A Chinese highly developed persistent danger (APT) known as Gallium has been observed using a earlier undocumented remote obtain trojan in its espionage attacks focusing on providers working in Southeast Asia, Europe, and Africa.
Called PingPull, the “complicated-to-detect” backdoor is noteworthy for its use of the Internet Handle Concept Protocol (ICMP) for command-and-handle (C2) communications, according to new investigation revealed by Palo Alto Networks Device 42 today.


Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
Gallium is known for its attacks primarily aimed at telecom businesses dating as significantly back again as 2012. Also tracked below the name Comfortable Cell by Cybereason, the state-sponsored actor has been related to a broader established of attacks focusing on five main telecom organizations located in Southeast Asian nations around the world considering the fact that 2017.
Around the earlier year, however, the team is said to have expanded its victimology footprint to contain fiscal establishments and governing administration entities situated in Afghanistan, Australia, Belgium, Cambodia, Malaysia, Mozambique, the Philippines, Russia, and Vietnam.
PingPull, a Visible C++-dependent malware, provides a menace actor the potential to accessibility a reverse shell and run arbitrary commands on a compromised host. This encompasses carrying out file operations, enumerating storage volumes, and timestomping files.
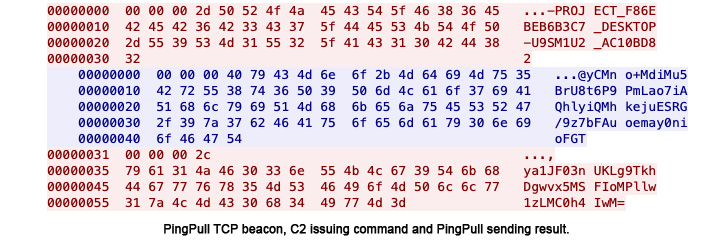
“PingPull samples that use ICMP for C2 communications issue ICMP Echo Request (ping) packets to the C2 server,” the researchers detailed. “The C2 server will reply to these Echo requests with an Echo Reply packet to issue instructions to the method.”

Also recognized are PingPull variants that count on HTTPS and TCP to connect with its C2 server as an alternative of ICMP and more than 170 IP addresses involved with the group due to the fact late 2020.
It can be not straight away distinct how the targeted networks are breached, despite the fact that the danger actor is acknowledged to exploit internet-uncovered programs to obtain an first foothold and deploy a modified edition of the China Chopper web shell to set up persistence.
“Gallium stays an active risk to telecommunications, finance and govt companies throughout Southeast Asia, Europe and Africa,” the scientists observed.
“When the use of ICMP tunneling is not a new technique, PingPull works by using ICMP to make it extra challenging to detect its C2 communications, as couple companies carry out inspection of ICMP site visitors on their networks.”
Identified this article appealing? Abide by THN on Fb, Twitter and LinkedIn to browse a lot more special articles we publish.
Some sections of this posting are sourced from:
thehackernews.com

 Researchers Disclose Rooting Backdoor in Mitel IP Phones for Businesses
Researchers Disclose Rooting Backdoor in Mitel IP Phones for Businesses