An examination of new samples of BlackMatter ransomware for Windows and Linux has revealed the extent to which the operators have continuously extra new features and encryption abilities in successive iterations more than a a few-thirty day period period.
No less than 10 Windows and two Linux variations of the ransomware have been noticed in the wild to date, Group-IB danger researcher Andrei Zhdanov reported in a report shared with The Hacker News, pointing out the improvements in the implementation of the ChaCha20 encryption algorithm used to encrypt the contents of the data files.
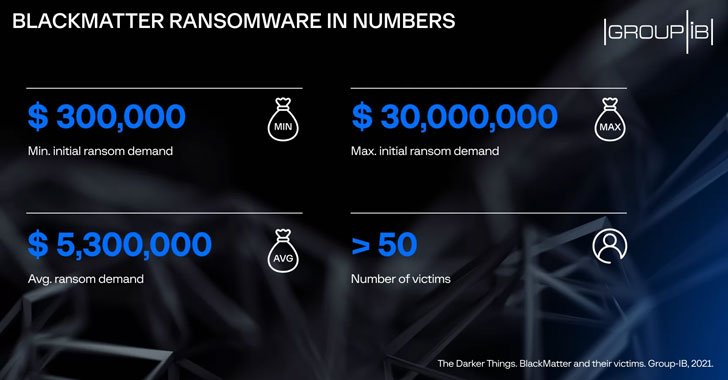
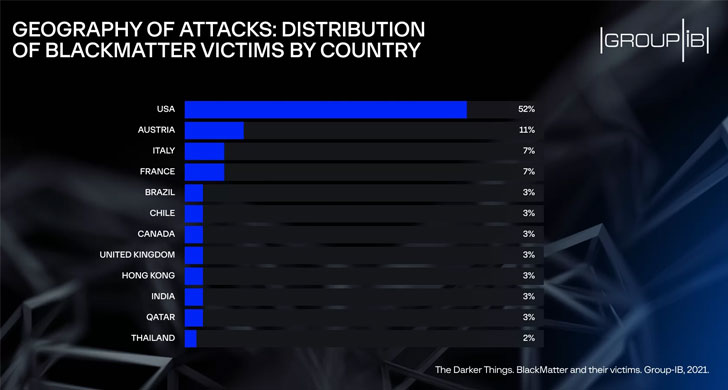
BlackMatter emerged in July 2021 boasting of incorporating the “finest capabilities of DarkSide, REvil, and LockBit” and is considered the successor to DarkSide, which has given that shut down together with REvil in the wake of law enforcement scrutiny. Functioning as a ransomware-as-a-provider (RaaS) product, the BlackMatter is thought to have hit extra than 50 corporations in the U.S., Austria, Italy, France, Brazil, among the some others.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

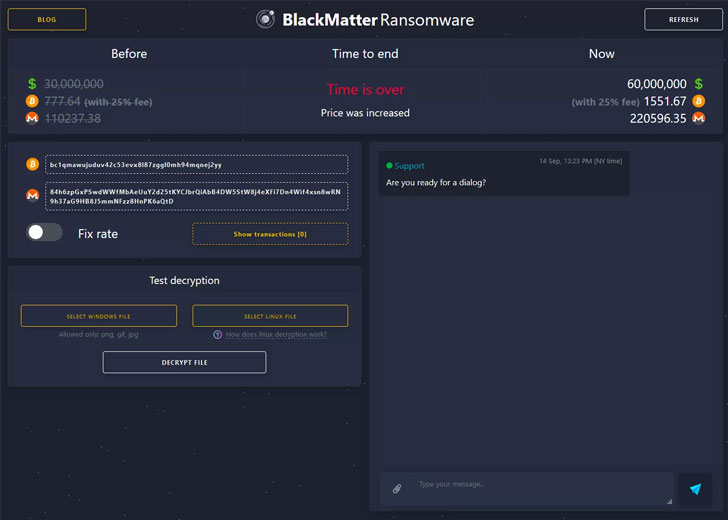
What is far more, the risk actor makes a unique Tor chat room for interaction for each victim, a backlink to which is connected to the textual content file made up of the ransom need. BlackMatter is also known to double the ransom amount of money when the ultimatum expires, prior to going to publish the stolen documents in the occasion the victim refuses to pay out up.
In accordance to security researchers from Microsoft’s counter-ransomware unit, DarkSide and its BlackMatter rebrand is the handiwork of a cybercrime team tracked as FIN7, which was recently unmasked functioning a front corporation named Bastion Safe to entice tech gurus with the goal of launching ransomware attacks.
“When other parameters are established or any parameters are absent, the process is entirely encrypted according to the configuration options,” Zhdanov mentioned. “On finishing the encryption, the ransomware generates a BMP impression alerting that documents have been encrypted, which it then sets as the desktop wallpaper. Beginning from edition 1.4, the ransomware can also print the text of the demand for ransom on the victim’s default printer.”

The Linux variants, on the other hand, are developed to concentrate on VMware ESXi servers, that includes the skill to terminate virtual equipment and kill distinct procedures, such as the firewall, prior to commencing information encryption.
The results arrive as VX-Underground, a portal that hosts malware source code, samples and papers, uncovered that the team is pulling the plug on its operations “pursuing tension from nearby authorities.” The put up shared on the RaaS web-site also observed that a “aspect of the group is no longer offered, just after the latest information.”
It truly is not right away crystal clear what the “most recent information” could be referring to, but it implies a potent url to the coordinated global regulation enforcement procedure late very last thirty day period that noticed 12 people today arrested for orchestrating ransomware attacks towards 1,800 victims across 71 international locations since 2019.
In an advisory issued on Oct 18, 2021, the Cybersecurity and Infrastructure Security Company (CISA), the Federal Bureau of Investigation (FBI), and the Nationwide Security Company (NSA) warned that the BlackMatter ransomware group has qualified “multiple” companies considered critical infrastructure, like two entities in the U.S. food items and agriculture sector.
Identified this report fascinating? Observe THN on Fb, Twitter and LinkedIn to browse far more unique material we put up.
Some elements of this posting are sourced from:
thehackernews.com

 Product Overview – Cynet Centralized Log Management
Product Overview – Cynet Centralized Log Management