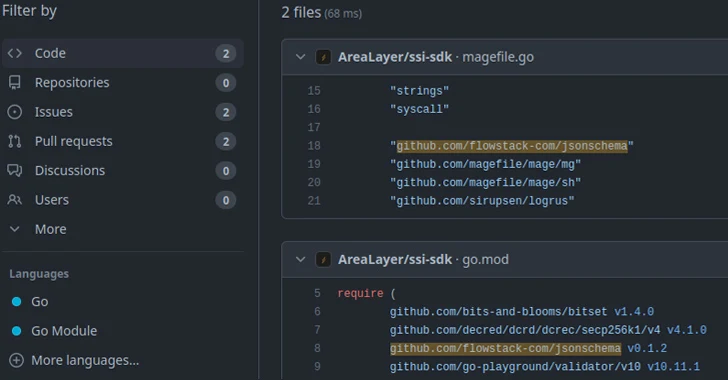
New analysis has observed that in excess of 15,000 Go module repositories on GitHub are vulnerable to an attack identified as repojacking.
“Additional than 9,000 repositories are susceptible to repojacking due to GitHub username improvements,” Jacob Baines, main technology officer at VulnCheck, said in a report shared with The Hacker Information. “Additional than 6,000 repositories had been susceptible to repojacking due to account deletion.”
Collectively, these repositories account for additional no less than 800,000 Go module-variations.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
Approaching WEBINAR Find out Insider Threat Detection with Application Response Tactics
Uncover how application detection, response, and automated actions modeling can revolutionize your defense towards insider threats.
Be part of Now
Repojacking, a portmanteau of “repository” and “hijacking,” is an attack approach that will allow a negative actor to consider advantage of account username variations and deletions to produce a repository with the similar title and the pre-existing username to stage open-supply application provide chain attacks.
Before this June, cloud security firm Aqua exposed that tens of millions of program repositories on GitHub are possible vulnerable to the risk, urging businesses that go through title adjustments to ensure that they still possess their former identify as placeholders to prevent these types of abuse.
Modules penned in the Go programming language are specifically prone to repojacking as unlike other bundle supervisor alternatives like npm or PyPI, they are decentralized due to the reality that they get printed to edition management platforms like GitHub or Bitbucket.
“Any individual can then instruct the Go module mirror and pkg.go.dev to cache the module’s details,” Baines claimed. “An attacker can register the freshly unused username, copy the module repository, and publish a new module to proxy.golang.org and go.pkg.dev.”
To avert developers from pulling down possibly unsafe packages, GitHub has in place a countermeasure known as popular repository namespace retirement that blocks tries to develop repositories with the names of retired namespaces that have been cloned additional than 100 times prior to the owners’ accounts currently being renamed or deleted.
But VulnCheck noted that this defense is not handy when it will come to Go modules as they are cached by the module mirror, therefore obviating the need to have for interacting with or cloning a repository.” In other words, there could be common Go-primarily based modules that have been cloned considerably less than 100 situations, ensuing in a bypass of types.

“However, mitigating all of these repojackings is anything that possibly Go or GitHub will have to choose on,” Baines reported. “A 3rd-party are not able to reasonably sign-up 15,000 GitHub accounts. Right until then, it is really critical for Go developers to be knowledgeable of the modules they use, and the point out of the repository that the modules originated from.”
The disclosure also arrives as Lasso Security said it learned 1,681 uncovered API tokens on Hugging Confront and GitHub, including all those associated with Google, Meta, Microsoft, and VMware, that could be probably exploited to phase offer chain, training info poisoning, and product theft attacks.
Identified this report interesting? Abide by us on Twitter and LinkedIn to examine additional exceptional content material we write-up.
Some areas of this report are sourced from:
thehackernews.com

 New Threat Actor ‘AeroBlade’ Emerges in Espionage Attack on U.S. Aerospace
New Threat Actor ‘AeroBlade’ Emerges in Espionage Attack on U.S. Aerospace