Cybersecurity scientists have drop mild on the internal workings of the ransomware operation led by Mikhail Pavlovich Matveev, a Russian national who was indicted by the U.S. authorities previously this 12 months for his alleged position in launching countless numbers of attacks throughout the planet.
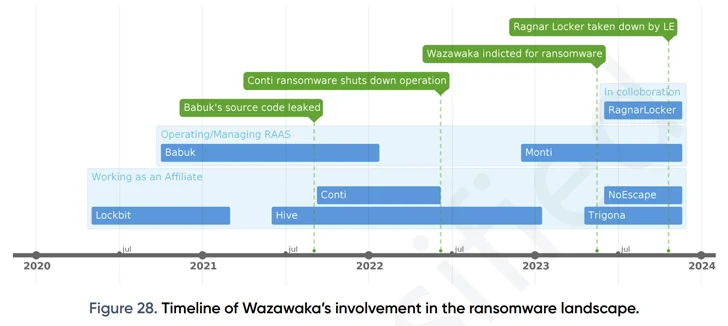
Matveev, who resides in Saint Petersburg and is acknowledged by the aliases Wazawaka, m1x, Boriselcin, Uhodiransomwar, Orange, and waza, is alleged to have performed a very important element in the development and deployment of LockBit, Babuk, and Hive ransomware variants because at the very least June 2020.
“Wazawaka and his crew users prominently exhibit an insatiable greed for ransom payments, demonstrating a substantial disregard for moral values in their cyber functions,” Swiss cybersecurity agency PRODAFT said in a detailed examination shared with The Hacker News.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
“Utilizing tactics that entail intimidation by means of threats to leak delicate data files, participating in dishonest techniques, and persisting in retaining documents even right after the target complies with the ransom payment, they exemplify the ethical void prevalent in the tactics of common ransomware teams.”
Future WEBINAR Conquer AI-Run Threats with Zero Have faith in – Webinar for Security Industry experts
Conventional security steps won’t cut it in present-day world. It can be time for Zero Rely on Security. Secure your info like under no circumstances right before.
Join Now
PRODAFT’s results are the outcome of details compiled among April and December 2023 by intercepting thousands of interaction logs in between various menace actors affiliated with numerous ransomware variants.
Matawveev is said to guide a team of 6 penetration testers – 777, bobr.kurwa, krbtgt, shokoladniy_zayac, WhyNot, and dushnila – to execute the attacks. The team has a flat hierarchy, fostering much better collaboration between the customers.
“Each individual unique contributes resources and abilities as required, showcasing a exceptional level of adaptability in adapting to new eventualities and conditions,” PRODAFT stated.
Matveev, moreover operating as an affiliate for Conti, LockBit, Hive, Monti, Trigona, and NoEscape, also had a management-degree job with the Babuk ransomware group up right until early 2022, when sharing what is becoming explained as a “advanced marriage” with one more actor named Dudka, who is likely the developer behind Babuk and Monti.

Attacks mounted by Matveev and his workforce involve the use of Zoominfo and expert services like Censys, Shodan, and FOFA to get facts about the victims, relying on recognised security flaws and original entry brokers for acquiring a foothold, in addition to employing a combine of custom and off-the-shelf tools to brute-power VPN accounts, escalate privileges, and streamline their campaigns.
“Adhering to the attainment of original access, Wazawaka and his team principally hire PowerShell instructions to execute their chosen Remote Monitoring and Administration (RMM) instrument,” the company stated. “Distinctively, MeshCentral stands out as the team’s one of a kind toolkit, frequently used as their chosen open-source program for several operations.”

PRODAFT’s evaluation even further uncovered connections in between Matveev and Evgeniy Mikhailovich Bogachev, a Russian national linked to the development of the GameOver Zeus botnet, which was dismantled in 2014, and Evil Corp.
It truly is truly worth noting that the Babuk ransomware functions rebranded as PayloadBIN in 2021, with the latter tied to Evil Corp in an obvious effort and hard work to get about sanctions imposed from it by the U.S. in December 2019.
“This technological affiliation, coupled with the regarded connection between Wazawaka and the infamous cybercriminal Bogachev, suggests deeper connections amongst Wazawaka, Bogachev, and the operations of Evil Corp,” PRODAFT stated.
Discovered this article exciting? Follow us on Twitter and LinkedIn to read additional exceptional material we post.
Some elements of this posting are sourced from:
thehackernews.com


 Hackers Abusing GitHub to Evade Detection and Control Compromised Hosts
Hackers Abusing GitHub to Evade Detection and Control Compromised Hosts