The Zerobot DDoS botnet has obtained significant updates that grow on its ability to target a lot more internet-related equipment and scale its network.
Microsoft Danger Intelligence Middle (MSTIC) is tracking the ongoing threat less than the moniker DEV-1061, its designation for mysterious, rising, or creating exercise clusters.
Zerobot, first documented by Fortinet FortiGuard Labs earlier this month, is a Go-based mostly malware that propagates through vulnerabilities in web applications and IoT gadgets like firewalls, routers, and cameras.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
“The most recent distribution of Zerobot incorporates added capabilities, this sort of as exploiting vulnerabilities in Apache and Apache Spark (CVE-2021-42013 and CVE-2022-33891 respectively), and new DDoS attack capabilities,” Microsoft researchers said.

Also known as ZeroStresser by its operators, the malware is provided as a DDoS-for-employ the service of service to other criminal actors, with the botnet advertised on social media by its operators.
Microsoft mentioned that a single domain with connections to Zerobot – zerostresser[.]com – was among the the 48 domains that had been seized by the U.S. Federal Bureau of Investigation (FBI) this thirty day period for giving DDoS attack capabilities to shelling out shoppers.
The most recent variation of Zerobot spotted by Microsoft not only targets unpatched and improperly secured products, but also attempts to brute-force above SSH and Telnet on ports 23 and 2323 for spreading to other hosts.
The checklist of freshly extra recognized flaws exploited by Zerobot 1.1 is as follows –
- CVE-2017-17105 (CVSS rating: 9.8) – A command injection vulnerability in Zivif PR115-204-P-RS
- CVE-2019-10655 (CVSS rating: 9.8) – An unauthenticated distant code execution vulnerability in Grandstream GAC2500, GXP2200, GVC3202, GXV3275, and GXV3240
- CVE-2020-25223 (CVSS score: 9.8) – A distant code execution vulnerability in the WebAdmin of Sophos SG UTM
- CVE-2021-42013 (CVSS rating: 9.8) – A distant code execution vulnerability in Apache HTTP Server
- CVE-2022-31137 (CVSS rating: 9.8) – A distant code execution vulnerability in Roxy-WI
- CVE-2022-33891 (CVSS score: 8.8) – An unauthenticated command injection vulnerability in Apache Spark
- ZSL-2022-5717 (CVSS score: N/A) – A remote root command injection vulnerability in MiniDVBLinux
On thriving infection, the attacks chain proceeds to download a binary named “zero” for a specific CPU architecture that enables it to self-propagate to far more susceptible devices exposed on line.
On top of that, Zerobot is mentioned to proliferate by scanning and compromising gadgets with known vulnerabilities that are not involved in the malware executable, these kinds of as CVE-2022-30023, a command injection vulnerability in Tenda GPON AC1200 routers.
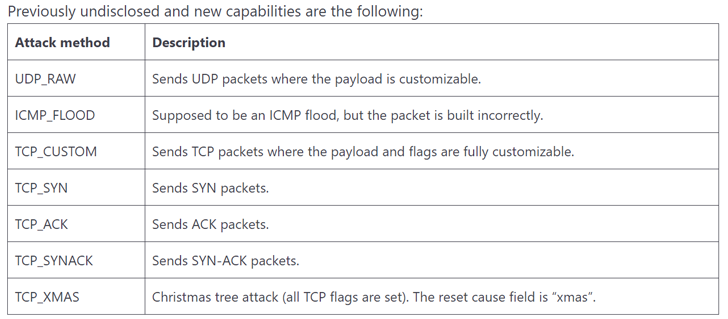
Zerobot 1.1 further more incorporates 7 new DDoS attack techniques by creating use of protocols this kind of as UDP, ICMP, and TCP, indicating “continual evolution and quick addition of new abilities.”
“The change toward malware as a provider in the cyber economy has industrialized attacks and has made it much easier for attackers to buy and use malware, create and maintain obtain to compromised networks, and use completely ready-designed instruments to accomplish their attacks,” the tech giant stated.
Observed this short article interesting? Follow us on Twitter and LinkedIn to read additional exclusive material we publish.
Some areas of this article are sourced from:
thehackernews.com


 Ransomware Attack Hits The Guardian Newspaper
Ransomware Attack Hits The Guardian Newspaper