CISOs, security leaders, and SOC teams generally wrestle with constrained visibility into all connections created to their company-owned belongings and networks. They are hindered by a lack of open-source intelligence and impressive technology expected for proactive, constant, and efficient discovery and safety of their programs, information, and belongings.
As superior threat actors consistently lookup for very easily exploitable vulnerabilities all around the clock, CISOs are in pursuit of improved methods to decrease threat exposures and safeguard their belongings, people, and facts from relentless cyber-attacks and the critical consequences of breaches.
In reaction to this will need, an rising answer addressing the most critical priorities at the first stage of the attack chain has supplied security leaders with a new device to control their most pressing risk exposures at their origin. Main analyst agency Gartner Exploration describes the answer: “By 2026, companies prioritizing their security investments dependent on a ongoing publicity administration plan will be 3x much less possible to endure from a breach.” (Gartner, 2022).

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
But what exactly does this involve?
IT and security teams consistently deal with menace exposures, and they should proactively tackle critical security gaps in their exposed belongings. By employing a Steady Risk Exposure Administration (CTEM) system, security teams can thwart their adversaries’ aims by minimizing critical dangers linked with uncovered assets. This comprehensive strategy brings together prevention and remediation techniques to both a) solely avert a breach or b) significantly minimize the affect if a breach does manifest.
A lot quicker Adversaries, Inadequate Security, and Preventable Incidents
In 2023, even with substantial investments in security infrastructure and experienced personnel, current methods are having difficulties to effectively lower dangers, regulate threat exposures, and avoid security breaches.
Present preventive cyber risk management tactics, although successful, are time-consuming, source-intense, and susceptible to human errors. Duties these kinds of as steady vulnerability detection, identification, and patch management desire significant time and know-how to be executed correctly. Delays or mishandling of these important routines can guide to a greater likelihood of financially harming security breaches.
Concurrently, cybercriminals can very easily receive initial access factors to substantial-price targets via the dark web, many thanks to ransomware-as-a-assistance and preliminary obtain brokers. Moreover, they can quickly get compromised user qualifications on the web, which are easily available for use in qualified methods, procedures, and processes (TTPs).
Compounding the hazards, the cybersecurity competencies gap and financial things have still left several SecOps and DevOps groups understaffed, less than-resourced, and confused by alerts.
These mixed elements have resulted in confined visibility for the SOC, offering an undue benefit to danger actors. This trend need to be countered and reversed.
The Developing Attack Floor and Growing Danger Exposures
In 2022, exterior attackers have been liable for 75% of described security breaches (IBM, 2022). These attacks are swift, intricate, and pose a important obstacle for up to date SOCs. To counter these threats, businesses ought to adopt a multi-layered defense method, as their networks, methods, and buyers are below continuous assault from exterior threat actors with malicious intentions.
Weaknesses, security gaps, and inadequate controls add to an at any time-evolving attack surface area exactly where cybercriminals can exploit easily available risk exposures. Usually, these issues had been addressed by vulnerability administration functions. Even so, as cybercriminals consistently scan for vulnerable attack surfaces, searching for weak controls, unpatched assets, and vulnerable programs, their TTPs have turn into remarkably specific, amazingly rapidly, and really productive.
Security teams call for improved abilities that provide precision, velocity, and versatility to stay ahead of their adversaries.
Recognizing this, it is essential to prioritize the identification and remediation of critical security danger exposures, as most can be prevented. By swiftly detecting and addressing these exposures, CISOs can effectively shrink their over-all attack surface area and halt its relentless growth. Consequently, companies should really put into practice a Continual Risk Exposure Administration (CTEM) system that operates 24/7.
Developing a Proactive CTEM system
The two big enterprises and modest-to-medium-sized companies (SMBs) should contemplate adopting a CTEM program to streamline conventional vulnerability administration processes and lessen their attack surface area. By proactively tackling vulnerabilities and using economical risk management methods, companies can bolster their security stance and lessen the potential penalties of security breaches. CTEM provides a holistic solution that goes further than mere vulnerability administration, supplying intelligence, context, and facts to give this means and validation to discoveries.
Gartner Analysis defines a CTEM software as a cohesive, dynamic strategy for prioritizing the remediation and mitigation of the most urgent cyber dangers whilst repeatedly maximizing an organization’s security posture: “CTEM encompasses a selection of processes and abilities that empower enterprises to consistently and regularly assess the accessibility, exposure, and exploitability of an enterprise’s electronic and bodily assets” (Gartner, 2022).
The CTEM Target on DevSecOps
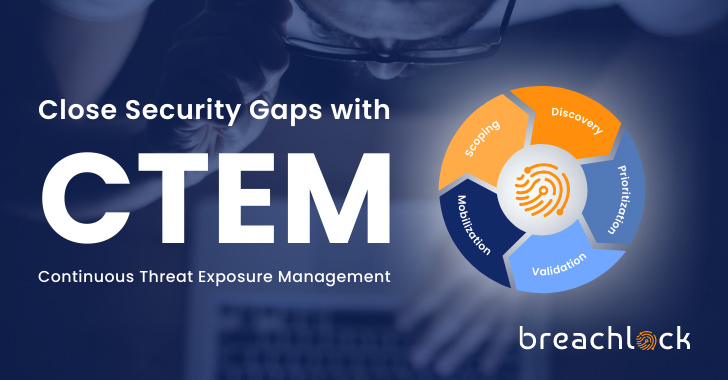
A CTEM system is structured into five unique still interconnected stages, which will have to be executed in a cyclical way: defining the scope, uncovering vulnerabilities, ranking priorities, verifying results, and initiating motion.
These levels aid a thorough comprehending of the organization’s cyberthreat landscape and empower security teams to take well-educated, decisive steps. The mobilization period of the CTEM method focuses on prioritizing vulnerabilities and threats dependent on the criticality of assets, making certain swift remediation, and incorporating seamless workflows for DevSecOps groups.
When carried out correctly, a CTEM software can prevent security incidents and breaches, expedite risk reduction, and enhance total security maturity. Important capabilities and capabilities of a strong CTEM system consist of:
- Automatic discovery of property and management of vulnerabilities
- Ongoing vulnerability assessment of danger exposures in just the attack floor
- Security validation to get rid of wrong positives and assurance precision
- Attaining visibility into the attacker’s perspective and opportunity avenues of attack
- Prioritizing remediation efforts and integrating them with DevSecOps workflows
Start out Your CTEM Plan Nowadays
Security executives call for continuous Danger Publicity Administration remedies that increase, help, and broaden their in-house team’s capabilities to neutralize threats at their origin, blocking expensive and harming security breaches.
By way of the advanced enhancement of CTEM, CISOs and security leaders can undertake a proactive, multi-layered approach to combat cyber-attacks, making sure a prioritized and successful approach. This comprehensive established of abilities equips groups with strong programmatic resources that can substantially diminish cyber dangers in true-time while continuously increasing security benefits around the long time period.
If you are interested in learning far more about making a planet-class solution to closing security gaps with a Continual Risk Exposure Management software, contact BreachLock, the Worldwide Chief in Penetration Tests Providers, for a discovery simply call today.
Identified this article attention-grabbing? Stick to us on Twitter and LinkedIn to read far more unique written content we post.
Some areas of this report are sourced from:
thehackernews.com

 BlackByte 2.0 Ransomware: Infiltrate, Encrypt, and Extort in Just 5 Days
BlackByte 2.0 Ransomware: Infiltrate, Encrypt, and Extort in Just 5 Days