A security researcher who has a very long line of get the job done demonstrating novel facts exfiltration approaches from air-gapped devices has come up with still one more procedure that will involve sending Morse code alerts by using LEDs on network interface cards (NICs).
The method, codenamed ETHERLED, arrives from Dr. Mordechai Guri, the head of R&D in the Cyber Security Study Heart in the Ben Gurion College of the Negev in Israel, who not long ago outlined GAIROSCOPE, a process for transmitting details ultrasonically to smartphone gyroscopes.


Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
“Malware mounted on the device could programmatically management the standing LED by blinking or alternating its shades, working with documented approaches or undocumented firmware instructions,” Dr. Guri reported.
“Facts can be encoded via simple encoding these types of as Morse code and modulated above these optical indicators. An attacker can intercept and decode these indicators from tens to hundreds of meters absent.”
A network interface card, also known as a network interface controller or network adapter, is a personal computer hardware element that connects a computer to a personal computer network. LEDs integrated into the network connector notify the person of regardless of whether the network is related, and when data exercise occurs.
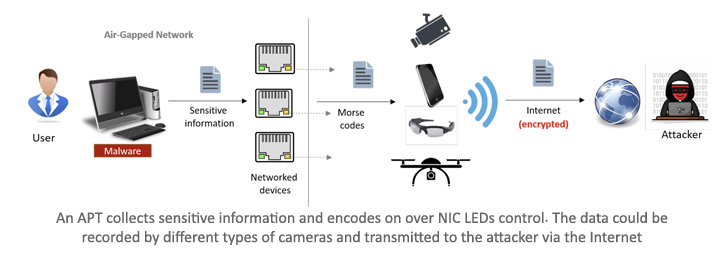
ETHERLED, like other adversarial approaches versus air-gapped units, involves the intruder to breach the focus on atmosphere and plant malicious code that will make it doable to manage the NIC LEDs.
The 2nd phase of the attack relates to data selection and exfiltration, all through which sensitive information and facts is encoded and sent over an optical covert channel by applying the network card’s position LEDs.
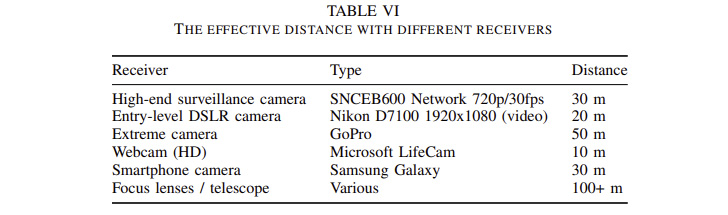
In the final stage, the optical indicators are obtained via a hidden camera that is positioned in a site with a direct line of sight with the compromised transmitting personal computer. Alternatively, the camera could also be a surveillance digicam that is susceptible to distant exploitation or a smartphone that will involve a rogue insider.

The attack can be employed to leak several styles of info, like passwords, RSA encryption keys, keystrokes, and textual articles, to cameras situated any place in between 10m and 50m, a distance that can be further more extended to a handful of hundred meters by applying a telescope and unique emphasis lenses.
What’s more, the ETHERLED method is developed to perform with peripherals or components that are delivered with Ethernet cards, this sort of as printers, network cameras, network-attached storage (NAS) units, embedded devices, and other IoT devices.
Countermeasures consist of limiting cameras and online video recorders in sensitive zones, covering the status LEDs with black tape to block the optical emanation physically, reprogramming the program to defeat the encoding scheme, and jamming the environment to increase random noise to the modulated indicators.
Located this article fascinating? Comply with THN on Fb, Twitter and LinkedIn to study much more unique articles we put up.
Some parts of this article are sourced from:
thehackernews.com

 IoT Vulnerability Disclosures Up 57% in Six Months, Claroty Reveals
IoT Vulnerability Disclosures Up 57% in Six Months, Claroty Reveals