Validate security consistently throughout your comprehensive stack with Pen Testing as a Support.
In modern contemporary security functions heart (SOC), it’s a fight among the defenders and the cybercriminals. Each are applying instruments and experience – nevertheless, the cybercriminals have the factor of surprise on their aspect, and a host of techniques, tactics, and methods (TTPs) that have evolved. These external menace actors have now been even more emboldened in the period of AI with open up-source applications like ChatGPT.
With the probable of an attack primary to a breach inside minutes, CISOs now are hunting to get ready all methods and assets for cyber resilience and quick response when needed.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
With equipment and abilities to validate security continually – which include penetration testing as a service – DevSecOps teams can remediate critical vulnerabilities quickly owing to the easy accessibility to tactical help to the teams that require it the most. This provides the SOC and DevOps teams tools to that eliminate fake positives, validate findings, and streamline remediation and incident response. This efficient expenditure presents a game-point advantage that provides back again time to the SOC by minimizing events, incidents, and breaches that have to have the SOC to detect and answer.
The Require to Consistently Validate Security Currently
Continually validating an organization’s security is foundational in a cybersecurity plan to satisfy various compliance requirements, industry rules, and federal mandates. Corporations need to deliver proof with validated artifacts and certified, impartial penetration tests reports that their devices and in general environments consistently satisfy the demands the firm has established for governance, risk, and compliance.
In addition, the benefits of continual validation combined with penetration screening can be a drive multiplier for audit-readiness, incident preparedness, and fortified defenses.
As security leaders seek new alternatives to increase security results and reduce breaches, they are hunting at the screening aspect to strengthen compliance when validating security. With this Cyber Security Validation in location, every little thing functions collectively as a entire-stack remedy. This new answer presents an exit strategy from legacy pentesting alternatives for a additional sophisticated risk management answer that accelerates results for present-day contemporary SOC.
The Difficulty with Conventional Penetration Testing
Legacy penetration tests answers are continue to making use of guide tests methods regardless of the availability of modern day technology, like AI and automation.
Additionally, traditional penetration testing has traditionally left DevOps in the dark. Although integrating DevOps remediation in just the lifecycle of the true penetration take a look at just helps make good small business perception – the possibility is overlooked when functioning with legacy suppliers. This method results in persistent delays, improved prices, and profits reduction – all the whilst security threats and compliance vulnerabilities that were being identified through the penetration check are still left unnecessarily uncovered. The evident missed option is distinct – specially when security leaders can pursue a greater way.
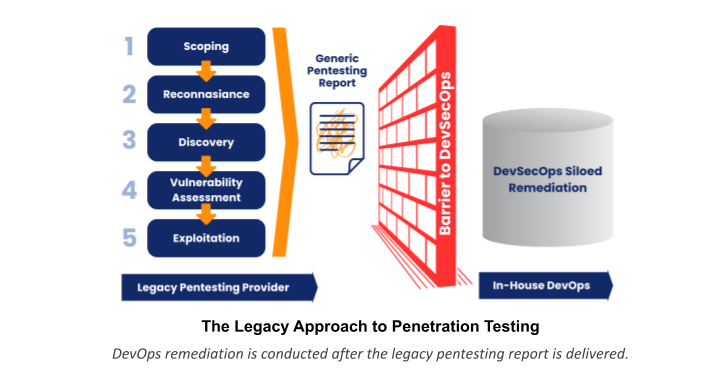
When a penetration tester discovers a critical vulnerability – shouldn’t DevOps be alerted appropriate away? Security leaders are entitled to a far better alternative from their penetration screening investments.
What is Pen Screening as a Services (PTaaS)?
One of the most thrilling innovative approaches right now for security and technology leaders today is the augmented capabilities accessible by a competent Pentesting as a Service (PTaaS) platform and support service provider.
PTaaS is a present day tactic to providing penetration testing providers. It utilizes a mixture of manual human-led pentesting, AI, and automation applications and tactics that speed up pentesting without the need of phony positives. This resolution is getting momentum, as it will help mitigate the cybersecurity capabilities gap currently being confronted by security leaders at a international amount. PTaaS allows technology and security leaders tap into a treasure trove of expertise to optimize their pen tests investments. With skilled, accredited penetration testers offered on-demand, PTaaS shoppers can faucet into the talent they need to perform a penetration test at any time – without the included cost of employing costly security practitioners.
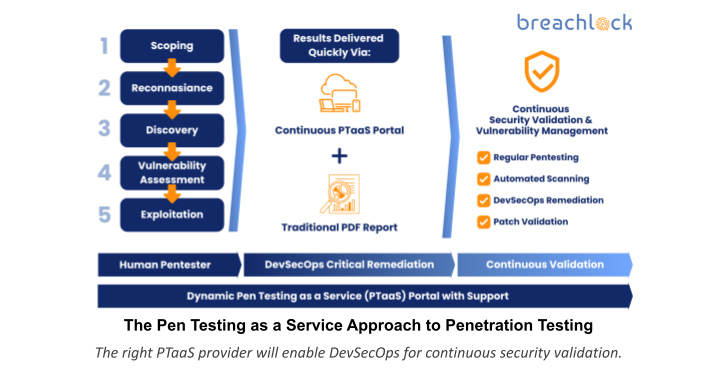
How PTaaS Is effective to Validate Security Continually
Somewhat than a linear method wherever a legacy pen examination is delivered and the in-house DevOps staff can take on the recommended remediations following the pen check concludes, PTaaS integrates DevOps remediation into the lifecycle of just about every penetration check. This permits a DevSecOps testing solution to managing cybersecurity risk – the favored tactic by CISOs to strengthen security maturity and cyber resilience.
