On the in addition side, only instances with non-common not encouraged configurations are vulnerable. On the downside, people configurations are not simple to monitor down, and it is uncomplicated as pie to exploit.
Researchers have shared aspects about a now-patched, significant-severity security bug in the Apache Cassandra open up-source NoSQL dispersed databases that’s easy to exploit and, if remaining unpatched, could enable attackers to gain remote code execution (RCE).
The bug, which requires how Cassandra makes person-described-capabilities (UDFs) to accomplish tailor made processing of facts, is tracked as CVE-2021-44521, with a substantial-severity score of 8.4.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
The vulnerability was discovered by JFrog’s Security Study crew. In a Tuesday writeup, JFrog security researcher Omer Kaspi stated that on the upside, the only Cassandra programs that are susceptible to the flaw are those with a distinct, non-regular and, specially, not advisable configuration.
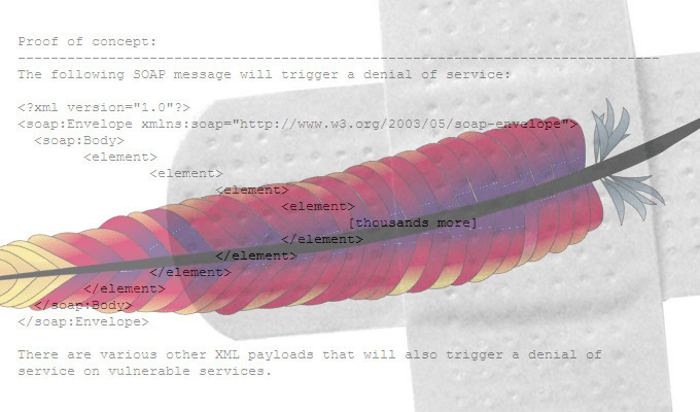
On the downside, it is a snap to exploit, JFrog has now produced a proof-of-principle (PoC) exploit. An additional downside: This database is all over the place.
“This Apache security vulnerability is quick to exploit and has the prospective to wreak havoc on devices, but thankfully only manifests in non-default configurations of Cassandra,” Kaspi said in his writeup.
What, and The place, Exactly, is Cassandra?
Cassandra is a very scalable, broadly made use of distributed databases recognized for staying economical and extremely accessible, offered that these databases never have a solitary place of failure: a significant moreover for companies that can not lose facts or endure technique downtime. It is also recognised for currently being able to manage large volumes of details across many servers, with quick writes of huge amounts of information that really don’t bathroom down its read efficiency.
“Cassandra is a highly scalable, distributed NoSQL databases that is incredibly well known owing to the rewards of its distributed mother nature,” Kaspi said.
As these types of, it is made use of by enterprises with huge, large names, Kaspi famous, including Netflix, Twitter, Urban Airship, Frequent Get in touch with, Reddit, Cisco, OpenX, Digg, CloudKick, Ooyala and far more. The researcher added that Cassandra is also incredibly well known in DevOps and cloud-indigenous development circles, “as can be viewed by its support in CNCF [cloud native Computing Foundation] tasks (these as Jaeger).”
(Jaeger is an open-source, close-to-close dispersed tracing system developed to keep an eye on and troubleshoot transactions in advanced distributed programs.)
“Some firms even present cloud-based turnkey solutions primarily based on Cassandra, this sort of as DataStax (a serverless, multi-cloud DBaaS),” Kaspi pointed out.
Digging Out the Risk Will Be a Royal Pain
Given Cassandra’s reputation, the simple fact that the flaw requires non-default person configuration configurations to exploit may possibly not be all that comforting, security specialists told Threatpost.
John Bambenek, principal threat hunter at the electronic IT and security operations business Netenrich, instructed Threatpost on Wednesday that he suspects that the non-default options are “common in many applications around the globe.”
The predicament isn’t looking as undesirable as Log4j, but it could however probably be prevalent, and it’s likely to be a chore to dig out susceptible installations, Bambenek claimed by using email. “Unfortunately, there is no way to know precisely how many installations are susceptible, and this is most likely the form of vulnerability that will be missed by automated vulnerability scanners,” he claimed. “Enterprises will have to go into the configuration documents of just about every Cassandra occasion to determine what their risk is.”
Casey Bisson, head of product or service and developer relations at code-security methods provider BluBracket, told Threatpost that the issue could have “a broad effects with extremely significant repercussions,” as in, “Threat actors may be capable to go through or manipulate sensitive knowledge in susceptible configurations.”
Bisson advised an additional prospective hazard: Have been a danger actor to obtain compose obtain to a databases instance’s configuration, they could help the vulnerability with out the operators being mindful.
The Coronary heart of the Trouble: JavaScript’s Use of the Nashorn Motor
When it will come to creating UDFs for personalized knowledge processing, Cassandra can produce them by default in Java and JavaScript. When they are published in JavaScript, Cassandra makes use of the Nashorn engine in the Java Runtime Environment (JRE): a JavaScript engine that operates on top of the Java Digital Device (JVM).
Therein lies the challenge: “Nashorn is not confirmed to be safe when accepting untrusted code. Consequently, any company that makes it possible for these types of habits will have to normally wrap the Nashorn execution in a sandbox,” in accordance to JFrog’s writeup. “For instance, jogging the following Nashorn JavaScript code will allow execution of an arbitrary shell command – java.lang.Runtime.getRuntime().exec(“touch hacked”).
Some assignments this kind of as NashornEscape, employ a sandbox to protected Nashorn code execution, Kaspi stated.
“The Nashorn motor offers entry to arbitrary Java classes by applying Java.sort.
For case in point: var Method = Java.variety(“java.lang.System”) will permit us to obtain the java.lang.Process offer by using the System variable,” he continued.
People with enough permissions can generate arbitrary capabilities by working with the develop perform question.
Though studying the Cassandra UDF sandbox implementation, scientists realized that a combine of distinct (non-default) configuration choices could enable them to abuse the Nashorn engine, escape the sandbox and realize RCE: the vulnerability claimed as CVE-2021-44521.
Mitigation and Resolve
JFrog hugely recommends that all Apache Cassandra consumers enhance to a person of the next variations, which resolves the bug:
- 3..x buyers need to improve to 3..26
- 3.11.x consumers really should upgrade to 3.11.12
- 4..x consumers must up grade to 4..2
For these end users who cannot update their scenarios, JFrog recommends these mitigations:
- If UDFs are not actively used, they can be absolutely disabled by location allow_consumer_outlined_functions to false (which is the default value)
- If UDFs are desired, established enable_user_described_functions_threads to genuine (which is the default benefit)
- Take away the permissions of generating, altering and executing capabilities for untrusted people by taking away the subsequent permissions: ALL Functions, ALL Features IN KEYSPACE and Function for Create, Alter and EXECUTE queries.
Some sections of this report are sourced from:
threatpost.com

 Critical VMware Bugs Open ESXi, Fusion & Workstation to Attackers
Critical VMware Bugs Open ESXi, Fusion & Workstation to Attackers