Earlier this yr, threat actors infiltrated Mailchimp, the popular SaaS email marketing system. They seen over 300 Mailchimp purchaser accounts and exported audience information from 102 of them. The breach was preceded by a successful phishing endeavor and led to malicious attacks from Mailchimp’s customers’ finish people.
Three months afterwards, Mailchimp was strike with another attack. When all over again, an employee’s account was breached following a effective phishing try.
Whilst the id of the Mailchimp accounts that experienced been compromised wasn’t launched, it can be easy to see how consumer permission options could have played a position in the attack. At the time danger detectors breached the method, they experienced the accessibility desired to make the most of an interior software that enabled them to find the data they have been searching for. The attack ended when security teams have been capable to terminate person accessibility, despite the fact that facts which experienced now been downloaded remained in the menace actor’s palms.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
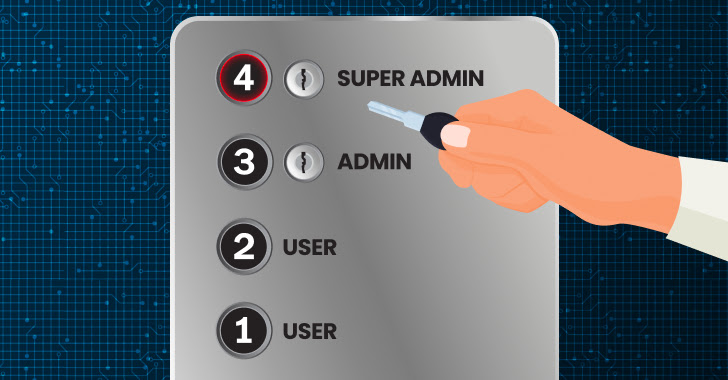
Introducing consumer permissions, by way of position-dependent account regulate (RBAC), could have seriously minimal the damage brought about by the breach. Had the rule of the very least privilege been utilized, it really is probable that the breached account would not have afforded access to the interior applications that have been utilized in the attack. On top of that, reduced access could possibly have absolutely prevented the attack or restricted the number of influenced accounts to far less than the 100 which ended up in the long run compromised.
Guard SaaS knowledge as if your company’s potential relies upon on it. Timetable a demo for more.
What Are User Permissions?
SaaS consumer permissions enable application entrepreneurs to restrict a user’s assets and actions primarily based on the user’s purpose. Referred to as RBAC, it is the authorization set that grants browse or produce entry, assigns privileges to higher-level customers, and decides entry amounts to corporation details.
What is the Intent of the “Rule of Least Privilege”?
The rule of minimum privilege is an vital security concept that supplies the minimum amount of money of accessibility required for people to execute their job capabilities. In observe, it cuts down the attack surface by restricting higher-level obtain to a few privileged men and women. If a low-privilege consumer account is breached, the risk actor would have significantly less access to delicate data contained in just the application.
Are your SaaS applications pursuing the rule of minimum privilege? Schedule a demo to understand more.
Why Do User Permissions Issue for Security?
App administrators often grant whole access to team customers, specifically when dealing with a compact user team. As organization people alternatively than security pros, they will not constantly figure out the degree of risk in granting individuals obtain permissions. Also, they prefer to give total authorization rather than be asked for certain permissions afterwards on.
Regretably, this strategy can place sensitive info documents at risk. Consumer permissions support determine the exposed data in the celebration of a breach. By shielding facts guiding a authorization established, risk actors that entry a user identity are restricted to the data obtainable to their victim.
Loose person permissions also make it easier for threat actors to have out automatic attacks. Having a number of users with vast API permissions will make it less difficult for cybercriminals to breach a SaaS app and both automate ransomware or steal info.
Why Are User Entry Evaluations Vital?
Consumer access assessments are in essence audits that seem at end users and their obtain. They show security team members and app house owners the degree of obtain every user has and enables them to alter authorization concentrations as necessary.
This is essential, as it will help discover consumers who may have switched roles or groups within just the company but retained an needless level of permissions, or alerts security teams regarding employees whose actions have deviated from usual behaviors to contain suspicious conduct. Also, it aids detect previous staff members who however have entry and high-privilege permissions.
Accessibility Opinions need to get spot at predetermined intervals, guaranteeing that unwanted permissions are determined within a established time frame.
Conclusion
User permissions are normally a misunderstood security aspect. It guards corporations from the two external attacks and internal information-sharing glitches.
An SSPM resolution, like Adaptive Shield, permits efficient consumer authorization management, giving security staff and application house owners the self confidence to know the extent of any user permission and see that user’s SaaS security cleanliness. This true-time look at of end users is far much more efficient than Person Accessibility Audits, which only present a snapshot watch of the users’ permissions at a precise minute in time.
Hunting for more visibility into your Saas buyers? Schedule a demo these days for whole visibility.
Discovered this report intriguing? Stick to us on Twitter and LinkedIn to go through extra special information we write-up.
Some parts of this report are sourced from:
thehackernews.com

 FCC plans strict overhaul of 15-year-old US data breach regulations
FCC plans strict overhaul of 15-year-old US data breach regulations