A new ongoing malware marketing campaign has been noticed distributing three diverse stealers, this sort of as CryptBot, LummaC2, and Rhadamanthys hosted on Written content Supply Network (CDN) cache domains because at minimum February 2024.
Cisco Talos has attributed the action with average confidence to a threat actor tracked as CoralRaider, a suspected Vietnamese-origin team that arrived to gentle earlier this month.
This evaluation is dependent on “a number of overlaps in tactics, techniques, and processes (TTPs) of CoralRaider’s Rotbot marketing campaign, together with the original attack vector of the Windows Shortcut file, intermediate PowerShell decryptor and payload obtain scripts, the FoDHelper method utilized to bypass Consumer Obtain Controls (UAC) of the victim machine,” the business claimed.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

Targets of the marketing campaign span a variety of business enterprise verticals throughout geographies, like the U.S., Nigeria, Pakistan, Ecuador, Germany, Egypt, the U.K., Poland, the Philippines, Norway, Japan, Syria, and Turkey.
Attack chains entail customers downloading information masquerading as film files through a web browser, boosting the possibility of a massive-scale attack.
“This danger actor is working with a Written content Shipping Network (CDN) cache to retail store the destructive information on their network edge host in this campaign, staying away from request hold off,” Talos scientists Joey Chen, Chetan Raghuprasad, and Alex Karkins mentioned. “The actor is making use of the CDN cache as a obtain server to deceive network defenders.”
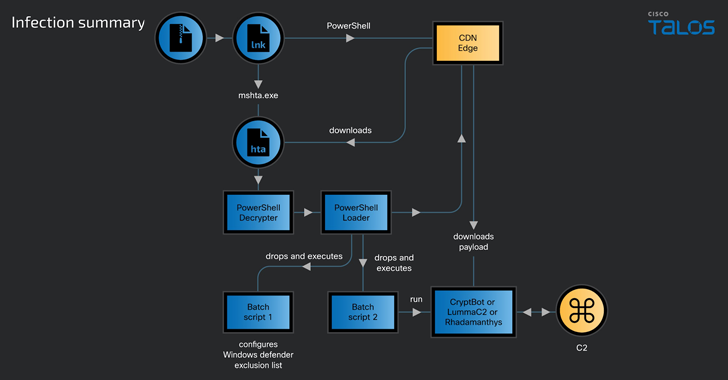
The initial access vector for the drive-by downloads is suspected to be phishing email messages, utilizing them as a conduit to propagate booby-trapped links pointing to ZIP archives containing a Windows shortcut (LNK) file.
The shortcut file, in change, operates a PowerShell script to fetch a upcoming-phase HTML application (HTA) payload hosted on the CDN cache, which subsequently operates Javascript code to start an embedded PowerShell loader that takes actions to fly less than the radar and in the end downloads and operates a single of the 3 stealer malware.

The modular PowerShell loader script is intended to bypass the Consumer Accessibility Controls (UAC) in the victim’s machine employing a acknowledged system termed FodHelper, which has also been place to use by Vietnamese danger actors joined to an additional stealer regarded as NodeStealer that is capable of thieving Fb account facts.
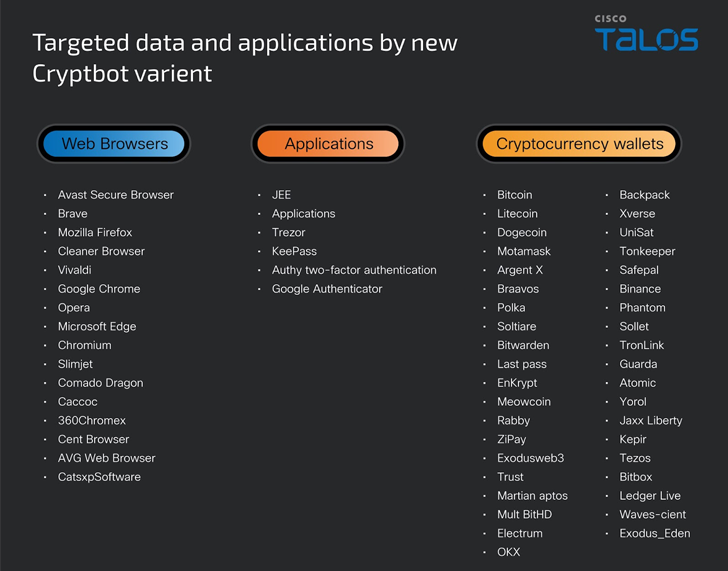
The stealer malware, regardless of what is deployed, grabs victims’ data, these as system and browser data, credentials, cryptocurrency wallets, and money information.
What is noteworthy about the campaign is that it utilizes an updated version of CryptBot that packs in new anti-analysis procedures and also captures password supervisor application databases and authenticator software facts.
Uncovered this post attention-grabbing? Adhere to us on Twitter and LinkedIn to read additional exclusive articles we put up.
Some parts of this report are sourced from:
thehackernews.com

 Apache Cordova App Harness Targeted in Dependency Confusion Attack
Apache Cordova App Harness Targeted in Dependency Confusion Attack