A Chinese country-condition team has been observed concentrating on Overseas Affairs ministries and embassies in Europe working with HTML smuggling tactics to provide the PlugX remote obtain trojan on compromised systems.
Cybersecurity agency Check out Point claimed the action, dubbed SmugX, has been ongoing given that at least December 2022.
“The campaign employs new supply strategies to deploy (most notably – HTML Smuggling) a new variant of PlugX, an implant generally related with a large wide range of Chinese danger actors,” Check Place reported.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
“Even though the payload by itself remains identical to the just one identified in older PlugX variants, its supply techniques end result in minimal detection costs, which until finally lately helped the marketing campaign fly beneath the radar.”
The exact identification of the threat actor behind the operation is a tiny hazy, whilst existing clues point in the direction of Mustang Panda, which also shares overlaps with clusters tracked as Earth Preta, RedDelta, and Test Point’s personal designation Camaro Dragon.
Even so, the organization stated there is “inadequate proof” at this stage to conclusively attribute it to the adversarial collective.
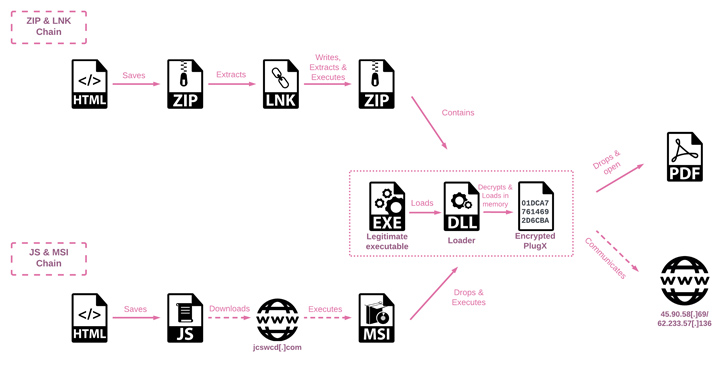
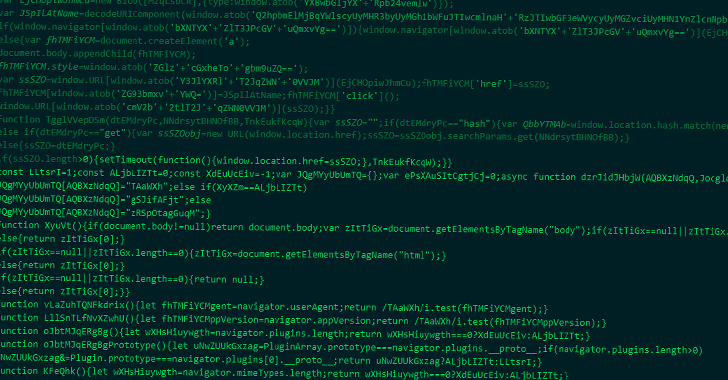
The latest attack sequence is important for the use of HTML Smuggling – a stealthy system in which respectable HTML5 and JavaScript attributes are abused to assemble and start the malware – in the decoy files attached to spear-phishing e-mails.
“HTML smuggling employs HTML5 attributes that can get the job done offline by storing a binary in an immutable blob of facts inside JavaScript code,” Trustwave observed previously this February. “The information blob, or the embedded payload, will get decoded into a file object when opened via a web browser.”
An investigation of the files, which had been uploaded to the VirusTotal malware database, reveals that they are made to concentrate on diplomats and authorities entities in Czechia, Hungary, Slovakia, the U.K., Ukraine, and also likely France and Sweden.

In one instance, the threat actor is stated to have utilized an Uyghur-themed lure (“China Attempts to Block Popular Uyghur Speaker at UN.docx”) that, when opened, beacons to an external server by signifies of an embedded, invisible monitoring pixel to exfiltrate reconnaissance data.
The multi-stage an infection process makes use of DLL side-loading methods to decrypt and launch the ultimate payload, PlugX.
Also referred to as Korplug, the malware dates all the way again to 2008 and is a modular trojan able of accommodating “numerous plugins with distinctive functionalities” that allows the operators to carry out file theft, screen captures, keystroke logging, and command execution.
“Through the course of our investigating the samples, the risk actor dispatched a batch script, despatched from the C&C server, intended to erase any trace of their activities,” Verify Issue claimed.
“This script, named del_RoboTask Update.bat, eradicates the respectable executable, the PlugX loader DLL, and the registry crucial implemented for persistence, and eventually deletes itself. It is very likely this is the consequence of the risk actors getting knowledgeable they were less than scrutiny.”
Found this write-up exciting? Adhere to us on Twitter and LinkedIn to go through extra distinctive information we post.
Some sections of this write-up are sourced from:
thehackernews.com

 Improve Your Security WordPress Spam Protection With CleanTalk Anti-Spam
Improve Your Security WordPress Spam Protection With CleanTalk Anti-Spam