When contemplating authentication suppliers, numerous organizations consider the simplicity of configuration, ubiquity of usage, and specialized stability. Businesses simply cannot usually be judged on these metrics by itself. There is an rising want to assess firm ownership, procedures and the balance, or instability, that it delivers.
How Management Adjust Affects Steadiness
In the latest months, a salient case in point is that of Twitter. The Twitter system has been all over because 2006 and is utilised by millions around the globe. With numerous people and a seemingly sturdy authentication procedure, corporations made use of Twitter as a most important or secondary authentication services.
Inconsistent leadership and policies imply the stability of a system is issue to change, which is specially accurate with Twitter as of late. The possession transform to Elon Musk precipitated prevalent alterations to staffing and guidelines. Thanks to those modifications, a huge portion of team was permit go, but this included numerous persons liable for the specialized stability of the platform.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
This culminated in an outage of Twitter’s SMS two-factor authentication. With delayed or non-existent texts, lots of people could not log in to Twitter. This affected systems that relied on Twitter as their principal and secondary authentication company.
Not constrained to authentication issues, with the adjustments come a renewed issue more than the safety and privacy of consumer details. Twitter has been underneath an FTC consent decree from previous troubles bordering person facts, and a very good part of the workers liable for compliance has been permit go. Even if the authentication supplier stays up, it may go away an corporation in an awkward place about the point out of their stored on Twitter’s servers.
Approaches for Authentication Provider Stability
Utilizing a platform’s perfectly-recognized and strong authentication service can save companies time and dollars more than applying their individual. Slicing out third-party platforms is generally not feasible or even recommended. As an alternative, proactive scheduling is necessary if an firm wants to maintain security and security with its authentication platforms.
It can be critical to request and respond to the next issues when thinking about how your organization’s authentication assistance would tackle probable disruptions in authentication vendors.
- Does the organization’s authentication provider aid numerous identity providers?
- If a company is unavailable, is there a backup company, and how rapidly can companies be switched?
- What is the disruption to buyers? Will they be logged out of recent periods, or will it be seamless and take outcome on the upcoming login?
- If MFA is configured, what are the obtainable choices? Are there various methods to verify the user, and if one is eradicated, does that degrade authentication solutions?
If an corporation chose Twitter as a resource of two-factor authentication, it might come across that recent gatherings point out a required adjust. If so, the switch could be designed less difficult if a number of MFA platforms had been previously accessible and configured.
If an business can decide on the active authentication procedure based mostly on present requirements, then even the difficulties shown with a significant platform these types of as Twitter would be mitigated, and the organization’s consumers would see small change.
Supplying Several MFA Selections
To understand how this will work in observe, one particular can appear to Microsoft. With Azure, the moment MFA is configured, you can provide many solutions or restrict the available verification procedures. As an alternative of an SMS, you could get a phone connect with or use a hardware token. If you give all 3, you will not likely be locked out of your account if a particular support is unavailable.
Almost equivalent is Google Workspace, where you can offer one particular or a lot more authentication possibilities. If you help a lot more than a person, you will not reduce the capacity to authenticate your buyers in the party of a services failure. Both equally Microsoft and Google could be more flexible. Neither offers the entire vary of alternatives to combine with solutions like Twitter.
An illustration of a process that offers a myriad of options is Okta. By enabling Social Logins, you can let consumers to log in by using well-known services these kinds of as Fb or Twitter. But it truly is advised that you back again that social login with an MFA configuration that could consist of this kind of options as SMS, authenticator applications, or a components device these kinds of as a Yubikey.
Mitigating Authentication Instability with Specops uReset
An organization may well discover alone uncomfortable with variations to its authentication company. If so, utilizing a merchandise, these types of as Specops uReset, will take the reliance on a problematic authentication platform off the table, at minimum for password resets.
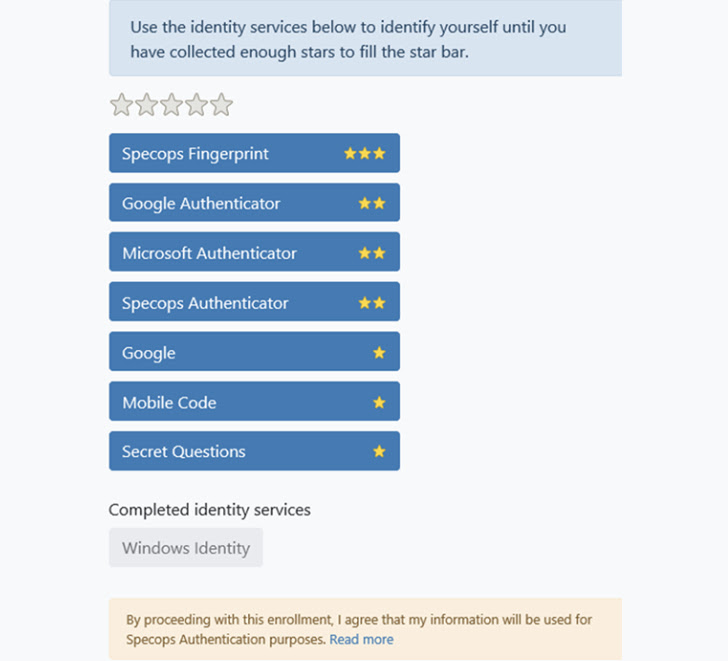
The versatility to choose from various weighted authentication providers can make a problematic service provider uncomplicated to clear away although leaving the ability for users and support desk personnel to reset a password. Improve the weighting to offset the loss of the earlier applied service provider, and your consumers can rapidly get again to get the job done!
Given that several suppliers are in use, you can have finish-buyers utilize a mix of trusted identification solutions to carry out self-support password resets devoid of worrying about losing entry to a previously critical authentication provider.
 Source
Source
Handle Platform Instability with Planning
Platform changes are difficult to forecast and react to, but your organization can be all set for any modify with foresight and preparing. Even the most mercurial leaders can be planned around by architecting flexible authentication solutions.
With items these kinds of as Specops uReset, people will not be locked out when an authentication service goes down. Applying different password reset alternatives, they can speedily get back to operate.
Identified this posting fascinating? Abide by us on Twitter and LinkedIn to examine more exceptional information we put up.
Some sections of this article are sourced from:
thehackernews.com


 CISA Warns for Flaws Affecting Industrial Control Systems from Major Manufacturers
CISA Warns for Flaws Affecting Industrial Control Systems from Major Manufacturers