The Russia-connected threat actor identified as Gamaredon has been noticed conducting data exfiltration things to do in just an hour of the preliminary compromise.
“As a vector of key compromise, for the most portion, emails and messages in messengers (Telegram, WhatsApp, Signal) are employed, in most conditions, working with earlier compromised accounts,” the Laptop or computer Crisis Response Staff of Ukraine (CERT-UA) claimed in an analysis of the team revealed last 7 days.
Gamaredon, also known as Aqua Blizzard, Armageddon, Shuckworm, or UAC-0010, is a condition-sponsored actor with ties to the SBU Primary Business in the Autonomous Republic of Crimea, which was annexed by Russia in 2014. The team is estimated to have contaminated thousands of federal government personal computers.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
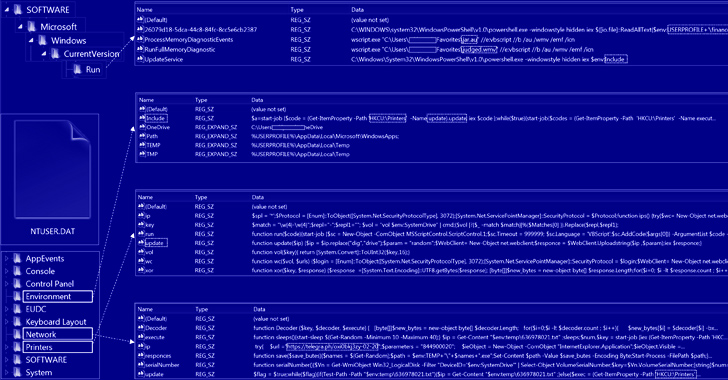
It is also one particular of the quite a few Russian hacking crews that have preserved an lively presence considering the fact that the start out of the Russo-Ukrainian war in February 2022, leveraging phishing strategies to supply PowerShell backdoors this sort of as GammaSteel to perform reconnaissance and execute further instructions.
The messages normally arrive bearing an archive containing an HTM or HTA file that, when opened, activates the attack sequence.
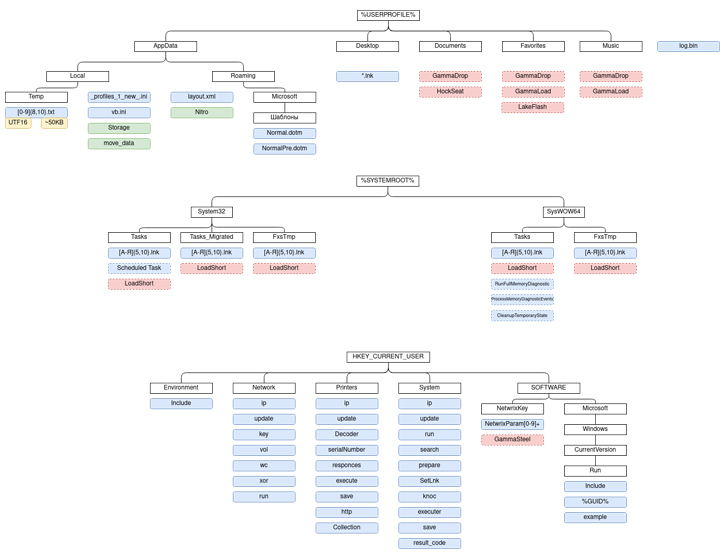
In accordance to CERT-UA, GammaSteel is made use of to exfiltrate documents matching a specific set of extensions – .doc, .docx, .xls, .xlsx, .rtf, .odt, .txt, .jpg, .jpeg, .pdf, .ps1, .rar, .zip, .7z, and .mdb – in a time time period of 30 to 50 minutes.
The team has also been noticed continuously evolving its strategies, generating use of USB infection approaches for propagation. A host running in a compromised condition for a 7 days could have anywhere between 80 to 120 destructive information, the company famous.
Upcoming WEBINARShield Against Insider Threats: Master SaaS Security Posture Management
Worried about insider threats? We have received you lined! Join this webinar to examine sensible approaches and the secrets and techniques of proactive security with SaaS Security Posture Management.
Be part of These days
Also substantial is the menace actor’s use of AnyDesk computer software for interactive distant access, PowerShell scripts for session hijacking to bypass two-factor authentication (2FA), and Telegram and Telegraph for fetching the command-and-control (C2) server info.
“Attackers just take individual measures to ensure fault tolerance of their network infrastructure and stay clear of detection at the network stage,” CERT-UA mentioned. “For the duration of the day, the IP addresses of intermediate handle nodes can transform from 3 to 6 or additional periods, which, between other factors, suggests the suitable automation of the course of action.”
Identified this posting fascinating? Follow us on Twitter and LinkedIn to go through more special written content we write-up.
Some components of this short article are sourced from:
thehackernews.com

 WormGPT: New AI Tool Allows Cybercriminals to Launch Sophisticated Cyber Attacks
WormGPT: New AI Tool Allows Cybercriminals to Launch Sophisticated Cyber Attacks