A person matter is crystal clear. The “business price” of details continues to increase, making it an organization’s most important piece of intellectual home.
From a cyber risk point of view, attacks on facts are the most prominent threat to corporations.
Regulators, cyber insurance plan corporations, and auditors are paying much nearer awareness to the integrity, resilience, and recoverability of group info – as effectively as the IT infrastructure & devices that retail outlet the facts.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
What Influence Does This Have On The Security Of Storage & Backup Programs?
Just a number of many years in the past, nearly no CISO thought that storage & backups were being essential. That is no for a longer time the circumstance nowadays.
Ransomware has pushed backup and restoration again onto the IT and corporate agenda.
Cybercriminals, these as Conti, Hive and REvil, are targeting storage and backup methods, to avoid recovery.
Some ransomwares – Locky and Crypto, for illustration – now bypass output devices completely, and specifically goal backups.
This has forced organizations to seem again at probable holes in their safety nets, by examining their storage, backup, and info recovery methods.
CISO Point of See
To get insights on new storage, backup, and info protection strategies, 8 CISOs were being interviewed. Right here are some of all those lessons.
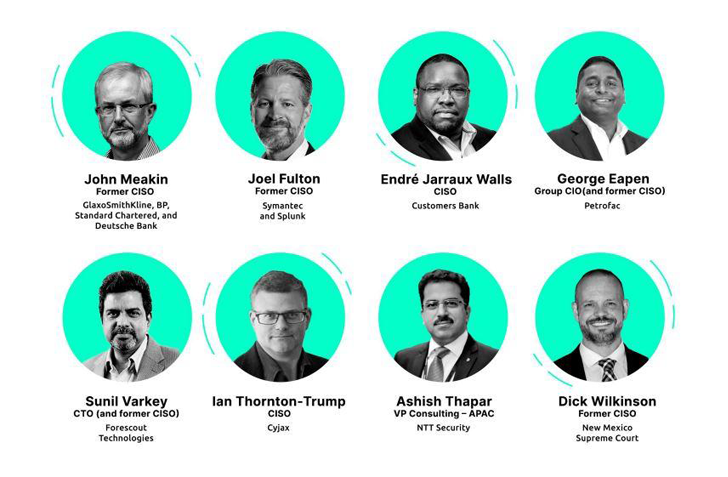 Supply: CISO Stage of Check out: The at any time-shifting role of details, and the implications for details safety & storage security (Continuity)
Supply: CISO Stage of Check out: The at any time-shifting role of details, and the implications for details safety & storage security (Continuity)
CISOs are involved about the increase of ransomware – not only of the proliferation of attacks but also of their sophistication: “The storage and backup environments are now underneath attack, as the attackers comprehend that this is the single greatest figuring out factor to clearly show if the firm will spend the ransom,” suggests George Eapen, Team CIO (and former CISO) at Petrofac,
John Meakin, former CISO at GlaxoSmithKline, BP, Regular Chartered, and Deutsche Financial institution thinks that “As significant as it may well be, facts encryption is rarely adequate to defend an organization’s main information. If attackers come across their way into a storage system (as information encryption alone is not going to protect against them from performing so), they are free to lead to extreme problems by deleting and compromising petabytes of information – whether they are encrypted or not. This also involves the snapshots and backup.”
With out a sound storage, backup, and details restoration strategy, companies have little chance of surviving a ransomware attack, even if they conclude up paying the ransom.
Shared Responsibility – CISO vs. Storage & Backup Seller
Although storage & backup sellers provide superb tools for controlling availability and overall performance of their infrastructure, they do not do the exact for the security and configuration of those same systems.
Some storage and backup sellers publish security most effective exercise guides. However, implementation and monitoring of security options and configurations is the accountability of an organization’s security division.
There are, nonetheless, a amount of cyber resiliency initiatives that are being carried out. These involve:
Recent Ransomware Resiliency Initiatives For Storage & Backup:
Air-gapped information copies
Adding an air-gap usually means separating backups from production facts. This usually means that if the generation atmosphere is breached, attackers really don’t straight away have accessibility to backups.
You can also keep storage accounts individual.
Storage snapshots & replication
Snapshots report the live point out of a procedure to a different place, whether or not that is on-premises or in the cloud. So, if ransomware hits the generation procedure, there is every likelihood it will be replicated on to the copy.
Immutable storage & vault
Immutable storage is the most basic way to shield backup details. Facts is saved in a Publish At the time Go through Lots of (WORM) point out and can’t be deleted for a pre-specified interval.
Guidelines are established in backup software program or at storage level and it means backups can’t be adjusted or encrypted.
When immutability is practical in remediating cyberthreats, it is certainly not bullet evidence.
Immutable storage can be ‘poisoned’, enabling hackers to modify the configuration of backup clientele and step by step substitute stored info with meaningless facts. In addition, when hackers get access to the storage procedure, they can quickly wipe out snapshots.
Storage security posture administration
Storage security posture administration remedies assistance you get a comprehensive check out of the security challenges in your storage & backup programs. It does this by constantly scanning these methods, to routinely detect security misconfigurations and vulnerabilities.
It also prioritizes threats in get of urgency and enterprise influence, and gives remediation steering.

4 Methods to Accomplishment
NIST Exclusive Publication 800-209 Security Rules for Storage Infrastructure offers an overview of the evolution of storage technology, recent security threats, and the challenges they pose.
It consists of a extensive established of tips for the secure deployment, configuration, and operation of storage assets. These include info and confidentiality safety employing encryption, isolation and restoration assurance.
Located this posting interesting? Adhere to us on Twitter and LinkedIn to go through far more unique information we put up.
Some sections of this short article are sourced from:
thehackernews.com

 Resurrected Crypto-mixer Launders $100m in North Korean Funds
Resurrected Crypto-mixer Launders $100m in North Korean Funds