The time concerning a vulnerability getting discovered and hackers exploiting it is narrower than at any time – just 12 days. So it tends to make perception that corporations are beginning to identify the relevance of not leaving prolonged gaps concerning their scans, and the term “constant vulnerability scanning” is turning out to be much more popular.
Hackers will not wait for your next scan
Just one-off scans can be a simple ‘one-and-done’ scan to verify your security posture to prospects, auditors or investors, but a lot more usually they refer to periodic scans kicked off at semi-normal intervals – the market typical has typically been quarterly.
These periodic scans give you a place-in-time snapshot of your vulnerability status – from SQL injections and XSS to misconfigurations and weak passwords. Great for compliance if they only request for a quarterly vulnerability scan, but not so excellent for ongoing oversight of your security posture, or a robust attack surface administration application. With a clean CVE produced each and every 20 minutes, you run the risk of obtaining an outdated watch of your security at any given instant.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
It is really hugely likely that some of the 25,000 CVE vulnerabilities disclosed last yr alone will influence you and your organization in the gaps involving 1-off or semi-normal scans. Just look at how usually you have to update the program on your laptop computer… It can choose months or even months ahead of vulnerabilities are patched also, by which time it may perhaps be too late. With the probable harm to your organization these vulnerabilities could result in, there’s simply just no substitute for constant scanning in 2023.
Steady vulnerability scanning delivers 24/7 checking of your IT setting and automation to decrease the stress on IT teams. This usually means issues can be found and set speedier, closing the door on hackers and opportunity breaches.
The sluggish rate of compliance
Let us be trustworthy, a large amount of businesses commence their cyber security journey because somebody tells them they have to, no matter whether that’s a consumer or market compliance framework. And a good deal of the requirements in this house can just take time to evolve, nevertheless citing items like an “annual penetration test” or “quarterly vulnerability scan”. These are legacy ideas from several years in the past when attackers ended up couple of on the floor, and these things had been found as ‘nice to have.’
As a end result, several businesses however treat vulnerability scanning as a awesome-to-have or a compliance box to tick. But there is a environment of change in between semi-typical scanning and suitable, constant vulnerability testing and management – and comprehending that variation is critical for improving upon security relatively than just shelling out money on it.
The easy reality is that new vulnerabilities are disclosed every single day, so you can find generally the possible for a breach, even much more so if you might be frequently updating cloud products and services, APIs, and programs. Just one small alter or new vulnerability launch is all it can take to go away yourself uncovered. It truly is no lengthier about ticking boxes – continual coverage is now a ‘must have,’ and companies who are much more mature in their cyber security journey recognize it.
Steady attack surface area checking
It truly is not just new vulnerabilities that are important to observe. Each and every working day, your attack floor changes as you incorporate or remove devices from your network, expose new companies to the internet, or update your purposes or APIs. As this attack floor variations, new vulnerabilities can be uncovered.
To capture new vulnerabilities in advance of they are exploited, you need to know what is actually uncovered and where – all the time. Quite a few legacy equipment really don’t provide the ideal degree of detail or small business context to prioritize vulnerabilities they handle all attack vectors (exterior, inner, cloud) the exact same. Effective continual attack area monitoring ought to deliver the business context and deal with all attack vectors – like cloud integrations and network changes – to be actually effective.
Attack surface management is no longer just a specialized thing to consider either. Boards are ever more recognizing its great importance as part of a sturdy cyber security method to safeguard operations, when it really is a key need for lots of cyber insurance plan premiums.
How a lot is too significantly?
Continual scanning won’t mean continuous scanning, which can produce a barrage of alerts, triggers and phony positives that are virtually unattainable to hold on major off. This inform tiredness can gradual down your techniques and applications, and tie your group up in knots prioritizing issues and weeding out phony positives.
Intruder is a modern security tool that cleverly receives spherical this issue by kicking off a vulnerability scan when a network improve is detected or a new exterior IP tackle or hostname is spun up in your cloud accounts. This indicates your vulnerability scans would not overload your crew or your systems but will decrease the window of chance for hackers.
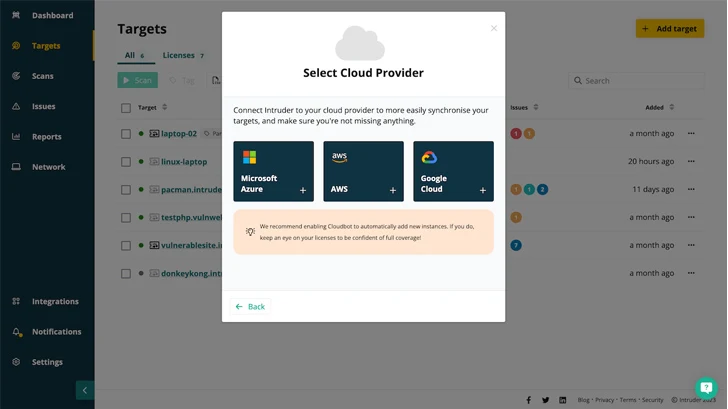 Modern day security tools like Intruder integrate with your cloud providers, so it is easy to see which units are reside and to operate security checks when something changes.
Modern day security tools like Intruder integrate with your cloud providers, so it is easy to see which units are reside and to operate security checks when something changes.
How generally do you need to have to scan for compliance?
This is dependent on which compliance you might be hunting for! While SOC 2 and ISO 27001 give you some wiggle space, HIPAA, PCI DSS and GDPR explicitly condition scanning frequency, from quarterly to at the time a 12 months. But using these requirements to determine the appropriate time and frequency for vulnerability scanning might not be correct for your business enterprise. And executing so will increase your exposure to security hazards thanks to the promptly shifting security landscape.
If you want to in fact protected your electronic property and not just tick a box for compliance, you will need to go over and past the prerequisites stipulated in these benchmarks – some of which are out of phase with present-day security demands. Today’s agile SaaS companies, online shops that approach large volume transactions or get card payments, and any person running in highly-regulated industries like health care and economical companies, want continual scanning to be certain they are appropriately secured.
Harder, far better, a lot quicker, much better
Regular vulnerability administration is damaged. With technology in consistent flux as you spin up new cloud accounts, make network alterations or deploy new systems, just one-off scans are no extended sufficient to retain up with the speed with the alter.
When it will come to closing the cyber security gaps among scans that attackers appear to exploit, quicker is far better than afterwards, but continuous is ideal. Constant scanning minimizes the time to come across and take care of vulnerabilities, delivers wealthy threat facts and remediation suggestions, and minimizes your risk by prioritizing threats in accordance to the context of your company requirements.
About Intruder
Intruder is a cyber security enterprise that assists businesses decrease their attack surface area by providing constant vulnerability scanning and penetration tests providers. Intruder’s strong scanner is made to promptly recognize large-effects flaws, alterations in the attack surface area, and quickly scan the infrastructure for emerging threats. Functioning countless numbers of checks, which include determining misconfigurations, missing patches, and web layer issues, Intruder would make company-quality vulnerability scanning easy and obtainable to everyone. Intruder’s significant-top quality stories are fantastic to go on to prospective clients or comply with security regulations, this sort of as ISO 27001 and SOC 2.
Intruder delivers a 14-working day free of charge demo of its vulnerability evaluation platform. Pay a visit to their web site now to just take it for a spin!
Identified this post exciting? Stick to us on Twitter and LinkedIn to study far more distinctive content we publish.
Some pieces of this posting are sourced from:
thehackernews.com


 Google Play Protect Introduces Real-Time Code-Level Scanning for Android Malware
Google Play Protect Introduces Real-Time Code-Level Scanning for Android Malware