Getty Visuals
With social engineering set to plague 2022, being familiar with cyber criminals’ methods, and the issues they make, could assist us protect in opposition to their attempts. This is the 1st entry in a 4-portion sequence, released weekly, discovering how social engineers plan their attacks – from determining targets to exploitation.
Human beings are tough-wired to trust, aid, link and impress. It really is what tends to make us so important to your organisation. These traits, however, also make humans your deadly flaw.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
Social engineering is the art of tricking persons into executing some thing that is in your interests and not in your victims’, with a see to accumulating information and facts or obtaining an action, these kinds of as allowing you into their house. It is really a criminal tactic as old as time, and a ideal fit for today’s networked workplace.
Cyber criminals have utilised social engineering proficiently as a result of the years, turning the very best personnel into unwitting accomplices in security breaches. The consequence, alert industry experts, has been a surge in active threats to critical and sensitive systems.
Know thy enemy
“There is certainly a tidal wave of it coming,” former cyber prison and We Struggle Fraud founder, Tony Sales, tells IT Pro. “Countrywide infrastructure is at risk since of social engineering. I imagine the whole nation is at risk with no even realising it.”
Figures bear out this alarming language, with Verizon finding 85% of info breaches contain attempts to prey on human weaknesses. Purplesec statements, in the meantime, 98% of attacks depend on some variety of social engineering.
It is really simple to see why cyber criminals come across social engineering so successful it can take considerably significantly less energy and ingenuity to con an person into supplying you access to organization pcs than hacking via corporate code. The very poor weaponised worker has no concept what is heading on.
If you are to stand any possibility of avoiding this risk, you have to know your enemy and recognise their tactics. “Except if you train your personnel about the human element, you are heading to turn out to be a victim,” states Income, whose 30-year felony profession integrated identity fraud and two stints in prison. “If you do educate them, while, you are going to pressure the attackers to search elsewhere, at your fewer safe competitors.” You have to check out, hence, to get inside a social engineer’s heads before they can get within yours.
The attack plan
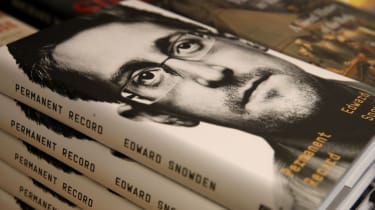
Social engineering is, by its nature, a stealthy, tough-to-place, compromising tactic that plays a function in most multi-stage attacks that demand from customers extensive-phrase infiltration and observation. Generally, the attacker will use a combination of actions to reach their aims. These can be as easy as tricking anyone into revealing their process password (not challenging, specified how several of us nonetheless use our pets’ names and soccer groups as passwords), or as refined as securing a work with a certain organisation in order to infiltrate its worldwide security networks. Edward Snowden, in a way, did both of those.
Lengthy right before an bold social engineer can get stuck into spoofing finance staff with AI deepfakes pretending to be the CFO, even so, they must make a decision how their action fits into the attack plan. They ought to also ascertain which employee to concentrate on, how to attain their have confidence in, and to what ends: To steal money? Seize information and intellectual house (IP), which can then be sold on the black market place or utilised in additional attacks? Or are they hoping to exploit a flaw and infiltrate the organisation’s network, then set off a row of domino compromises in a supply-chain attack?
Getty Pictures
Edward Snowden was at the coronary heart of a sensational whistleblowing scandal early very last decade
“Innovative attackers have a extremely obvious comprehension of how they’ll revenue from their pursuits, just like a thriving business,” suggests James Stanger, main technology evangelist at IT schooling group CompTIA. “If they want to steal passwords, for instance, they will choose just how they will monetise these passwords to increase their financial gain at the lowest attainable risk.”
Address your tracks
The character of social engineering aids threat actors stay hidden or disguised, suitable up to the remaining breach, and even right after the broader outcomes are observed. The technique’s significant reliance on study, however, dangers leaving a substantial on the web footprint, so this has to be dealt with in the attack plan.
“They’d possibly use Tor and a VPN to be as obfuscated as possible,” says Kevin Curran, senior IEEE member and professor of cyber security at Ulster University. “It requires amazing focus to be profitable, there’s a large amount of energy associated in being beneath the radar.”
To reduce the energy, the social engineer could employ accomplices with complementary skillsets. Product sales, for illustration, teamed up with hacker Solomon Gilbert. “Sol was in all probability 1 of the ideal hackers on the earth,” claims Product sales. “My prison mind functions out a plan, and Solomon attaches what he requires to it, and then you get the ‘boom’. We were 10 instances deadlier collectively than we’d ever have been individually.”
An expert social engineer, however, will exploit human flaws from the term go, and employ the service of accomplices who have no thought what they are finding into. This cuts down any risk for the prison by restricting the range of persons with understanding of the conspiracy. “You could probably stop up becoming a translator for a prison gang and not know it,” SE Labs founder Simon Edwards tells IT Pro. “If I was heading to influence you to do a thing for me, I would faux to be Apple, so you’d consider you had been doing the job for Apple to enable them edit their messaging – and you wouldn’t know any different.”
In the subsequent aspect of our collection, we reveal how a social engineer smokes out the weakest inbound links in an organisation and turns these men and women into attack vectors.
Some parts of this write-up are sourced from:
www.itpro.co.uk


 VMware Patches Important Bug Affecting ESXi, Workstation and Fusion Products
VMware Patches Important Bug Affecting ESXi, Workstation and Fusion Products