The U.S. Cybersecurity and Infrastructure Security Company (CISA) issued an advisory on Thursday warning that the freshly disclosed critical security flaw in Citrix NetScaler Software Delivery Controller (ADC) and Gateway gadgets is staying abused to drop web shells on vulnerable techniques.
“In June 2023, danger actors exploited this vulnerability as a zero-working day to drop a web shell on a critical infrastructure organization’s non-production environment NetScaler ADC appliance,” the company claimed.
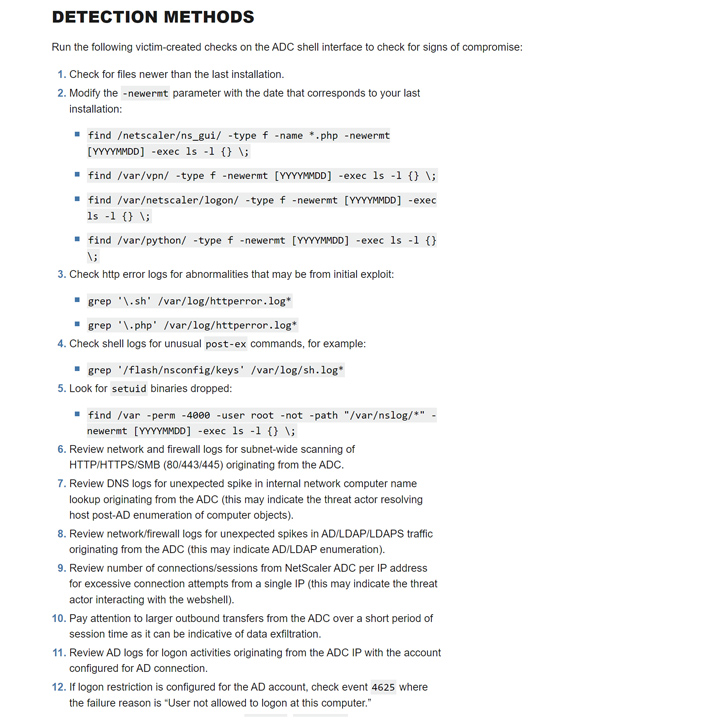
“The web shell enabled the actors to perform discovery on the victim’s lively listing (Advertisement) and obtain and exfiltrate Advert facts. The actors tried to shift laterally to a domain controller but network segmentation controls for the equipment blocked movement.”

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
The shortcoming in question is CVE-2023-3519 (CVSS score: 9.8), a code injection bug that could end result in unauthenticated distant code execution. Citrix, before this 7 days, launched patches for the issue and warned of active in-the-wild exploitation.
Prosperous exploitation calls for the appliance to be configured as a Gateway (VPN virtual server, ICA Proxy, CVPN, RDP Proxy) or authentication, authorization, and auditing (AAA) virtual server.
CISA did not disclose the name of the corporation that was impacted by the incident. The threat actor or the region allegedly at the rear of it is presently unknown.
In the incident analyzed by CISA, the web shell is claimed to have enabled the selection of NetScaler configuration files, NetScaler decryption keys, and Advertisement data, after which the knowledge was transmitted as a PNG image file (“medialogininit.png”).
Forthcoming WEBINARShield Towards Insider Threats: Grasp SaaS Security Posture Management
Concerned about insider threats? We have received you lined! Be a part of this webinar to investigate realistic methods and the secrets of proactive security with SaaS Security Posture Administration.
Sign up for Currently
The adversary’s subsequent attempts to laterally transfer across the network as very well as operate commands to recognize available targets and confirm outbound network connectivity have been thwarted owing to robust network segmentation procedures, the agency famous, incorporating the actors also tried to delete their artifacts to deal with up the tracks.
Vulnerabilities in gateway solutions these as NetScaler ADC and NetScaler Gateway have become well-known targets for risk actors searching to attain privileged access to specific networks. This helps make it imperative that customers shift speedily to use the hottest fixes to safe versus likely threats.
Identified this report exciting? Follow us on Twitter and LinkedIn to go through a lot more distinctive content we post.
Some areas of this short article are sourced from:
thehackernews.com


 Mallox Ransomware Exploits Weak MS-SQL Servers to Breach Networks
Mallox Ransomware Exploits Weak MS-SQL Servers to Breach Networks