DevOps platform CircleCI on Wednesday urged its clients to rotate all their insider secrets next an unspecified security incident.
The corporation stated an investigation is presently ongoing, but emphasised that “there are no unauthorized actors lively in our programs.” More aspects are envisioned to be shared in the coming times.
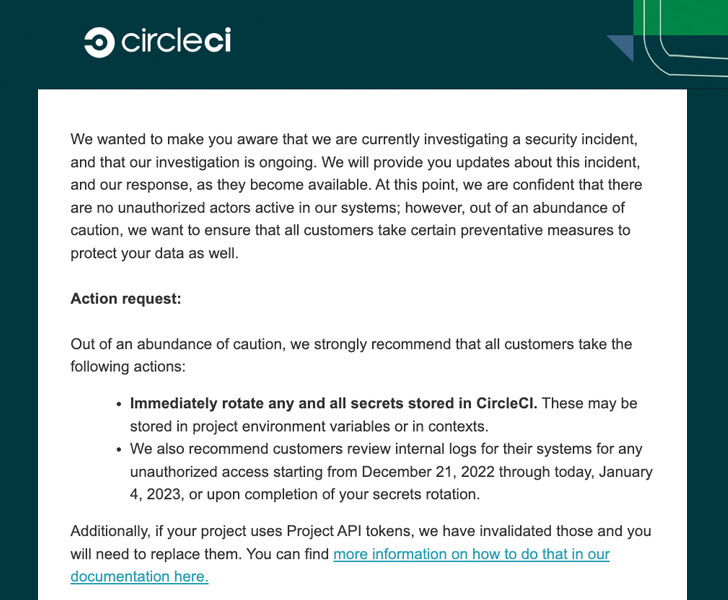
“Quickly rotate any and all strategies stored in CircleCI,” CircleCI’s main technology officer, Rob Zuber, stated in a terse advisory. “These may possibly be saved in challenge surroundings variables or in contexts.”

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
CircleCI is also recommending users to assessment inner logs for indicators of any unauthorized entry starting off from December 21, 2022, to January 4, 2023, or till when the insider secrets are rotated.
The software growth service did not disclose any even further details about the breach, but mentioned it has also invalidated all Challenge API tokens and that they need to have to be changed.
The disclosure will come weeks immediately after the firm announced that it experienced launched dependability updates to the service on December 21, 2022, to solve underlying “systemic issues.”
It can be also the most recent breach to hit CircleCI in latest a long time. The corporation, in September 2019, exposed “unconventional exercise” linked to a third-party analytics vendor that resulted in unauthorized access to usernames and email addresses affiliated with GitHub and Bitbucket.
Then last 12 months, it alerted buyers that faux CircleCI email notifications had been staying applied to steal GitHub qualifications and two-factor authentication (2FA) codes.
Slack’s GitHub Code Repositories Stolen
It is really just not CircleCI, as Slack disclosed on December 31, 2022, that it turned knowledgeable of a security issue that entailed unauthorized access to a subset of its source code repositories on GitHub.
The issue, which arrived to light on December 29, 2022, resulted in the theft of a limited selection of Slack employee tokens that had been then used to obtain its GitHub repository, finally allowing the adversary to down load the source code.
Slack, however, explained no consumer action is required and that the breach was speedily contained. The qualifications have because been invalidated.
“No downloaded repositories contained client knowledge, implies to obtain client data, or Slack’s main codebase,” the Salesforce-owned corporation said. “The danger actor did not accessibility other regions of Slack’s ecosystem, which includes the production ecosystem, and they did not accessibility other Slack sources or purchaser info.”
The instantaneous messaging assistance did not share extra information on how the worker tokens ended up stolen, but stressed the “unauthorized obtain did not consequence from a vulnerability inherent to Slack.”
Located this post attention-grabbing? Stick to us on Twitter and LinkedIn to go through much more exclusive content we post.
Some components of this report are sourced from:
thehackernews.com


 The Evolving Tactics of Vidar Stealer: From Phishing Emails to Social Media
The Evolving Tactics of Vidar Stealer: From Phishing Emails to Social Media