-management (C2) server for put up-exploitation actions, successfully seizing manage above the host.
“Even though the attack chain is fairly basic, the attackers leveraged some pretty intricate TTPs and obfuscation strategies in purchase to evade detection,” the scientists claimed.
This is the first time Ukrainian authorities companies have been qualified applying Merlin. In early August 2023, the Personal computer Unexpected emergency Reaction Workforce of Ukraine (CERT-UA) disclosed a identical attack chain that employs CHM information as decoys to infect the computer systems with the open-supply software.
CERT-UA attributed the intrusions to a risk actor it monitors beneath the title UAC-0154.
“Data files and files employed in the attack chain are pretty able of bypassing defenses,” the researchers stated.
Impending WEBINARFight AI with AI — Battling Cyber Threats with Up coming-Gen AI Equipment
Prepared to deal with new AI-pushed cybersecurity troubles? Join our insightful webinar with Zscaler to deal with the increasing threat of generative AI in cybersecurity.
Supercharge Your Techniques
“Usually receiving a Microsoft support file above the internet would be considered strange. Even so, the attackers framed the entice documents to appear as anything an unsuspecting target could possibly assume to surface in a assist-themed document or file.”
The growth arrives months right after the CERT-UA explained it detected an unsuccessful cyber attack against an unnamed critical electrical power infrastructure facility in the state undertaken by the Russian state-sponsored crew identified as APT28.
Identified this short article exciting? Observe us on Twitter and LinkedIn to go through a lot more special written content we submit.
Some areas of this article are sourced from:
thehackernews.com

 Watch the Webinar — AI vs. AI: Harnessing AI Defenses Against AI-Powered Risks
Watch the Webinar — AI vs. AI: Harnessing AI Defenses Against AI-Powered Risks