A lack of consciousness about where by and how open-supply libraries are being employed is problematic, scientists say.
A complete 70 per cent of apps staying used now have at minimum just one stability flaw stemming from the use of an open-supply library.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
In accordance to Veracode’s yearly Point out of Software package Stability report, these open-supply libraries – no cost, centralized code repositories that offer ready-produced application “building blocks” for developers – are not only ubiquitous but also risky.
The evaluation examined 351,000 exterior libraries in 85,000 programs, and uncovered that open-resource libraries are incredibly, really common. For instance, most JavaScript applications comprise hundreds of open up-supply libraries – some have much more than 1,000 diverse libraries. In addition, most languages element the identical set of core libraries.

“JavaScript and PHP in particular have numerous core libraries that are in just about just about every application,” in accordance to the report.
These libraries, like other program, have bugs. The situation is that thanks to code re-use, a single bug can affect hundreds of programs.
“Prominent in virtually each individual software currently, open up-supply libraries make it possible for builders to transfer speedier by rapidly incorporating standard features,” according to Veracode. “In reality, it would be nearly unattainable to innovate with software program devoid of these libraries. Nevertheless, deficiency of recognition about where and how open resource libraries are currently being employed and their hazard aspects is a problematic apply.”
4 most important libraries characterize the vast majority of the open-supply bugs located in apps: Swift, .Internet, Go and PHP.
Swift has specialized use in the Apple ecosystem, and has the optimum density of flaws, in accordance to Veracode. Even so, it also has an over-all low proportion of flawed libraries in conditions of quantity.
.Internet meanwhile has the least expensive proportion of flawed libraries out of the 4, and on a populace that is more than 17 periods more substantial than Swift.
Go has a substantial proportion of libraries with flaws, but an over-all minimal number of flaws for every personal library. And PHP has a higher amount of flawed libraries than Go – but much more double the density of flaws in a given library.

The organization also identified that cross-internet site scripting (XSS) is the most widespread vulnerability group observed in open up-source libraries – present in 30 per cent of them. This is adopted by insecure deserialization (23.5 %) and broken entry control (20.3 p.c).
“We located insecure deserialization was a relatively scarce flaw among in-property applications (position eighth out of 10),” according to the report. “Having such a higher position when on the lookout at libraries is troubling as this classification of flaws can outcome in unanticipated code paths remaining executed, which signifies that portions of libraries that we are not even intending to use could be inserted into the execution path of their internet hosting purposes via use of this flaw.”
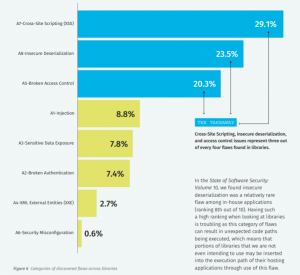
Share of bug forms found stemming from open up-source. Simply click to enlarge.
The information also confirmed that most flawed libraries conclusion up in code indirectly – thanks to cascading interdependencies. Developers could use one library – but unbeknownst to them, the library that they’re working with has pulled in code from an solely distinct open-supply library to underpin it.
“Forty-seven % of the flawed libraries in programs are transitive – in other words, they are not pulled in straight by builders, but are becoming pulled in by the initial library (42 percent are pulled in directly, 12 percent are both). This means that builders are introducing a great deal additional code, and usually flawed code, than they could possibly be anticipating.”
The very good news is that addressing protection flaws in these libraries is not a substantial lift.
“Most library-launched flaws (almost 75 p.c) in apps can be dealt with with only a minor variation update significant library upgrades are not commonly demanded,” according to the Veracode report. “This information place suggests that this issue is one particular of discovery and monitoring, not enormous refactoring of code.”
Involved about the IoT security worries corporations encounter as much more linked devices run our enterprises, travel our production traces, track and provide health care to clients, and much more? On June 3 at 2 p.m. ET, be part of renowned safety technologist Bruce Schneier, Armis CISO Curtis Simpson and Threatpost for a Absolutely free webinar, Taming the Unmanaged and IoT Machine Tsunami. Get unique insights on how to take care of this new and developing attack surface. Be sure to register listed here for this sponsored webinar.


 Critical Cisco Bug in Unified CCX Allows Remote Code Execution
Critical Cisco Bug in Unified CCX Allows Remote Code Execution