As lots of as 34 Russian-speaking gangs distributing info-stealing malware below the stealer-as-a-assistance model stole no less than 50 million passwords in the initial seven months of 2022.
“The underground market worth of stolen logs and compromised card facts is approximated close to $5.8 million,” Singapore-headquartered Team-IB said in a report shared with The Hacker Information.
Apart from looting passwords, the stealers also harvested 2.11 billion cookie documents, 113,204 crypto wallets, and 103,150 payment playing cards.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
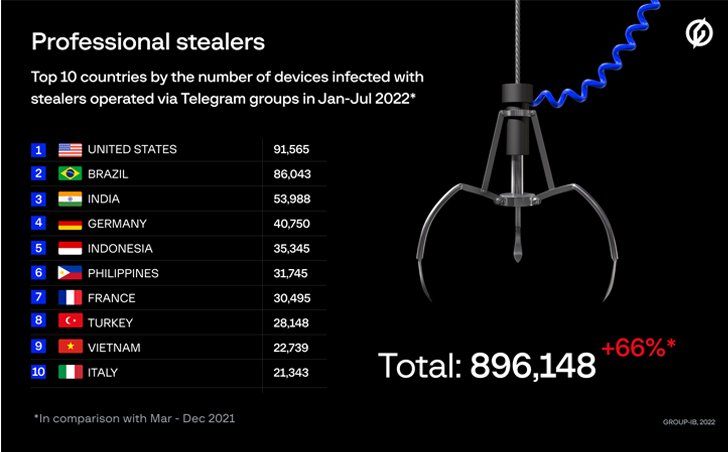
A majority of the victims are located in the U.S., followed by Brazil, India, Germany, Indonesia, the Philippines, France, Turkey, Vietnam, and Italy. In total, 890,000 equipment in 111 international locations ended up infected throughout the time frame.
Group-IB stated the customers of a number of rip-off teams who are propagating the details stealers previously participated in the Classiscam procedure.
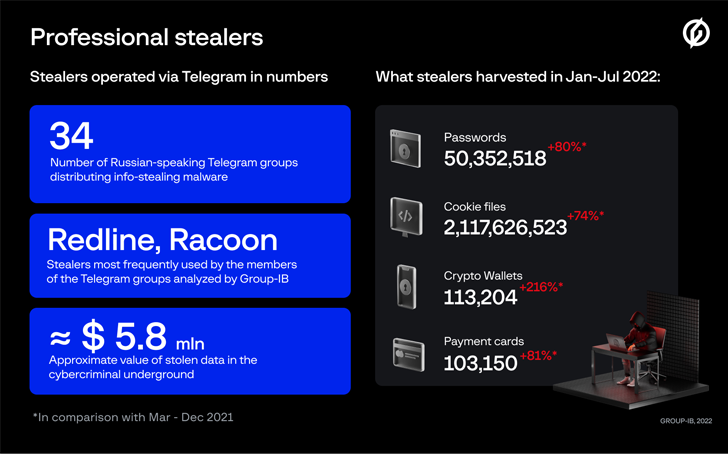
These teams, which are lively on Telegram and have all over 200 members on ordinary, are hierarchical, consisting of directors and personnel (or traffers), the latter of whom are dependable for driving unsuspecting users to information-stealers like RedLine and Raccoon.
This is realized by setting up bait sites that impersonate nicely-acknowledged providers and luring victims into downloading destructive documents. Backlinks to such sites are, in change, embedded into YouTube online video assessments for well-liked video games and lotteries on social media, or shared right with NFT artists.
“Directors typically give workers the two RedLine and Racoon in trade for a share of the stolen facts or money,” the firm claimed. “Some teams use a few stealers at the similar time, when other folks have only just one stealer in their arsenal.”
Pursuing a prosperous compromise, the cyber criminals peddle the stolen facts on the dark web for financial achieve.
The development highlights the critical job played by Telegram in facilitating a selection of criminal activities, including operating as a hub for saying product or service updates, offering shopper aid, and exfiltrating information from compromised gadgets.
The results also observe a new report from SEKOIA, which disclosed that 7 distinctive traffers groups have included an up-and-coming info stealer recognised as Aurora to their toolset.
“The level of popularity of schemes involving stealers can be explained by the lower entry barrier,” Team-IB described. “Rookies do not want to have state-of-the-art complex knowledge as the approach is fully automatic and the worker’s only task is to develop a file with a stealer in the Telegram bot and travel traffic to it.”
Uncovered this posting attention-grabbing? Abide by THN on Facebook, Twitter and LinkedIn to read through extra unique content we put up.
Some areas of this write-up are sourced from:
thehackernews.com

 Ducktail Malware Operation Evolves with New Malicious Capabilities
Ducktail Malware Operation Evolves with New Malicious Capabilities