For most companies now, the logs created by their security tools and environments deliver a blended bag. On the one hand, they can be a trove of beneficial facts on security breaches, vulnerabilities, attack styles, and typical security insights.
On the other, businesses really don’t have the appropriate means to manage the massive scale of logs and info manufactured to derive any benefit from it.
Log management can rapidly develop into a sore stage, and both be forgotten or improperly managed if performed manually.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
In turn, this cuts down facts transparency and leaves corporations more exposed to vulnerabilities that could have been detected. A new centralized log administration module (CLM) released by XDR service provider Cynet (study more in this article) could assist organizations lighten that load and greatly enhance organizations’ visibility into their worthwhile log knowledge.
As a substitute of manually managing the collection, storage, and parsing of knowledge, corporations can use CLM to enhance their log evaluation, superior fully grasp their security environment, and lighten the load on lean security groups that will have to handle this system.
Introducing Cynet CLM
Cynet’s new Centralized Log Administration module offers businesses an efficient way to offer with the significant volume of security logs most businesses – no matter of size – produce. The very first step to executing this is to automate the course of action.
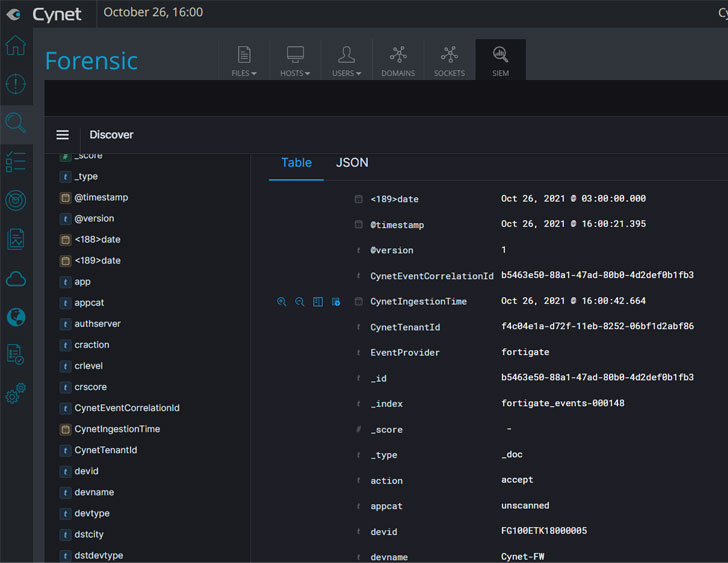
Cynet CLM routinely collects the maximum precedence log facts to uncover threats rapidly and properly across an organization’s setting. Celebration logs and facts are gathered from network equipment and apps, SaaS programs, and any hosts related to the Cynet system. Logs are saved in a data lake which can be accessed specifically by the Cynet console.
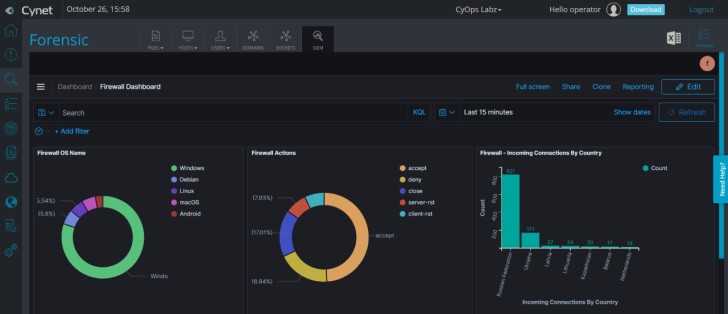
Visual log examination
A person prevalent issue with the superior quantity of logs is arranging them into a format that is easily digestible and comprehensible. Cynet delivers a visual analysis device that lets security teams produce charts and dashboards that enable them acquire and leverage insights from their log repository. Furthermore, it lets groups swiftly pinpoint and take care of issues.
Centralized management
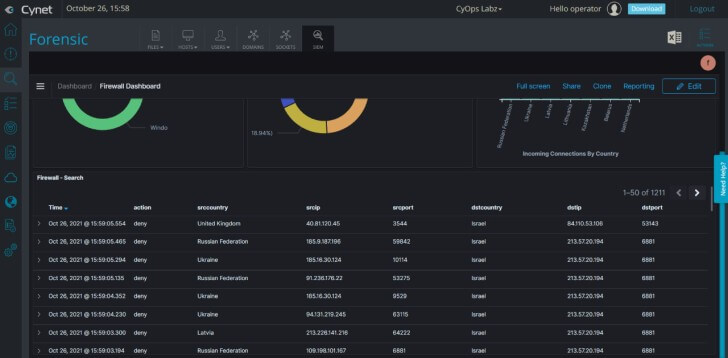
As the title implies, Cynet’s CLM provides corporations an effortless way to look at, kind, question, filter and correlate facts from hundreds of sources in a single area. As an alternative of getting to hunt threats and look for vulnerabilities throughout a network of resources, security teams can simply just emphasis on a solitary pane of glass that lets them organize their data and leverage impressive question applications to find particularly the info they will need.
A lot easier info deep-dives
Probably the greatest gain of centralizing log management is the depth of examination a single knowledge place can present. Cynet CLM mechanically connects all knowledge details linked to log activities into solitary threads.
This will make it less complicated to recognize an party throughout an total network in a one check out. Security groups do not have to manually scour as a result of hundreds of logs and resources to monitor a solitary celebration. As a substitute, a one click on allows groups quickly realize an occasion and uncover techniques to take care of it and stop it in the long run.
Companies can now add Cynet CLM to their present Cynet 360 licenses and include a new log evaluation resource to their arsenal.
Cynet is also launching a webinar to introduce its CLM module. You can register listed here.
You can find out extra about Cynet CLM here.
Found this post fascinating? Stick to THN on Fb, Twitter and LinkedIn to go through a lot more unique written content we put up.
Some elements of this report are sourced from:
thehackernews.com


 Mitre reveals 10 worst hardware security weaknesses in 2021
Mitre reveals 10 worst hardware security weaknesses in 2021