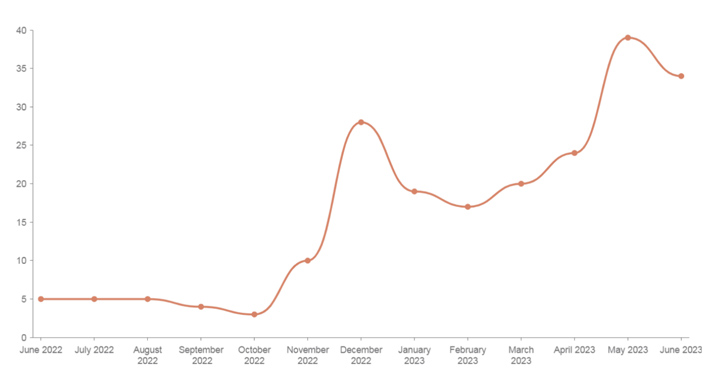
Mallox ransomware activities in 2023 have witnessed a 174% raise when as opposed to the past yr, new findings from Palo Alto Networks Unit 42 expose.
“Mallox ransomware, like numerous other ransomware threat actors, follows the double extortion trend: stealing info before encrypting an organization’s files, and then threatening to publish the stolen knowledge on a leak internet site as leverage to encourage victims to pay out the ransom fee,” security researchers Lior Rochberger and Shimi Cohen explained in a new report shared with The Hacker Information.
Mallox is joined to a risk actor that is also linked to other ransomware strains, such as TargetCompany, Tohnichi, Fargo, and, most lately, Xollam. It to start with burst on to the scene in June 2021.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
Some of the notable sectors qualified by Mallox are manufacturing, skilled and legal providers, and wholesale and retail.
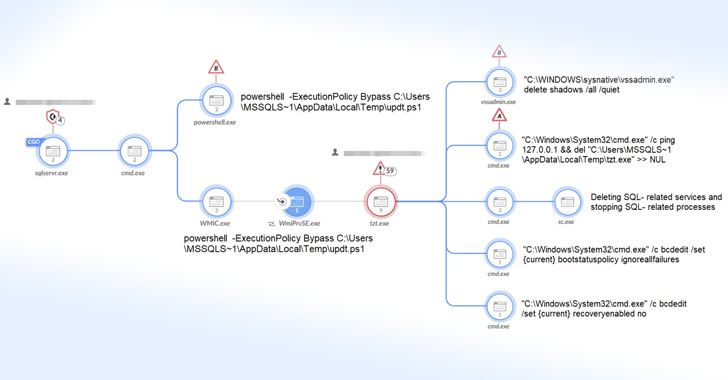
A noteworthy element of the group is its sample of exploiting inadequately secured MS-SQL servers by using dictionary attacks as a penetration vector to compromise victims’ networks. Xollam is a deviation from the norm in that it has been observed making use of destructive OneNote file attachments for initial accessibility, as detailed by Development Micro last thirty day period.
On gaining a successful foothold on the contaminated host, a PowerShell command is executed to retrieve the ransomware payload from a remote server.
The binary, for its section, attempts to stop and get rid of SQL-similar solutions, delete volume shadow copies, distinct technique party logs, terminate security-linked processes, and bypass Raccine, an open-resource software made to counter ransomware attacks, prior to commencing its encryption method, after which a ransom be aware is dropped in each listing.
Upcoming WEBINARShield Towards Insider Threats: Learn SaaS Security Posture Administration
Nervous about insider threats? We’ve received you coated! Be part of this webinar to investigate realistic tactics and the secrets of proactive security with SaaS Security Posture Management.
Be a part of Today
TargetCompany stays a modest, closed group, but it has also been noticed recruiting affiliates for the Mallox ransomware-as-a-support (RaaS) affiliate method on the RAMP cybercrime forum.
The development arrives as ransomware continues to be a worthwhile monetary scheme, netting cybercriminals no less than $449.1 million in the first 50 % of 2023 by itself, for each Chainalysis.
“The Mallox ransomware team has been additional active in the previous couple of months, and their new recruiting efforts could permit them to attack a lot more organizations if the recruitment travel is prosperous,” the scientists mentioned.
Observed this article intriguing? Abide by us on Twitter and LinkedIn to read far more exclusive written content we publish.
Some areas of this report are sourced from:
thehackernews.com

 Apache OpenMeetings Web Conferencing Tool Exposed to Critical Vulnerabilities
Apache OpenMeetings Web Conferencing Tool Exposed to Critical Vulnerabilities