In addition, the correct PTaaS provider will offer ongoing vulnerability administration benefits extended after the pen exam has concluded inside of the consumer portal hosted by using a cloud system that contains patch retesting and automatic vulnerability scanning. These positive aspects facilitate group collaboration with the PTaaS supplier as they handle the PTaaS equipment within the platform that supply ongoing security validation.
PTaaS Gains Spelled out
As organizations carry on to depend on technology for everyday security operations, it is important to have a comprehensive understanding of opportunity security vulnerabilities. Pen Testing as a Assistance (PTaaS) provides CISOs the capabilities they need to have to carry out constant pen tests to uncover weaknesses in networks, purposes, and cloud devices from a accredited 3rd party that presents steady security tests, vulnerability scanning, and insights on critical hazards.
Fast Benefits of PTaaS
The largest profit that CISOs can assume from picking the proper PTaaS expense is viewing security outcomes enhanced throughout groups as they get unbiased penetration testing executed by in-house, qualified human authorities employing marketplace-conventional methodologies, chopping edge technology, and an sophisticated cloud pentesting platform to take care of every single PTaaS engagement.
The PTaaS product delivers added immediate advantages, which include the next rewards:
- Agility
- Additional price-efficient than standard in-house penetration tests
- Quicker scheduling, testing effectiveness, and report execution
- API integrates with DevOps ticketing administration units
- Accuracy
- Protected cloud system offers visibility of check effects
- Licensed penetration testers perform comprehensive-stack penetration assessments
- AI and automation improve security tests efficiency
- Human testers validate automatic outcomes and security discoveries
- Confirmed Zero untrue positives
- Lessened Complete Charge of Possession (TCO)
- Enhances security outcomes and compliance-readiness affordably
- Remove duplicative vulnerability scanning and screening technologies in the security tech stack
- Switch conventional pentesting solutions with PTaaS steady security testing capabilities, functions, and benefits
- Scalability
- Remove the DevOps silo of remediation
- Real-time communications are bundled with shopper accessibility to penetration testers
- Buy pen tests on-demand from customers and when essential
Long Phrase Advantages of PTaaS
Above time, when PTaaS is included into a in depth security technique, security leaders can significantly progress an organization’s defenses towards cyber threats and strengthen overall cyber resilience.
The extensive-phrase benefits of PTaaS delivery in your firm are significant, together with the benefits as follows:
- Expense Financial savings
- Outsource the end-to-end aspects of the pentesting approach, which includes protecting against opportunity scope creep
- Constant Security Validation
- Retain Security and DevOps groups continue to be on top rated of security and compliance and enables them to speedily reply to new vulnerabilities
- Visibility into the Adversary’s Perspective
- Get an accurate report of what adversaries can see uncovered in the client’s techniques with an aim and neutral viewpoint
- In-House Staff Extension
- Tap into abilities and means lacking in-house
- Enhanced Security Results
- Recognize challenges, exposures, and weaknesses to remediate now and validate with retesting above time
- Governance, Risk, and Compliance Pentesting Management
- Implement compliance necessities for critical laws by conducting regimen PCI-DSS pentesting, HIPAA Pentesting and GDPR Screening
- Built-in DevSecOps Remediation
- Increase remediation moments with DevSecOps remediation built-in in the course of all phases of the pen check, which include early discovery
- Total-Stack Visibility Throughout Units
- See vulnerabilities by risk and criticality across complete-stack programs, together with purposes, devices, and networks
- Improved Team Workflows
- Increase the velocity of security teams and other departments inside the enterprise with integrations for workflow ticketing
- Ability to Begin the Following Pentest Speedy
- Start the subsequent penetration exam swiftly, and decrease backlogs that are holding back income-creating tasks
The Suitable PTaaS Resolution for Constant Security Validation
Like some other newer offensive security classes, PTaaS has created a ton of interest swiftly – first with CISOs, and now, a lot more a short while ago with item owners and other developers with a stake in the DevSecOps method. Obviously, this has attracted a host of new solutions adding to the legacy alternatives obtainable – generating the ultimate range of your favored PTaaS supplier additional complicated.
In contrast to late entrants to the PTaaS market, third party security provider vendors, like BreachLock, are foremost the Pen Testing as a Assistance group. With an impressive continual security validation answer and in-house security authorities and penetration testers, BreachLock is a proven PTaaS service provider that is fast, reliable, and reasonably priced. BreachLock gives CIOs and CISOs piece of thoughts with a new way to satisfy their security validation, pentesting, and compliance needs in fifty percent the time for 50 % the price tag of classic options. Interested in finding out extra? E-book a discovery contact with BreachLock to see how their award-profitable, analyst identified PTaaS option can get the job done for you right now.
Identified this report exciting? Follow us on Twitter and LinkedIn to browse more unique articles we write-up.
Some elements of this write-up are sourced from:
thehackernews.com


 U.K. Electoral Commission Breach Exposes Voter Data of 40 Million Britons
U.K. Electoral Commission Breach Exposes Voter Data of 40 Million Britons