Researchers have disclosed aspects of two critical security vulnerabilities in Control Web Panel that could be abused as element of an exploit chain to attain pre-authenticated distant code execution on afflicted servers.
Tracked as CVE-2021-45467, the issue problems a scenario of a file inclusion vulnerability, which takes place when a web application is tricked into exposing or working arbitrary files on the web server.
Manage Web Panel, formerly CentOS Web Panel, is an open-source Linux control panel software utilised for deploying web hosting environments.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

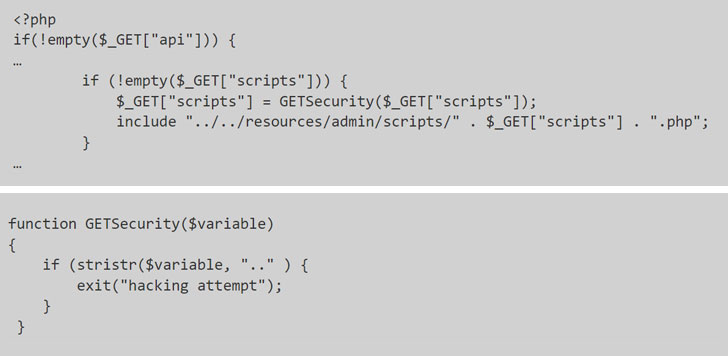
Specifically, the issue arises when two of the unauthenticated PHP webpages made use of in the application — “/consumer/login.php” and “/person/index.php” — are unsuccessful to sufficiently validate a route to a script file, according to Octagon Security’s Paulos Yibelo, who found and reported the flaws.
This indicates that in get to exploit the vulnerability, all an attacker has to do is to change the involve assertion, which is utilized to incorporate the information of just one PHP file into an additional PHP file, to inject malicious code from a remote source and reach code execution.
Apparently, whilst the application had protections in put to flag initiatives to swap to a dad or mum listing (denoted by “..”) as a “hacking attempt” it did nothing at all to stop the PHP interpreter from accepting a specially crafted string such as “.$00.” and efficiently attaining a full bypass.
This not only allows a lousy actor to entry restricted API endpoints, it can be employed in conjunction with an arbitrary file produce vulnerability (CVE-2021-45466) to acquire whole remote code execution on the server as follows —
- Deliver a null byte run file inclusion payload to add malicious API essential
- Use API crucial to create to a file (CVE-2021-45466)
- Use move #1 to involve the file we just wrote into (CVE-2021-45467)
Pursuing liable disclosure, the flaws have considering the fact that been dealt with by the CWP maintainers along with updates delivered before this month.
Uncovered this post attention-grabbing? Abide by THN on Facebook, Twitter and LinkedIn to study much more special material we put up.
Some components of this short article are sourced from:
thehackernews.com



 The Internet’s Most Tempting Targets
The Internet’s Most Tempting Targets